Patch Manager Plus
Patch Windows, Mac, Linux, and 1100+ third-party applications from a single console!

OpManager: Network & DC Monitoring
Monitor & Manage Network, Datacenters, endpoints & more.
Latest Articles
Endpoint Security Under Pressure: How to Stay Ahead of Modern Cyber Threats
 Cyberattacks no longer happen on a predictable schedule. Ransomware can cripple systems within minutes, while zero-day vulnerabilities are often exploited before patches even exist. With remote work, BYOD policies, cloud applications, and growing endpoint fleets now the norm, IT and security teams are under constant pressure to stay ahead of evolving threats.
Cyberattacks no longer happen on a predictable schedule. Ransomware can cripple systems within minutes, while zero-day vulnerabilities are often exploited before patches even exist. With remote work, BYOD policies, cloud applications, and growing endpoint fleets now the norm, IT and security teams are under constant pressure to stay ahead of evolving threats.
The challenge is not a lack of effort. It is having the right visibility, insights, and tools to respond quickly and effectively.
The Endpoint Security for Dummies guide is designed for endpoint administrators, security engineers, IT managers, and CISOs looking for practical ways to strengthen endpoint security without adding unnecessary complexity.
Inside the guide, you’ll learn how modern attackers identify weaknesses and target endpoint environments, how to proactively detect vulnerabilities, and how to build layered protection across devices, identities, networks, and sensitive data.
The guide also explores how AI-driven detection and response can help security teams identify threats faster, automate investigations, and improve incident response capabilities before incidents escalate.
You’ll also gain access to:
- Practical security checklists for CISOs and IT administrators
- Strategies for defending against advanced threats such as fileless malware and ransomware-as-a-service (RaaS)
- Best practices for building a security-first culture across the organisation
- Actionable frameworks to strengthen endpoint resilience and reduce risk exposure
 Whether you are starting your endpoint security journey or refining an existing strategy, the right knowledge can make a measurable difference. This guide provides practical, actionable insights that security teams can apply immediately.
Whether you are starting your endpoint security journey or refining an existing strategy, the right knowledge can make a measurable difference. This guide provides practical, actionable insights that security teams can apply immediately.
Detecting Insider Threats and Shadow IT Through Firewall Log Analysis
 This article explores the key indicators of insider threats and shadow IT hidden within firewall logs, the behavioral patterns security teams should monitor, and how advanced firewall analytics can help IT and security teams detect abnormal activity, improve application visibility, and identify emerging security risks before they impact business operations.
This article explores the key indicators of insider threats and shadow IT hidden within firewall logs, the behavioral patterns security teams should monitor, and how advanced firewall analytics can help IT and security teams detect abnormal activity, improve application visibility, and identify emerging security risks before they impact business operations.
Key topics:
- Why insider threats and shadow IT are hard to detect
- Key indicators of insider threats and shadow IT in firewall traffic and session data
- How SaaS adoption and unmanaged applications expand the enterprise attack surface
- Best practices for identifying abnormal user, application, and outbound traffic behavior
- How firewall log analysis helps uncover hidden security and compliance risks
- Using ManageEngine Firewall Analyzer to improve visibility, detect anomalies, and strengthen network security monitoring
- Summary
Related Articles:
- 7 Essential Firewall Management Strategies for Maximum Security
- Achieving Modern Compliance: Navigate PCI DSS v4.0 with Firewall Analyzer
- Challenges & Solutions to Managing Firewall Rules in Complex Network Environments
- Dealing with Security Audit Challenges: Discovering vulnerabilities, unauthorized access, optimize network security & reporting
- Discover the Ultimate Firewall Management Tool: 7 Essential Features for Unleashing Unrivaled Network Security!
- Ensuring Compliance and Business Continuity in a Hybrid Work Environment
- Master Your Firewall: 6 Expert-Backed Steps to Boost Security, Performance, and Compliance
Firewall Analyzer simplifies firewall auditing, helps identify vulnerabilities and compliance risks before they impact your network.
Why Insider Threats and Shadow IT Are Hard to Detect
Insider threats and shadow IT present a significant detection challenge because they rarely resemble conventional malicious activity. In most cases, there is no obvious exploit attempt, malware signature, or unauthorized access event to trigger immediate concern. Instead, the activity originates from authenticated users, trusted devices, approved applications, and legitimate communication channels already permitted within the organization’s security policies. From the perspective of traditional firewalls and perimeter-based controls, the traffic often appears fully compliant with expected operational behavior.
Free Cybersecurity Essentials 2026 Update: New Security Requirements, MFA, SaaS & Compliance Explained
 Cybersecurity frameworks continue to evolve as organisations face increasingly sophisticated threats. Recent updates to widely adopted baseline security standards are raising the bar—placing stronger emphasis on identity protection, cloud visibility, and endpoint control.
Cybersecurity frameworks continue to evolve as organisations face increasingly sophisticated threats. Recent updates to widely adopted baseline security standards are raising the bar—placing stronger emphasis on identity protection, cloud visibility, and endpoint control.
The latest Cyber Essentials changes introduce stricter requirements that go far beyond traditional perimeter security. Multi-Factor Authentication (MFA) is now mandatory across all user access to cloud services, not just privileged accounts. In addition, SaaS platforms, IaaS environments, and previously overlooked shadow IT systems are now fully in scope. Mobile devices are no longer optional—they must be assessed and secured as part of your environment.
For many organisations, this represents a significant shift. Compliance is no longer a checklist exercise—it requires a clear understanding of your entire attack surface, from endpoints to cloud services. Failure to align with these updates can expose critical gaps, increase risk, and impact audit outcomes.
To help break down these changes and their real-world implications, ManageEngine is hosting a live expert-led session designed specifically for IT and security professionals.
Free to attend – secure your spot now and stay ahead of evolving security standards
What This Webinar Covers
- Key changes in the latest Cyber Essentials framework update
- Why MFA is now critical across all cloud access points
- Expanding security scope: SaaS, IaaS, shadow IT, and mobile devices
- Practical steps to assess your current security posture
- How to prepare for upcoming compliance audits and avoid common pitfalls
- Real-world breach scenarios and lessons learned
Learn from Industry Experts
The session features insights from leading cybersecurity professionals:
- Graham Cluley, internationally recognised cybersecurity speaker, shares real-world attack scenarios and highlights where organisations commonly fall short
- Romanus Raymond Prabhu, Director of Technology at ManageEngine, provides practical guidance on strengthening endpoint security and aligning with modern compliance requirements
Who Should Attend
This webinar is ideal for:
- Network & Security Engineers
- IT Administrators & Infrastructure Teams
- CISOs and Security Leaders
- Compliance & Risk Professionals
- Managed Service Providers (MSPs)
- SMB and enterprise IT decision-makers
Why This Matters
Bandwidth Detective: Uncover Hidden Traffic and Eliminate Network Bottlenecks
 In this article, we explore the core principles of bandwidth management and examine how modern network monitoring technologies can assist in maintaining network efficiency. In particular, we look at how solutions like NetFlow Analyzer empower network administrators with detailed network traffic visibility, enabling them to proactively detect anomalies, analyse bandwidth usage, and resolve network performance issues before they impact users.
In this article, we explore the core principles of bandwidth management and examine how modern network monitoring technologies can assist in maintaining network efficiency. In particular, we look at how solutions like NetFlow Analyzer empower network administrators with detailed network traffic visibility, enabling them to proactively detect anomalies, analyse bandwidth usage, and resolve network performance issues before they impact users.
Key Topics Covered
- Bandwidth Management with Network Analyzer
- Bandwidth Traffic Analysis
- Network Forensics
- Smart Traffic Management
- Proactive Alerts
- Traffic Pattern Analysis
- Summary
Related Articles:
- Complete Guide to Netflow: How Netflow & its Components Work. Netflow Monitoring Tools
- Netflow: Monitor Bandwidth & Network Utilization. Detect LAN, WAN, Wi-Fi Bottlenecks, Unusual Traffic Patterns, Problems and more
- Netflow vs SNMP. Two Different Approaches to Network Monitoring
Get your Bandwidth Detective and start uncovering hidden traffic
With today’s increasingly complex network environments, managing network bandwidth is no longer optional—it is a critical requirement for ensuring stable and efficient operations. Modern networks support a wide range of applications, from real-time communications and cloud services to large-scale data transfers, all competing for limited resources. Without proper visibility and control, network congestion can quickly lead to degraded performance, poor user experience, and potential business disruption.
Effective bandwidth management enables organisations to prioritise critical applications, prevent unnecessary traffic from consuming valuable resources, and maintain consistent network performance across the infrastructure. By implementing the right network monitoring tools and traffic analysis solutions, administrators can gain deep insight into traffic patterns, identify bottlenecks, and make informed decisions to optimise overall performance.
Businesses today rely heavily on advanced network monitoring solutions to maintain operational continuity. These tools play a vital role in proactively identifying issues, strengthening network security, ensuring high availability, supporting scalability, and optimising infrastructure costs. Leveraging flow-based technologies such as NetFlow, administrators can achieve granular visibility into network traffic flows and gain the actionable insights required to effectively manage bandwidth in dynamic IT environments.
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Featured Categories:
Top Picks:
Live discussion: Learn to assess and accelerate y…

Discover the Ultimate Firewall Management Tool: 7…
The Ultimate Guide to Palo Alto Networks Software…
Optimizing Cisco Router Performance: Best Practic…
The Need for a Converged SASE Platform. Converging Network & Security Services with Catonetworks SASE Platform
Security Service Edge (SSE) Limitations & Disadvantages. Protecting all Traffic, Users, Apps, and Services with 360-degree SSE
Understanding Secure Access Service Edge (SASE) and how it integrates with SD-WAN
How To Secure Your SD-WAN. Comparing DIY, Managed SD-WAN and SD-WAN Cloud Services
The VLAN Concept - Introduction to VLANs

VTP Pruning

Static VLANs

Dynamic VLANs
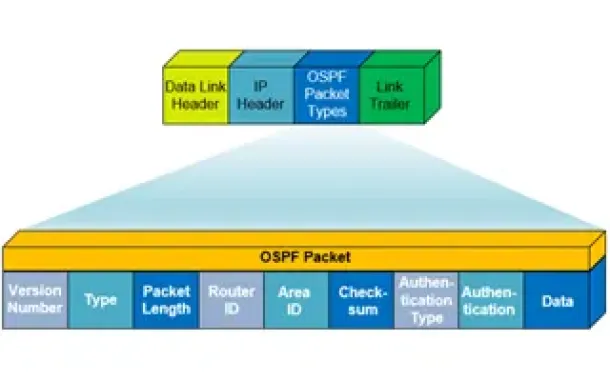
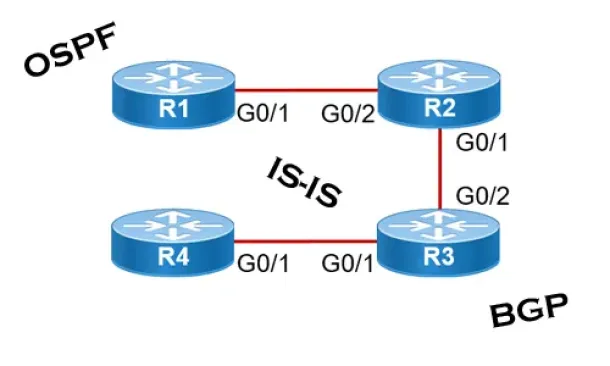
OSPF - Part 1: Introduction, OSPF Packet Structure, OSPF Messages and Characteristics

OSPF - Part 3: OSPF Adjacency & Neighbor Forming Process. OSPF Hello Messages, OSPF Database Updates via Link State Requests (LSR & LSU)
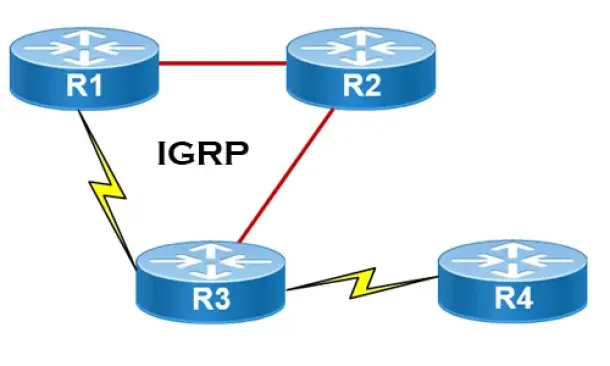
Interior Gateway Protocol - IGRP