Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
Network Switches & Bridges
| Read |
|
Articles:
Hubs & Repeaters
| Read |
|
Articles:
Securing Your Home Network
| Read |
|
Articles:
DoS & DDoS Attacks
| Read |
| Read | |
|
Articles:
Firewall Topologies
| Read |
|
Articles:
Controlling Broadcasts and Multicasts
| Read |
|
Articles:
Network Broadcast
| Read |
| Read | |
| Read | |
|
Articles:
Media Access Control - MAC Addresses
| Read |
|
Articles:
Network Data Transmission
| Read |
|
Articles:
LAN Network Topologies
| Read |
|
Articles:
Introduction To Networking
| Read |
Suggested Articles:
IP Protocol
IP Protocol - Part 3: IP Classes, Network & Host…
This article explains the 'Network-ID' and 'Host-ID' concept found in IP addressing and subnetting. We analyse the structure of IP addresses and netw…
Domain Name System (DNS)
The DNS Protocol - Part 3: DNS Query Message Form…
This section will deal with the analysis of the DNS packets by examining how DNS messages are formatted and the options and variables they contain. T…

Network Fundamentals
Measuring Network Performance: Test Network Throu…
Measuring network performance has always been a difficult and unclear task, mainly because most engineers and administrators are unsure which approac…
ICMP Protocol
ICMP Protocol - Part 2: Echo / Echo Reply (Ping)…
As mentioned in the previous page, an Echo is simply what we networking engineers call a 'ping'. The Echo Reply is, as most would guess, the 'p…
Featured Subcategories:
Netflow Articles:

Netflow vs SNMP. Two Different Approaches to Netw…
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ne…

Complete Guide to Netflow: How Netflow & its Comp…
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive int…

Bandwidth Detective: Uncover Hidden Traffic and E…
In this article, we explore the core principles of bandwidth management and examine how modern network monitoring technologies can assist in maintain…

NetFlow Analyzer: Free Download, Step-by-Step Ins…
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows w…
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
VLAN Networks
The VLAN Concept - Introduction to VLANs
We hear about them everywhere, vendors around the world are constantly trying to push them into every type of network and as a result, the Local Area Netw…
VLAN Networks
VTP Protocol - In-Depth Analysis
The previous article introduced the VTP protocol, we examined how it can be used within a network, to help manage VLANs and ease the administrative overhe…

VLAN Networks
Comparing Traditional Flat & VLAN Networks
Designing and building a network is not a simple job. VLANs are no exception to this rule, in fact they require a more sophisticated approach because of t…

VLAN Networks
VLANs - Access & Trunk Links
If you've read our previous article The VLAN Concept - Introduction to VLANs then you should feel comfortable with terms such as 'VLAN', 'Stati…
Routing
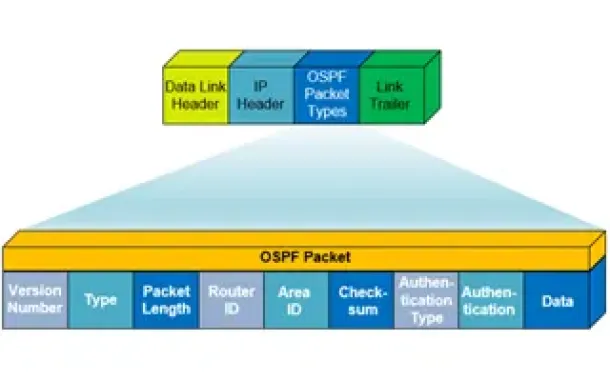
OSPF - Part 1: Introduction, OSPF Packet Structure, OS…
Open Shortest Path First (OSPF) is a popular routing protocol developed for Internet Protocol (IP) networks by the Interior Gateway Protocol (IGP) working…

Routing
OSPF - Part 3: OSPF Adjacency & Neighbor Forming Proce…
This is the thrid article of our 6-part OSPF series (see below) that describes how OSPF routers perform neighbor relationship and adjacency. We’ll examine…
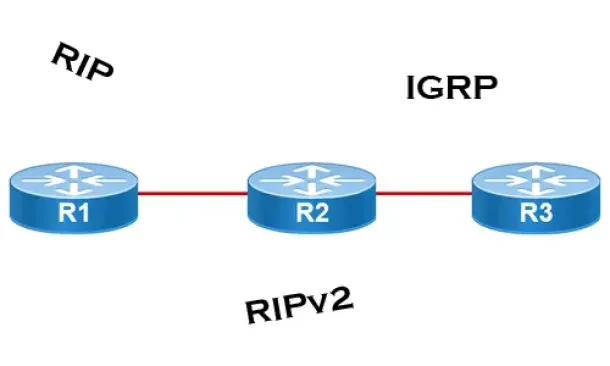
Routing
Distance Vector Routing Protocols
Distance Vector routing protocols use frequent broadcasts (255.255.255.255 or FF:FF:FF:FF) of their entire routing table every 30 sec. on all their interf…
Routing
Link State Routing Protocols
Link State routing protocols do not view networks in terms of adjacent routers and hop counts, but they build a comprehensive view of the overall network…
SASE & SD-WAN Networks
Key Features of a True Cloud-Native SASE Service. Sett…
Secure Access Service Edge (SASE) is an architecture widely regarded as the future of enterprise networking and security. In previous articles we talked a…
Cisco Routers
How To Secure Your Cisco Router Using Cisco AutoSecure…
In today’s complex network environments securing your network routers can be a daunting task, especially when there are so many CLI commands and parameter…
Cisco Switches
Spanning Tree BPDU Guard and Errdisable Interface Auto…
Running Spanning Tree Protocol (STP) in a large network environment can be a challenging task especially when features/enhancements such as BPDU Filter an…
Virtualization & VM Backup
How to Enable or Disable SSH on VMware ESXi via Web GU…
SSH access to VMware’s ESXi server is by disabled by default however there are many reasons where SSH might be required. VMware and System administrators…
















