How to Scan Your Network and Discover Unpatched, Vulnerable, High-Risk Servers or Workstations using GFI LanGuard 2015
 This article shows how any IT Administrator, network engineer or security auditor can quickly scan a network using GFI’s LanGuard and identify the different systems such as Windows, Linux, Android etc. More importantly, we’ll show how to uncover vulnerable, unpatched or high-risk Windows systems including Windows Server 2003, Windows Server 2008, Windows Server 2012 R2, Domain Controllers, Linux Servers such as RedHat Enterprise, CentOS, Ubuntu, Debian, openSuse, Fedora, any type of Windows workstation (XP, Vista, 7, 8, 8.1,10) and Apple OS X.
This article shows how any IT Administrator, network engineer or security auditor can quickly scan a network using GFI’s LanGuard and identify the different systems such as Windows, Linux, Android etc. More importantly, we’ll show how to uncover vulnerable, unpatched or high-risk Windows systems including Windows Server 2003, Windows Server 2008, Windows Server 2012 R2, Domain Controllers, Linux Servers such as RedHat Enterprise, CentOS, Ubuntu, Debian, openSuse, Fedora, any type of Windows workstation (XP, Vista, 7, 8, 8.1,10) and Apple OS X.
GFI’s LanGuard is a swiss-army knife that combines a network security tool, vulnerability scanner and patching management system all in one package. Using the network scanning functionality, LanGuard will automatically scan the whole network and use the provided credentials to log into every located host and discover additional vulnerabilities.
To begin, we launch GFI LanGuard and at the startup screen, select the Scan Tab as shown below:
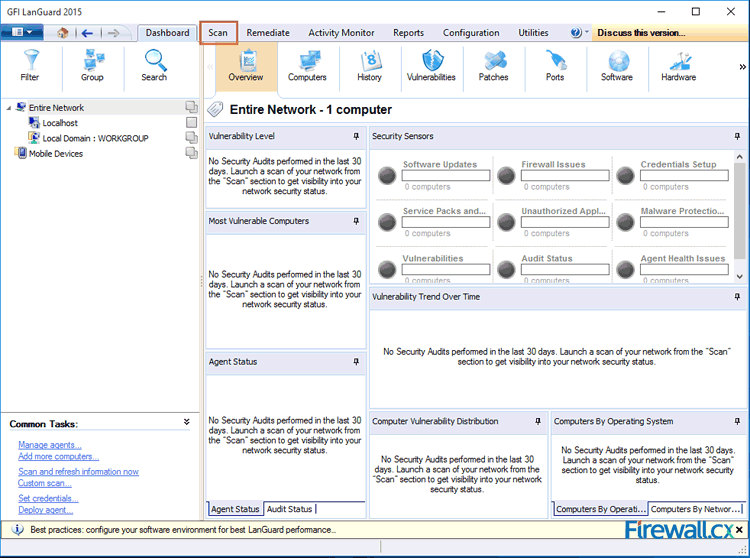
Figure 1. Launching GFI LanGuard 2015
Next, in the Scan Target section, select Custom target properties (box with dots) and click on Add new rule. This will bring us to the final window where we can add any IP address range or CIDR subnet:
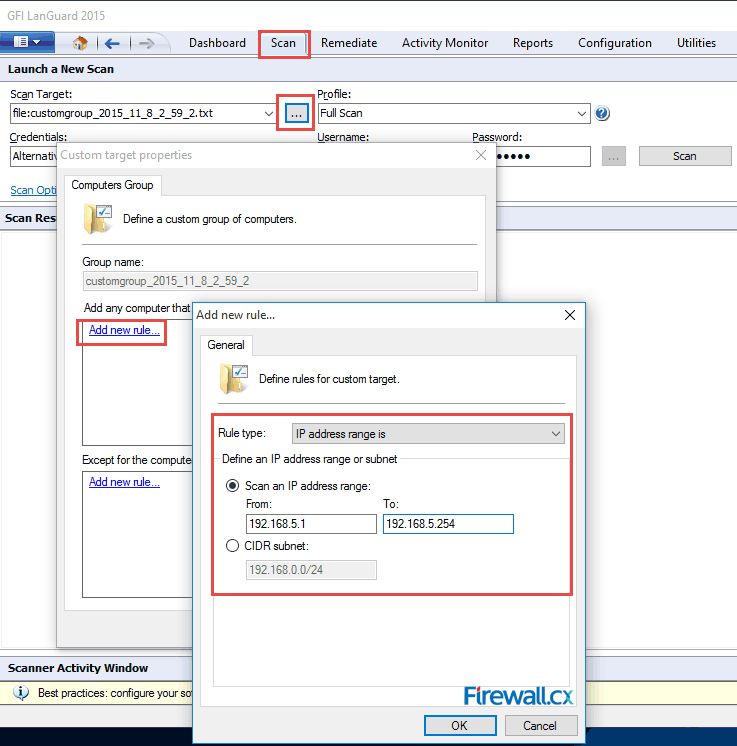
Figure 2. Adding your IP Network – Subnet to LanGuard for scanning
Now enter the IP address range you would like LanGuard to scan, e.g 192.168.5.1 to 192.168.5.254 and click OK.
The new IP address range should now appear in the Custom target properties window:
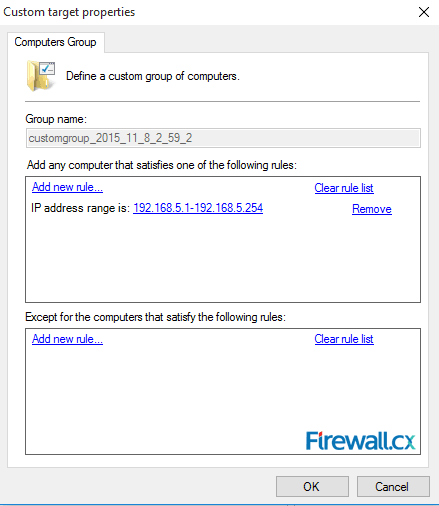
Figure 3. Custom target properties displays selected IP address range
Now click on OK to close the Custom target properties window and return back to the Scan area:
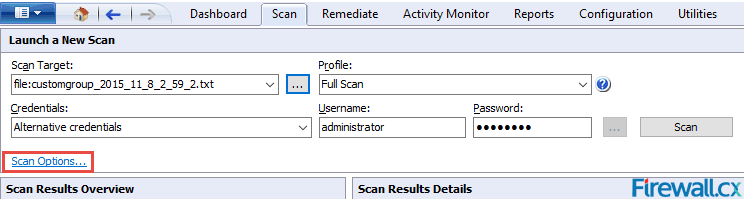
Figure 4. Returning back to LanGuard’s Scan area
At this point, we can enter the credentials (Username/Password) to be used for remotely accessing hosts discovered (e.g domain administrator credentials is a great idea) and selectively click on Scan Options to reveal additional useful options to be used during our scan, such as Credential Settings and Power saving options. Click on OK when done:
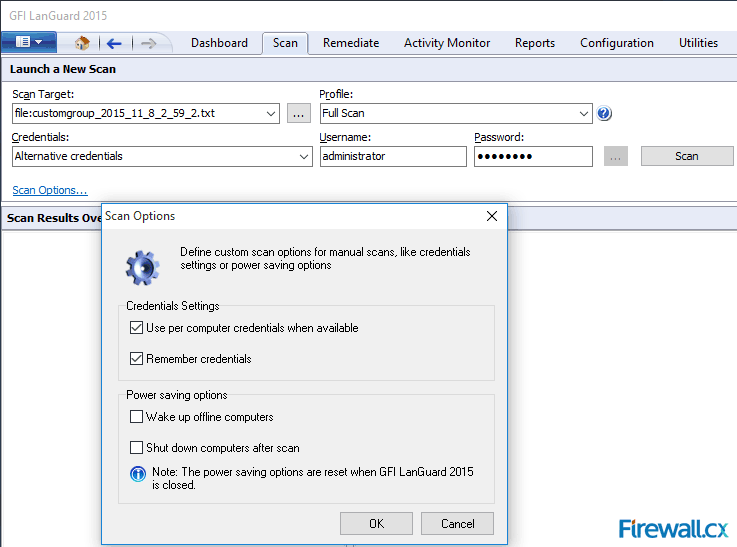
Figure 5. Additional Scan Options in GFI’s LanGuard 2015
We can now hit Scan to begin the host discovery and scan process:
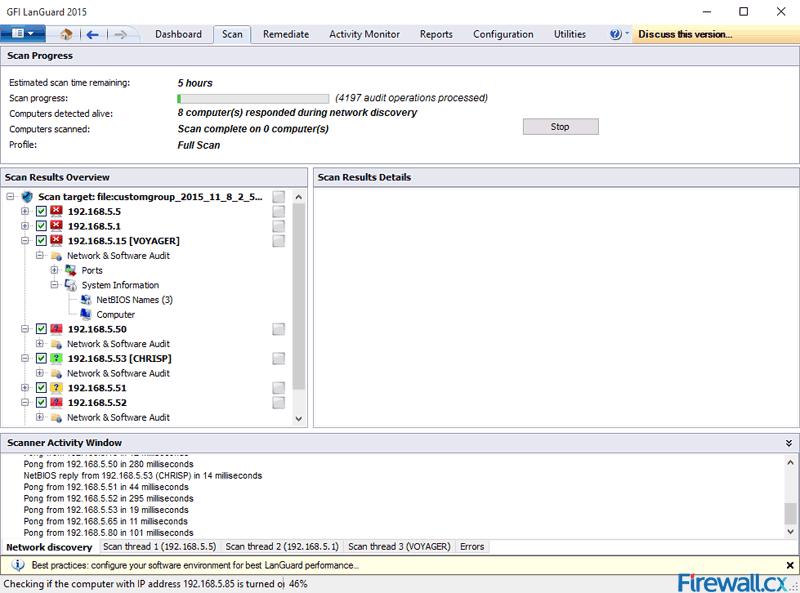
Figure 6. Initiating the discovery process in GFI LanGuard 2015
GFI LanGuard will being scanning the selected IP subnet and list all hosts found in the Scan Results Overview window area. As shown in the above screenshot, each host will be identified according to its operating system and will be accessed for open ports, vulnerabilities and missing operating system & application patches.
The full scan profile selected will force GFI LanGuard to run a complete detailed scan of every host.
Once complete, GFI LanGuard 2015 displays a full report summary for every host and an overal summary for the network:
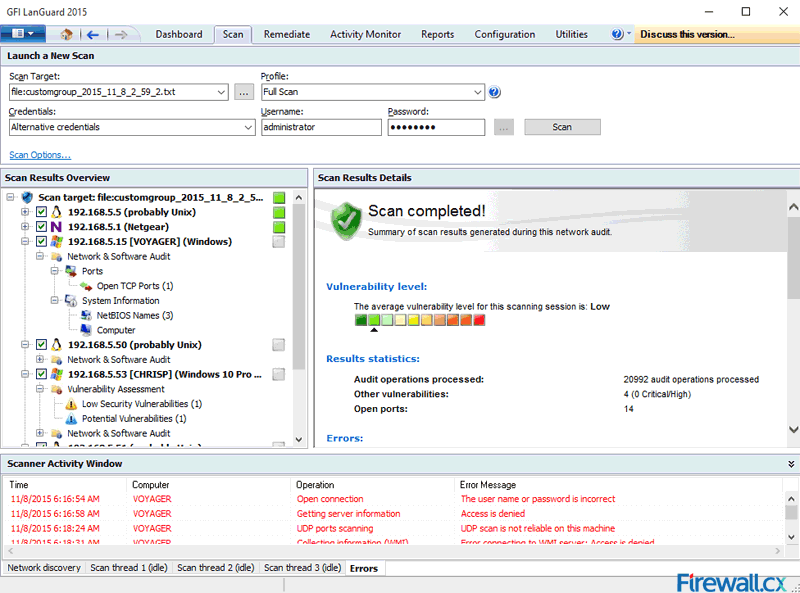
Figure 7. GFI LanGuard 2015 overall scan summary and results
Users can select each host individually from the left window and their Scan Results will be diplayed on the right window area (Scan Results Details). This method allows quick navigation through each host, but also allows the administrator or network security auditor to quickly locate specific scan results they are after.
This article explained how to configure GFI LanGuard 2015 to scan an IP subnet network, identify host operating systems, log into remote systems, scan for vulnerabilities, missing operating system and application patches, open ports and other critical security issues. IT Managers, network engineers and security auditors should defiantely try GFI LanGuard and see how easy & automated their job can become with such a powerfull network security tool in their hands.
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!











