Suggested Articles:

Network Fundamentals
Network Unicast - Its role and Importance
Unicast is a communication method used in computer networking where data is sent from a single sender to a specific destination device. In this…
Ethernet Protocol, CSMA/CD, Collisions
The Ethernet II Frame Format
The following is a description of the frame format described by the original Ethernet Version II specification as released by DEC, Intel, and Xerox…
TCP - UDP Protocol Analysis
TCP Header Anaylsis - Section 5: TCP Window Size…
Our fifth section contains some very interesting fields that are used by the TCP transport protocol. We see how TCP helps control how much data is tr…
IP Protocol
IP Protocol - Part 1: Binary & The Internet Proto…
To understand the Internet Protocol, we need to learn and understand Binary. It is very important to know and understand Binary because part of the I…
Featured Subcategories:
Netflow Articles:

Netflow vs SNMP. Two Different Approaches to Netw…
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ne…

Bandwidth Detective: Uncover Hidden Traffic and E…
In this article, we explore the core principles of bandwidth management and examine how modern network monitoring technologies can assist in maintain…

Complete Guide to Netflow: How Netflow & its Comp…
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive int…

Netflow: Monitor Bandwidth & Network Utilization…
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, applic…
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
VLAN Networks
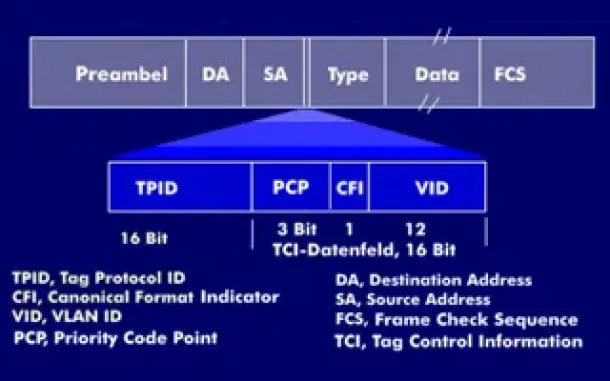
VLAN Tagging - Understanding VLANs Ethernet Frames
We mentioned that Trunk Links are designed to pass frames (packets) from all VLANs, allowing us to connect multiple switches together and independently co…

VLAN Networks
VLANs - Access & Trunk Links
If you've read our previous article The VLAN Concept - Introduction to VLANs then you should feel comfortable with terms such as 'VLAN', 'Stati…

VLAN Networks
VTP Pruning
VTP (VLAN Trunking Protocol) pruning is a feature that is used in Cisco switches to reduce unnecessary traffic in VLAN (Virtual Local Area Network) trunks…
VLAN Networks
VTP Protocol - In-Depth Analysis
The previous article introduced the VTP protocol, we examined how it can be used within a network, to help manage VLANs and ease the administrative overhe…
Routing
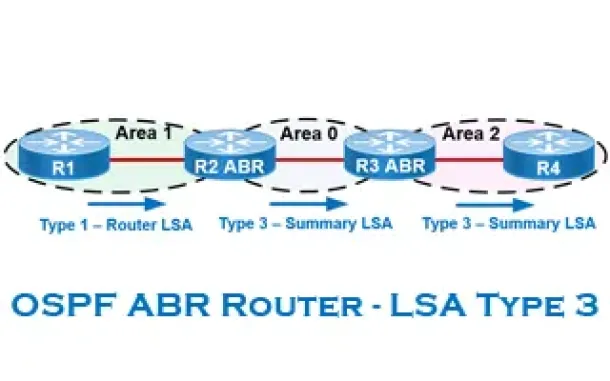
OSPF - Part 6: OSPF LSA Types - Purpose and Function o…
Our previous article explained the purpose of Link State Update (LSU) packets and examined the Link State Advertisement (LSA) information contained within…
Routing
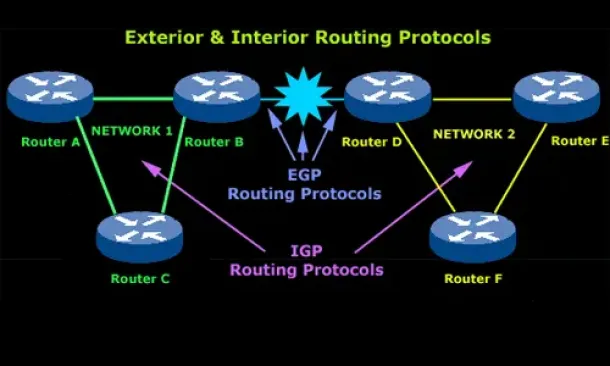
Hybrid Routing Protocols - Advantages and Disadvantage…
Hybrid routing protocols are a combination of distance-vector and link-state routing protocols, and are used to provide a more efficient and scalabl…
Routing
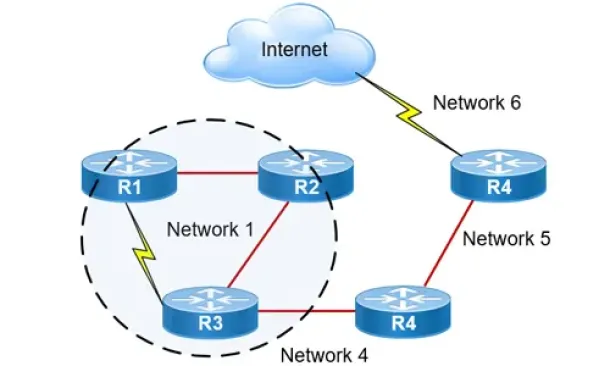
Introduction to Routing Protocols
Distance Vector, Link State RIP, IGRP, EIGRP, OSPF
Routing protocols were created for routers. These protocols have been designed to allow the exchange…
Routing
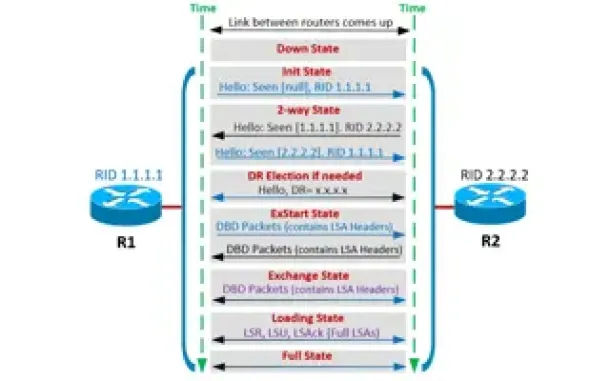
OSPF - Part 4: OSPF Neighbor States – OSPF Neighbor Fo…
This is the third article of our OSPF series which analyzes the different OSPF States routers go through during the OSPF discovery and neighbor forming pr…
Windows Servers
Active Directory Tombstone Lifetime Modification
Tombstone is a container object that contains the deleted objects from Active Directory. Actually when an object is deleted from Active Directory, it is n…
Cisco Routers
Configuring Cisco SSL VPN AnyConnect (WebVPN) on Cisco…
Our Web SSL VPN article written back in 2011 introduced this new wave of VPN services. This article extends the topic by covering the installation a…
Windows Servers
Free Webinar: Scripting & Automation in Hyper-V withou…
System Center Virtual Machine Manager (SCVMM) provides some great automation benefits for those organizations that can afford the hefty price tag. However…
SASE & SD-WAN Networks
SD-WAN is the Emerging, Evolving Solution for the Bran…
A lot has changed in how people work during the past twenty years. Co-working spaces, mobility, and the cloud now are common. Businesses are spread out an…
















