Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
|
Articles:
Dynamic NAT - Part 2
| Read |
|
Articles:
Dynamic NAT - Part 1
| Read |
|
Articles:
Static NAT - Part 2
| Read |
|
Articles:
Static NAT - Part 1
| Read |
|
Articles:
The Network Address Translation Table
| Read |
| Read | |
Suggested Articles:
Ethernet Protocol, CSMA/CD, Collisions
IEEE 802.3 Interframe Spacing
The IEEE 802.3 specification states that before a station can attempt to transmit on the wire, it must first wait until it has heard 9.6 microseconds…
Network Cabling
Fibre Optic Cables - Single-Mode Multi-Mode - Adv…
In this article, we'll talk about Fiber optic cables and how it has changed the design and implementation of network infrastructures, providing high…
Domain Name System (DNS)
The DNS Protocol - Part 2: DNS Queries & Resoluti…
This section will help you understand how the DNS queries work on the Internet and your home network. There are two ways to use the domain name syste…
ICMP Protocol
ICMP Protocol - Part 2: Echo / Echo Reply (Ping)…
As mentioned in the previous page, an Echo is simply what we networking engineers call a 'ping'. The Echo Reply is, as most would guess, the 'p…
Featured Subcategories:
Netflow Articles:

NetFlow Analyzer: Free Download, Step-by-Step Ins…
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows w…

Bandwidth Detective: Uncover Hidden Traffic and E…
In this article, we explore the core principles of bandwidth management and examine how modern network monitoring technologies can assist in maintain…

Netflow: Monitor Bandwidth & Network Utilization…
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, applic…

Netflow vs SNMP. Two Different Approaches to Netw…
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ne…
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
VLAN Networks
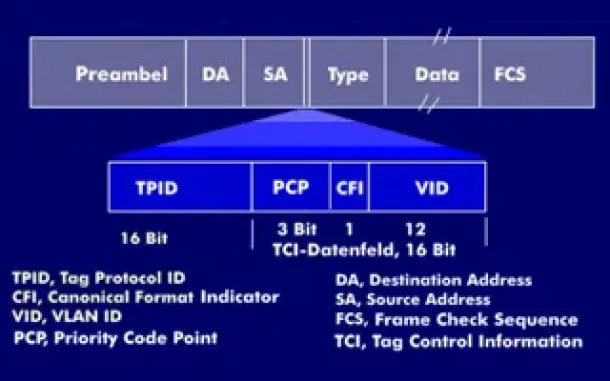
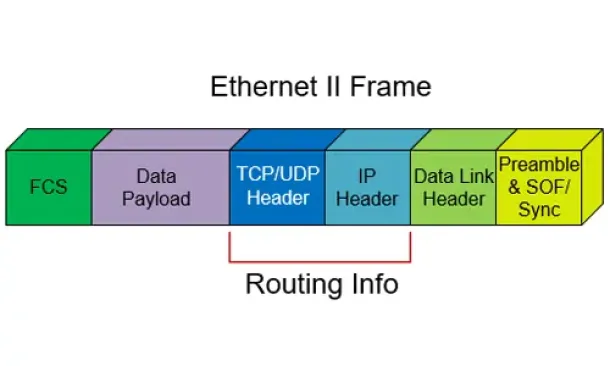
VLAN Tagging - Understanding VLANs Ethernet Frames
We mentioned that Trunk Links are designed to pass frames (packets) from all VLANs, allowing us to connect multiple switches together and independently co…
VLAN Networks
VTP Protocol - In-Depth Analysis
The previous article introduced the VTP protocol, we examined how it can be used within a network, to help manage VLANs and ease the administrative overhe…

VLAN Networks
VTP Pruning
VTP (VLAN Trunking Protocol) pruning is a feature that is used in Cisco switches to reduce unnecessary traffic in VLAN (Virtual Local Area Network) trunks…

VLAN Networks
InterVLAN Routing - Routing between VLAN Networks
This article deals with the popular topic of InterVLAN routing, which is used to allow routing & communication between VLAN networks. Our article anal…
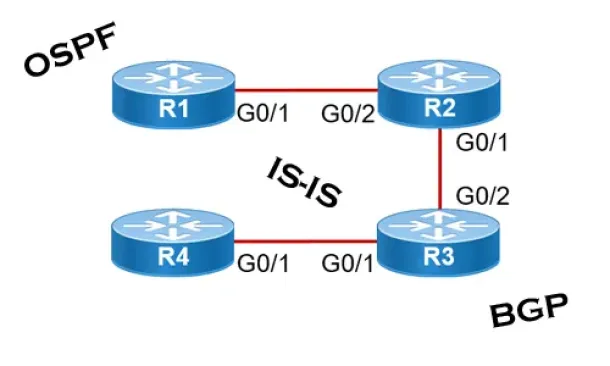
Routing
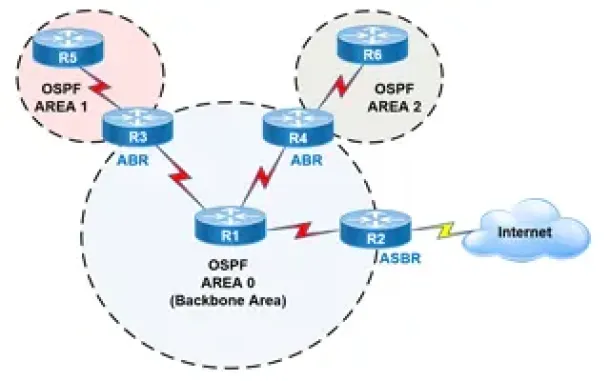
Link State Routing Protocols
Link State routing protocols do not view networks in terms of adjacent routers and hop counts, but they build a comprehensive view of the overall network…
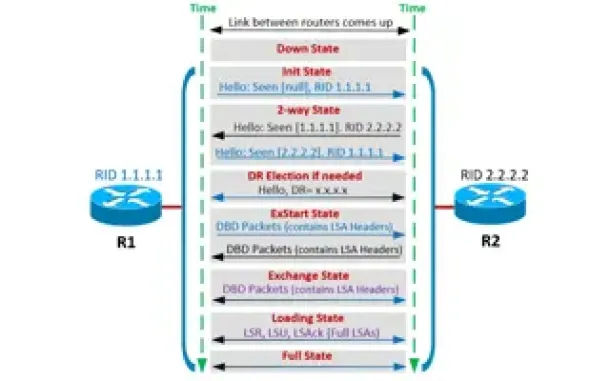
Routing
OSPF - Part 4: OSPF Neighbor States – OSPF Neighbor Fo…
This is the third article of our OSPF series which analyzes the different OSPF States routers go through during the OSPF discovery and neighbor forming pr…
Routing
OSPF - Part 2: How OSPF Protocol Works & Basic Concept…
This article covers basic OSPF concepts and operation. We explain how OSPF works, how OSPF tables are built on an OSPF-enabled router and their purpose (N…
Routing
Routed Protocols
We all understand that TCP/IP, IPX-SPX are protocols which are used in a Local Area Network (LAN) so computers can communicate between with each other and…
Cisco Switches
Installation of a Cisco Catalyst 4507R-E Layer 3 Switch
Driven by our thirst for technical material and experience, we thought it would be a great idea to start presenting various installations of Cisco equipme…
Windows Servers
Configuring Local Group Policy for Windows 2003
Windows 2003 Group Policies allow the administrators to efficiently manage a group of people accessing a resource. Group policies can be used to control b…
Cisco Routers
Cisco Router Password Recovery
Password recovery is a fairly frequently used procedure for administrators and engineers. Even though we usually stack our passwords in some word, excel o…
Palo Alto Networks
How to Register a Palo Alto Firewall and Activate Supp…
This article explains how to register and activate your Palo Alto Firewall Appliance to obtain technical support, RMA hardware replacement, product update…
















