Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
Linux File & Folder Permissions
| Read |
|
Articles:
Advanced Linux Commands
| Read |
|
Articles:
Installing Software On Linux
| Read |
|
Articles:
The Linux Command Line
| Read |
|
Articles:
The Linux File System
| Read |
|
Articles:
Why Use Linux?
| Read |
MS Server Articles:
Windows Servers
Creating a Virtual Machine in Windows Hyper-V. Co…
Our previous articles covered basic concepts of Virtualization along with the installation and monitoring of Windows 2012 Hyper-V. This article takes…
Windows Servers
Download Altaro Free VM Backup & Win a PlayStatio…
We have some exciting news for you today!
Altaro has launched a great contest in celebration of SysAdmin Day on 27th July!
They will be giving away…
Windows Servers
Free Hyper-V eBook - Create, Manage and Troublesh…
With the introduction of Hyper-V on the Windows Server platform, virtualization has quickly become the de facto standard for all companies seeking to…
Windows Servers
Active Directory Tombstone Lifetime Modification
Tombstone is a container object that contains the deleted objects from Active Directory. Actually when an object is deleted from Active Directory, it…
Featured Subcategories:
Virtualization & VM Backup Articles:
Differences Between VMware vSphere, vCenter, ESXi…
In this article we will cover the differences between VMware ESXi, vSphere and vCenter while also explain the features supported by each vSphere edit…
SysAdmin Day 2020 - Get your Free Amazon Voucher…
SysAdmin Day has arrived, and with it, gratitude for all the unsung heroes that 2020 has needed. Your hard work has made it possible for all of us to…

Ultimate Guide: Install Windows 11 on VMware ESXi…
In this article, we’ll show you how to setup or install Microsoft Windows 11 on VMware’s ESXi servers and bypass the Trusted Platform Module version…
World Backup Day with Free Amazon Voucher and Pri…
Celebrate World Backup Day and WIN with Altaro!
We all remember how grateful we were to have backup software when facing so many data loss mishaps…
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Linux - Unix
Understanding Linux File System Quotas - Installation…
When you are running your own web hosting, it is important to monitor how much space is being used by each user. This is not a simple task to be done manu…
Linux - Unix
Finding More Information On The Linux Operating System
Since this document merely scratches the surface when it comes to Linux, you will probably find you have lots of questions and possibly problems. Whether…
Linux - Unix
Linux CentOS - Redhat EL Installation on HP Smart Arra…
This article was written thanks to our recent encounter of a HP DL120 G7 rack mount server equipped with a HP Smart Array B110i SATA Raid controller, need…
Linux - Unix
Linux BIND DNS - Part 1: Introduction To The DNS Datab…
BIND (Berkely Internet Name Domain) is a popular software for translating domain names into IP addresses and usually found on Linux servers. This article…
Popular Topics
Cisco Switches
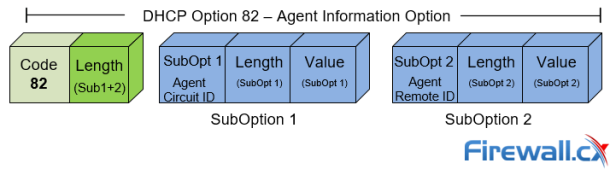
DHCP Option 82 Message Format, Analysis. DHCP Snooping…
This article provides in-depth analysis of DHCP Option 82 (DHCP Relay Agent) which is one of the +180 DHCP Options available to the DHCP protocol and used…
Network Protocol Analyzers
How To Detect ARP Attacks & ARP Flooding With Colasoft…
ARP attacks and ARP flooding are common problems small and large networks are faced with. ARP attacks target specific hosts by using their MAC address and…
Cisco Routers
How To Configure Router On A Stick - 802.1q Trunk To C…
Router-on-a-stick is a term frequently used to describe a setup up that consists of a router and switch connected using one Ethernet link configured as an…
Cisco Routers
How To Configure DHCP Server On A Cisco Router
DHCP (Dynamic Host Configuration Protocol) is the protocol used by network devices (such as PCs, network printers, etc) to automatically obtain correct ne…















