Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
|
Articles:
The OSI Model: Layer 5 - Session Layer
| Read |
|
Articles:
The OSI Model: Layer 4 - Transport Layer
| Read |
|
Articles:
The OSI Model: Layer 3 - Network Layer
| Read |
|
Articles:
The OSI Model: Layer 2 - Datalink Layer
| Read |
|
Articles:
The OSI Model: Layer 1 - Physical Layer
| Read |
Suggested Articles:
The OSI Model
The OSI Model: Layer 4 - Transport Layer
The Transport layer is responsible for providing mechanisms for multiplexing upper-layer application, session establishment, data transfer and tear d…
TCP - UDP Protocol Analysis
Transmission Control Protocol - Part 1: Introduct…
Understanding how each protocol fits into the OSI Model is essential for any network engineer. This page analyses how TCP is classified as a 'transpo…
Ethernet Protocol, CSMA/CD, Collisions
802.3 Fast Ethernet (100 Mbit/Sec) Model
Here we see a logical drawing of the Fast Ethernet Data Link Layer sublayers. Data is passed down from the upper layers (such as TCP/IP or Novell Net…
Ethernet Protocol, CSMA/CD, Collisions
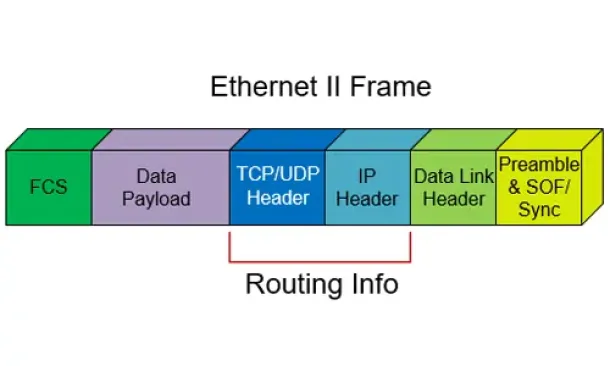
The Ethernet II Frame Format
The following is a description of the frame format described by the original Ethernet Version II specification as released by DEC, Intel, and Xerox…
Featured Subcategories:
Netflow Articles:

NetFlow Analyzer: Free Download, Step-by-Step Ins…
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows w…

Netflow: Monitor Bandwidth & Network Utilization…
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, applic…

Netflow vs SNMP. Two Different Approaches to Netw…
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ne…

Complete Guide to Netflow: How Netflow & its Comp…
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive int…
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
VLAN Networks
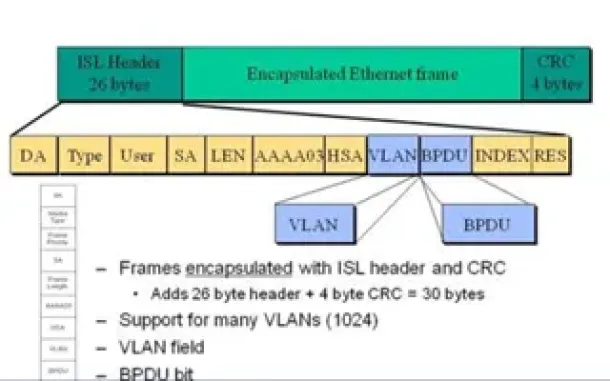
VLAN InterSwitch Link (ISL) Protocol Analysis
Deciding whether to use ISL or IEEE 802.1q to power your trunk links can be quite confusing if you cannot identify the advantages and disadvantages of eac…

VLAN Networks
Comparing Traditional Flat & VLAN Networks
Designing and building a network is not a simple job. VLANs are no exception to this rule, in fact they require a more sophisticated approach because of t…

VLAN Networks
InterVLAN Routing - Routing between VLAN Networks
This article deals with the popular topic of InterVLAN routing, which is used to allow routing & communication between VLAN networks. Our article anal…
VLAN Networks
VTP Protocol - In-Depth Analysis
The previous article introduced the VTP protocol, we examined how it can be used within a network, to help manage VLANs and ease the administrative overhe…
Routing
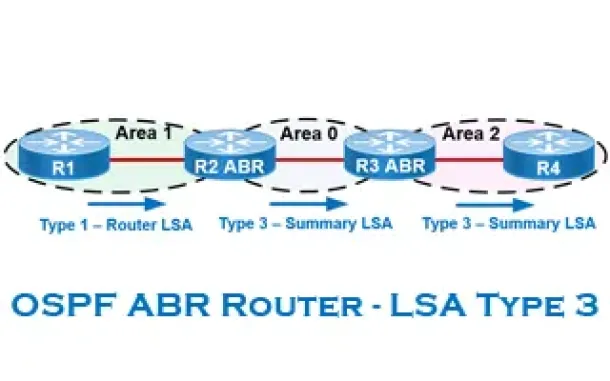
OSPF - Part 6: OSPF LSA Types - Purpose and Function o…
Our previous article explained the purpose of Link State Update (LSU) packets and examined the Link State Advertisement (LSA) information contained within…
Routing
Routed Protocols
We all understand that TCP/IP, IPX-SPX are protocols which are used in a Local Area Network (LAN) so computers can communicate between with each other and…
Routing
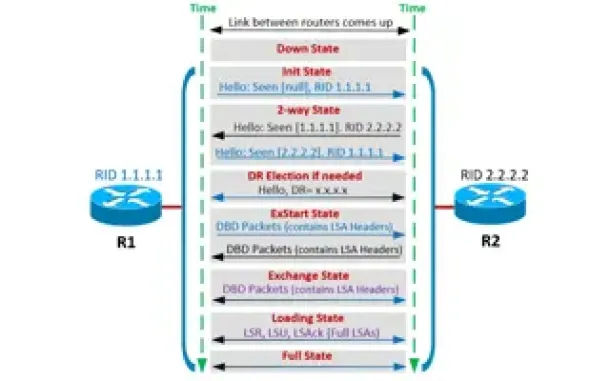
OSPF - Part 4: OSPF Neighbor States – OSPF Neighbor Fo…
This is the third article of our OSPF series which analyzes the different OSPF States routers go through during the OSPF discovery and neighbor forming pr…
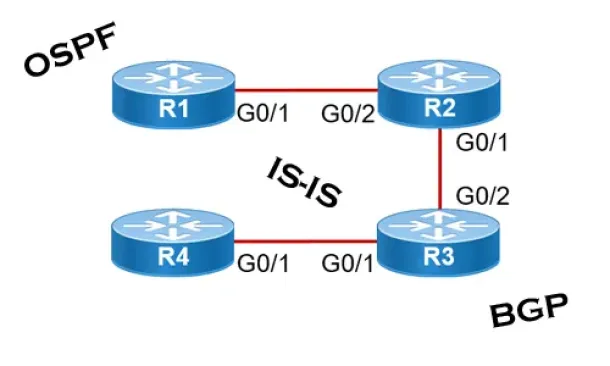
Routing
Link State Routing Protocols
Link State routing protocols do not view networks in terms of adjacent routers and hop counts, but they build a comprehensive view of the overall network…
Cisco Switches
VLAN Security Tips - Best Practices
This article focuses on VLAN Security and its implementation within the business network environment. We provide tips and Cisco CLI commands that will hel…
Cisco Switches
Discover Features & Capabilities - Cisco Catalyst 3850…
There’s a new switch around the block and its name is Catalyst 3850 – Cisco’s latest addition to its successful Catalyst series switches. The Cisco Cataly…
Windows Servers
How to Install Windows 2012 Hyper-V via Server Manager…
Our previous article covered the basic concepts of Virtualization and Windows Server 2012 Hyper-V. This article takes a closer look at Microsoft’s H…
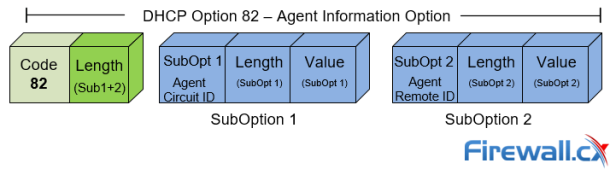
Cisco Switches
DHCP Option 82 Message Format, Analysis. DHCP Snooping…
This article provides in-depth analysis of DHCP Option 82 (DHCP Relay Agent) which is one of the +180 DHCP Options available to the DHCP protocol and used…



















