Palo Alto: Top Picks
Palo Alto Networks
Palo Alto Networks Firewall - Web & CLI Initial C…
This article is the second-part of our Palo Alto Networks Firewall technical articles. Our previous article was introduction to Palo Alto Networks Fi…
Palo Alto Networks
Palo Alto Firewall Configuration Options. Tap Mod…
Our previous article explained how Palo Alto Firewalls make use of Security Zones to process and enforce security policies. This article will explain…

Palo Alto Networks
Configuring QoS on Palo Alto Firewalls: Class-bas…
This article’s purpose is to help you quickly master Palo Alto QoS concepts and learn to configure QoS on Palo Alto Firewalls in a simple and efficie…
Palo Alto Networks
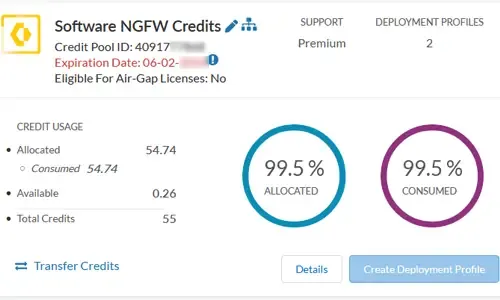
The Ultimate Guide to Palo Alto Networks Software…
Discover the ins and outs of using Palo Alto Networks’ Software NGFW (Flex) credits to seamlessly renew your cloud-based or virtualized software NGFW…
Featured Subcategories:
SD-WAN & SASE Articles:
SASE & SD-WAN Networks
Converged SASE Backbone – How Leading SASE Provid…
Global connectivity is top of mind for many IT teams at organizations of all sizes. We are currently in the middle of a dramatic shift in business an…
SASE & SD-WAN Networks
Check Point Software and Cato Networks Co-Founder…
By: Shlomo Kramer, Check Point Software & Cato Networks Co-Founder
As one of the founders of Check Point Software and more recently Cato Network…
SASE & SD-WAN Networks
MPLS vs. SD-WAN vs. Internet vs. Cloud Network. C…
The Wide Area Network (WAN) is the backbone of the business. It ties together the remote locations, headquarters and data centers into an integrated…
SASE & SD-WAN Networks
WAN Optimization vs SD WAN Networks. Today’s Chal…
Enterprises have been successfully running WAN optimization appliances at their many distributed sites for years. The devices have done a good job of…
F5 Networks:
Network Protocol & Firewall Analyzers:
Network Protocol Analyzers
How To Detect ARP Attacks & ARP Flooding With Col…
ARP attacks and ARP flooding are common problems small and large networks are faced with. ARP attacks target specific hosts by using their MAC addres…
Network Protocol Analyzers
Improve Network Analysis Efficiency with Colasoft…
Troubleshooting network problems can be a very difficult and challenging task. While most IT engineers use a network analyzer to help solve network p…
Network Protocol Analyzers
Introducing Colasoft Unified Performance Manageme…
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, quali…
Network Protocol Analyzers
How to Reconstruct HTTP Packets/Data & Monitor HT…
HTTP reconstruction is an advanced network security feature offered by nChronos version 4.3.0 and later. nChronos is a Network Forensic Analysis appl…
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Web Vulnerability Application Scanners & VPN Services
VPN Services & Guides
What is a VPN? VPNs for Beginners - Everything You Ne…
What is a VPN?
VPN (Virtual Private Network) is a well-known acronym amongst regular internet users. Initially used within businesses to securely connect…
Web Application Vulnerability Scanners
Web Application Security Best Practices that Help in S…
Successful web application attacks and the data breaches that are resulting from these attacks, have now become everyday news, with large corporations bei…
Web Application Vulnerability Scanners
Differences between Network & Web Application Security…
According to Wikipedia, security is defined as the degree of resistance to, or protection from, harm. It applies to any vulnerable and valuable asset whic…
Web Application Vulnerability Scanners
Scan and Generate Firewall Rules to Secure your Websit…
ModSecurity is a very popular open-source web application Firewall used to protect webservers and websites from vulnerability attacks, exploits, unauthori…















