Network Management Articles:
OpManager - Network Monitoring & Management
Boost Network Security and Efficiency with Intell…
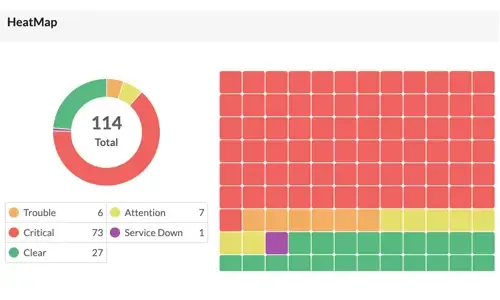
Network alerts are vital for maintaining your network's health, efficiency, and security, ensuring seamless daily operations. They act as an early warning system, alerting you to potential issues bef…

Netflow
Bandwidth Detective: Uncover Hidden Traffic and E…
In this article, we explore the core principles of bandwidth management and examine how modern network monitoring technologies can assist in maintaining network efficiency. In particular, we look at…

ManageEngine Firewall Analyzer
Discover the Ultimate Firewall Management Tool: 7…
Firewall security management is a combination of monitoring, configuring, and managing your firewall to make sure it runs at its best to effectively ward off network security threats. In this article…

Netflow
Complete Guide to Netflow: How Netflow & its Comp…
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive into the technical details of how the Netflow protoco…
Featured Subcategories:
Network Protocol Analyzer Articles:
Network Protocol Analyzers
Introducing Colasoft Unified Performance Manageme…
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, quality, fault, and security issues based on business…
Network Protocol Analyzers
How to Detect SYN Flood Attacks with Capsa Networ…
This article explains how to detect a SYN Flood Attack using an advanced protocol analyser like Colasoft Capsa. We’ll show you how to identify and inspect abnormal traffic spikes, drill into captured…
Network Protocol Analyzers
How to Detect P2P (peer-to-peer) File Sharing, To…
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing processes that not only consumes valuable bandwidth, but…
Network Protocol Analyzers
How To Detect ARP Attacks & ARP Flooding With Col…
ARP attacks and ARP flooding are common problems small and large networks are faced with. ARP attacks target specific hosts by using their MAC address and responding on their behalf, while at the sam…
Virtualization & VM Backup:
Virtualization & VM Backup
How to Fix VMware ESXi Virtual Machine 'Invalid S…
In this article, we'll show you how to deal with VMs which are reported to have an Invalid Status as shown in the screenshot below. This is a common problem many VMware and System Administr…
Virtualization & VM Backup
How to Enable or Disable SSH on VMware ESXi via W…
SSH access to VMware’s ESXi server is by disabled by default however there are many reasons where SSH might be required. VMware and System administrators often find the need to perform advanced admin…
Virtualization & VM Backup
5 Most Critical Microsoft M365 Vulnerabilities Re…
Microsoft 365 is an incredibly powerful software suite for businesses, but it is becoming increasingly targeted by people trying to steal your data. The good news is that there are plenty of ways adm…
Virtualization & VM Backup
FREE Webinar - Fast Track your IT Career with VMw…
Everyone who attends the webinar has a chance of winning a VMware VCP course (VMware Install, Config, Manage) worth $4,500!
Climbing the career ladder in the IT industry is usually dependent on one…
Firewall Articles:
Palo Alto Networks
Palo Alto Firewall Configuration Options. Tap Mod…
Our previous article explained how Palo Alto Firewalls make use of Security Zones to process and enforce security policies. This article will explain the different configuration options for physical…
Palo Alto Networks
The Benefits of Palo Alto Networks Firewall Singl…
What makes Palo Alto Networks Next-Generation Firewall (NGFW) so different from its competitors is its Platform, Process and Architecture. Palo Alto Networks delivers all the next generation firewall…
Palo Alto Networks
Introduction to Palo Alto Next-Generation Network…
During the past decade, we’ve seen the global IT security market flooded with new network security and firewall security appliances. New vendors emerging into the market while existing well-known ven…
Palo Alto Networks
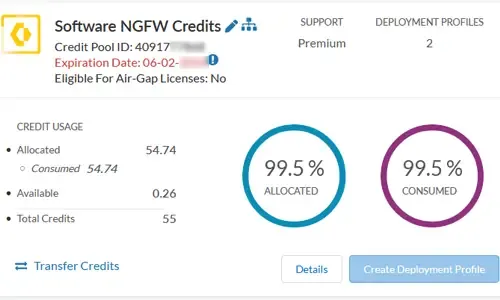
The Ultimate Guide to Palo Alto Networks Software…
Discover the ins and outs of using Palo Alto Networks’ Software NGFW (Flex) credits to seamlessly renew your cloud-based or virtualized software NGFW devices! Dive into this exciting guide where we u…
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Top Picks
Cisco Routers
Cisco Type 7 Password Decrypt / Decoder / Crack Tool
The Firewall.cx Cisco Password Decoder Tool (see below) provides readers with the ability to decrypt 'Type 7' cisco passwords.
For security reasons…
Cisco Switches
Password Recovery / Password Reset Procedure for Catalyst 3750-X & 3560-X Switches - Single or Stack Member Configuration
This article shows how to reset a password on a Cisco Catalyst 3750-X (stacked or single unit) and Cisco Catalyst 3560-x switch without losing its st…
Cisco Switches
Cisco Catalyst Err-disabled Port State, Enable & Disable Autorecovery Feature
Errdisable is a feature that automatically disables a port on a Cisco Catalyst switch. When a port is error disabled, it is effectively shut dow…
Windows Servers
Hyper-V Best Practices - Replica, Cluster, Backup Advice
Hyper-V has proven to be a very cost effective solution for server consolidation. Evidence of this is also the fact that companies are beginning to m…
















