MS Server Articles:
Windows Servers
Windows 2003 DHCP Server Advanced Configuration -…
Part 1 of our Windows 2003 DHCP Server Advanced Configuration article explained the creation and configuration of DHCP Scope options and how to confi…
Windows Servers
How to Recover & Create "Show Desktop" Icon Funct…
The Show Desktop feature, included with almost all versions of Windows up to Windows 7, allows a user to minimize or restore all open programs and e…
Windows Servers
Creating Windows Users and Groups with Windows 20…
In a Windows server environment, it is very important that only authenticated users are allowed to log in for security reasons. To fulfill this requi…
Windows Servers
Free Webinar: Scripting & Automation in Hyper-V w…
System Center Virtual Machine Manager (SCVMM) provides some great automation benefits for those organizations that can afford the hefty price tag. Ho…
Featured Subcategories:
Virtualization & VM Backup Articles:
Differences Between VMware vSphere, vCenter, ESXi…
In this article we will cover the differences between VMware ESXi, vSphere and vCenter while also explain the features supported by each vSphere edit…
The Backup Bible. A Free Complete Guide to Disast…
The Free Backup Bible Complete Edition written by backup expert and Microsoft MVP Eric Siron, is comprised of 200+ pages of actionable content divide…
Understanding Deduplication. Complete Guide to De…
When considering your VM backup solution, key features such as deduplication are incredibly important. This is not simply from a cost perspective but…
FREE Webinar - Fast Track your IT Career with VMw…
Everyone who attends the webinar has a chance of winning a VMware VCP course (VMware Install, Config, Manage) worth $4,500!
Climbing the career ladd…
Your IP address:
18.218.54.80
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Linux - Unix
Finding More Information On The Linux Operating System
Since this document merely scratches the surface when it comes to Linux, you will probably find you have lots of questions and possibly problems. Whether…
Linux - Unix
How To Secure Your Linux Server or Workstation - Linux…
Below are some of the most common recommendations and method to effectively secure a Linux Server or Workstation.
Boot Disk
One of the foremost requisit…
Linux - Unix
Installation and Configuration of Linux DHCP Server
For a cable modem or a DSL connection, the service provider dynamically assigns the IP address to your PC. When you install a DSL or a home cable router b…
Linux - Unix
Understanding The Linux Init Process & Different RunLe…
Different Linux systems can be used in many ways. This is the main idea behind operating different services at different operating levels. For example, th…
Popular Topics
OpManager - Network Monitoring & Management
Free Webinar: Clients' network configuration and compl…
Defending your client's network from faulty configuration changes, poor compliance, and bringing the network back quickly from downtime can be challenging…
Windows Workstations (XP, 7, 8, 10, 11)
How To Change & Configure An IP Address or Set to DHCP…
Not many users are aware that Windows 7 provides more than one way to configure a workstation’s network adaptor IP address or force it to obtain an IP add…
Network Protocol Analyzers
How to Detect SYN Flood Attacks with Capsa Network Pro…
This article explains how to detect a SYN Flood Attack using an advanced protocol analyser like Colasoft Capsa. We’ll show you how to identify and inspect…
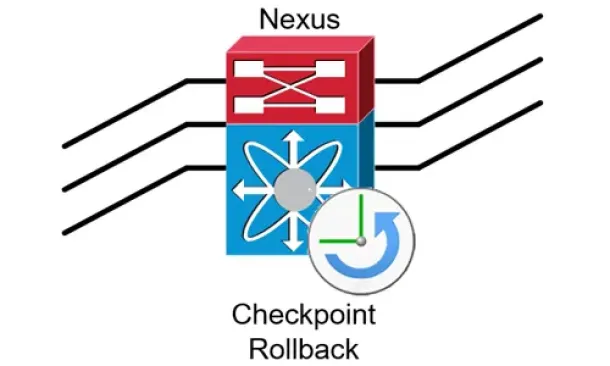
Cisco Data Center (Nexus/UCS)
Complete Guide to Nexus Checkpoint & Rollback Feature…
The Cisco NX-OS checkpoint feature provides the capability to capture at any time a snapshot (backup) of the Cisco Nexus configuration befo…

















