Increase your Enterprise or SMB Organization Security via Internet Application & User Control. Limit Threats and Internet Abuse at the Workplace
 In this era of constantly pushing for more productivity and greater efficiency, it is essential that every resource devoted to web access within a business is utilised for business benefit. Unless the company concerned is in the business of gaming or social media, etc. it is unwise to use resources like internet/web access, and the infrastructure supporting it, for a purpose other than business. Like they say, “Nothing personal, just business”
In this era of constantly pushing for more productivity and greater efficiency, it is essential that every resource devoted to web access within a business is utilised for business benefit. Unless the company concerned is in the business of gaming or social media, etc. it is unwise to use resources like internet/web access, and the infrastructure supporting it, for a purpose other than business. Like they say, “Nothing personal, just business”
With this in mind, IT administrators have their hands full ensuring management of web applications and their communication with the Internet. The cost of not ensuring this is loss of productivity, misuse of bandwidth and potential security breaches. As a business it is prudent to block any unproductive web application e.g. gaming, social media etc. and restrict or strictly monitor file sharing to mitigate information leakages.
It is widely accepted that in this area firewalls are of little use. Port blocking is not the preferred solution as it has a similar effect to a sledge hammer. What is required is the fineness of a scalpel to parse out the business usage from the personal and manage those business requirements accordingly. To be able to manage web application at such a level, it is essential to be able to identify and associate the request with its respective web application. Anything in line with business applications goes through, the rest are blocked.
This is where WebMonitor excels in terms of delivering this level of precision and efficiency. It identifies access requests from supported applications using inspection technology and helps IT administrators to allow or block them. Hence, the administrators can allow certain applications for certain departments while blocking certain other applications as part of a blanket ban, thus enhancing the browsing experience of all users.
So, to achieve this, the process is to use the unified policy system of WebMonitor. The policies can be configured specifically for application control or, within the same policy, several application controls can be combined using other filtering technologies.
Let’s take a look at the policy panel of WebMonitor:
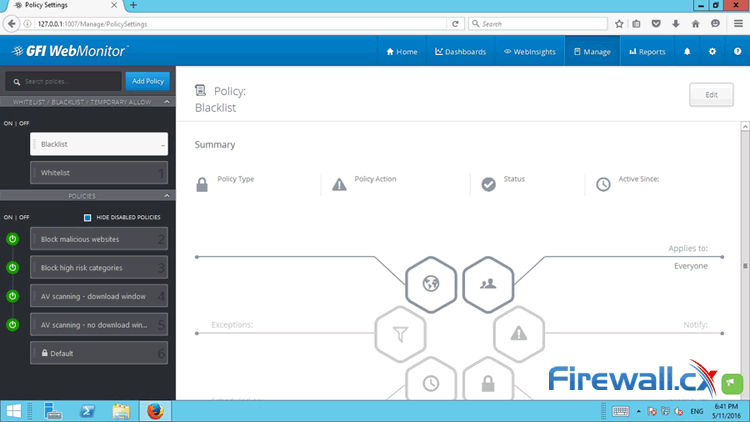 Figure 1. WebMonitor Policy Panel interface. Add, delete, create internet access policies with ease (click to enlarge)
Figure 1. WebMonitor Policy Panel interface. Add, delete, create internet access policies with ease (click to enlarge)
In order to discover the controls that are available against a certain application, the application needs to be dragged into the panel. For example, if we were to create a policy to block Google Drive we would be dragging that into the panel itself.
Once the related controls show up, we can select an application or application category the policy will apply to.
The rest of the configuration from this point will allow creating definitions for the following:
- Filter options
- Scope of the policy
- Actions to be taken
- Handling of exceptions
- Managing notifications
All of the above are ready to be implemented in a ‘drag – and – drop’ method. GFI WebMonitor will commence controlling access of the configured application to the Internet the moment the policy is saved.
So, going back to the example of creating the ‘block Google Drive’ policy, the steps are quite simple:
1. Click on ‘Add Policy’ as show in the following image:
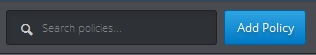
Figure 2. Click on the “Add Policy” button to being creating a policy to block internet access
Enter a Name and description in the relevant fields:
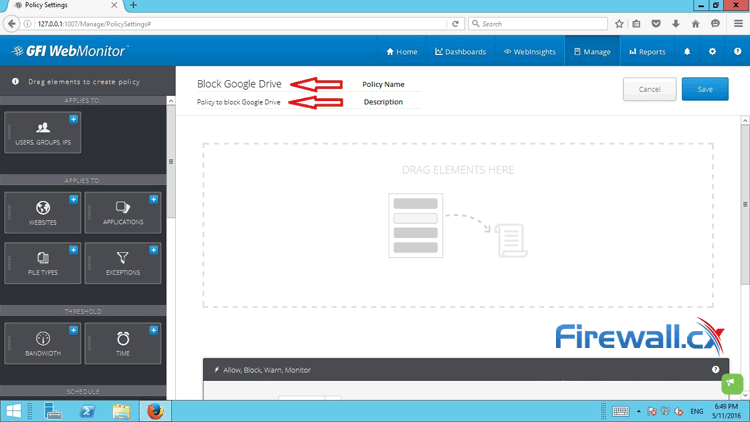 Figure 3. Adding policy name and description in WebMonitor to block an application network-wide (click to enlarge)
Figure 3. Adding policy name and description in WebMonitor to block an application network-wide (click to enlarge)
3. As this policy applies to ‘all’, at this moment there is no need to configure the scope. This can be done on a per user, group or IP address only basis.
4. Drag in the Application Block from the left panel (as shown in the following image), Select ‘Block’ in the ‘Allow, Block, Warn, Monitor’ section.
5. In the Application Category section, select ‘File Transfer’ as shown in the image below:
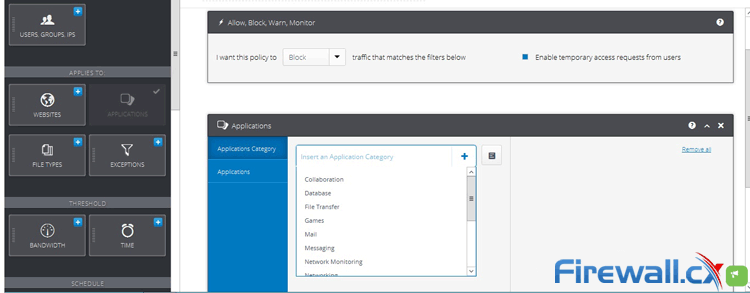 Figure 4. WebMonitor: Blocking the File Transfer application category from the internet (click to enlarge)
Figure 4. WebMonitor: Blocking the File Transfer application category from the internet (click to enlarge)
6. Click on the ‘Applications’ Tab and start typing ‘Google Drive’ in the field. The drop down list will include Google Drive. Select it and then press enter. The application will be added. Now Click on Save.
We need to keep in mind that the policy is operational the moment the Save button, located at the top right corner, is clicked.
Now if any user tries to access the web application Google Drive, he/she will be presented with the ‘Block Page’ rendered by GFI WebMonitor. At the same time, any Google Drive thick client installed on the user’s machine will not be able to connect to the Internet
As mentioned earlier, and reiterated through the above steps, the process of creating and implementing a web access management policy in WebMonitor is quite simple. Given the length and breadth of configuration options within the applications and the scope, this proves to be a very powerful tool that will make the task of managing and ensuring proper usage of web access, simple and effective for IT Administrators in small and large enterprise networks.
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!











