Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
Cisco Router Password Recovery
| Read |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
Cisco Router Basic ISDN Configuration
| Read |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
Cisco Router 'Privileged' Mode
| Read |
|
Articles:
Cisco Router 'User Exec' Mode
| Read |
|
Articles:
Cisco Router Modes
| Read |
|
Articles:
Cisco Router Basics
| Read |
|
Articles:
Introduction To Routers
| Read |
Suggested Articles:
Cisco Firewalls
Cisco ASA Firepower Threat Defense (FTD): Downloa…
One Appliance – One Image is what Cisco is targeting for its Next Generation Firewalls. With this vision, Cisco has created a unified software image…
Cisco CallManager-CCME
How To Upgrade Cisco - Linksys SPA8000 Firmware
The Cisco - Linksys SPA8000 is an 8-port IP Telephony Gateway that allows connections for up to eight analog telephones (provides 8 FXS ports) to a V…
Cisco Wireless
Easily Convert Cisco Autonomous - Standalone AP t…
This article explains how to convert a local or remote Autonomous / Standalone Cisco Aironet Access Point to Lightweight and register it to a Cisco W…
Cisco Data Center (Nexus/UCS)
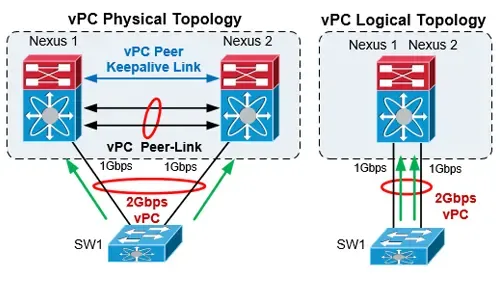
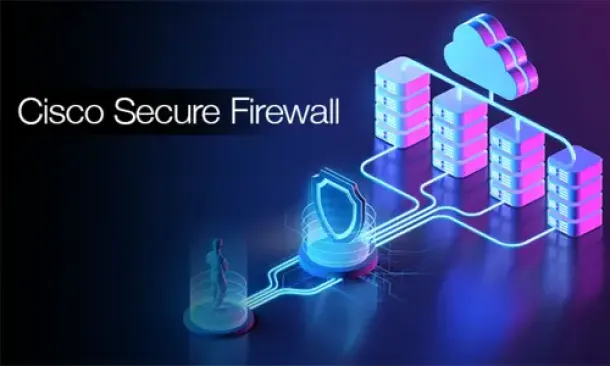
The Complete Cisco Nexus vPC Guide. Features & Ad…
Cisco virtual Port Channel (vPC) is a virtualization technology, launched in 2009, which allows links that are physically connected to two different…
Featured Subcategories:
Data Center Articles:
The Complete Cisco Nexus vPC Guide. Features & Ad…
Cisco virtual Port Channel (vPC) is a virtualization technology, launched in 2009, which allows links that are physically connected to two different…

Introduction to Cisco Nexus Switches – Nexus Prod…
This article introduces the Cisco Nexus product family (Nexus 9000, Nexus 7000, Nexus 5000, Nexus 3000, Nexus 2000, Nexus 1000V and MDS 9000). We exp…

Join Australia’s First Official Cisco Data Center…
It’s a reality – Australia now has its own Official Cisco Data Center User Group (DCUG) and it’s growing fast! Originally inspired by Cisco Champions…

NEXUS NX-OS: Useful Commands, CLI Scripting, Hint…
Whether you’re new to Cisco Nexus switches or have been working with them for years this article will show how to get around the Nexus NX-OS usi…
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Cisco Switches
Basic & Advanced Catalyst Layer 3 Switch Configuration…
This article covers basic and advanced configuration of Cisco Catalyst Layer-3 switches such as the Cisco Catalyst 3560G, 3560E, 3560-X, 3750, 3750E, 3750…
Cisco Switches
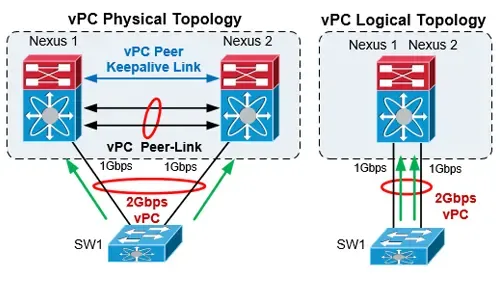
DHCP Option 82 Message Format, Analysis. DHCP Snooping…
This article provides in-depth analysis of DHCP Option 82 (DHCP Relay Agent) which is one of the +180 DHCP Options available to the DHCP protocol and used…
Cisco Switches
Password Recovery / Password Reset Procedure for Catal…
This article shows how to reset a password on a Cisco Catalyst 3750-X (stacked or single unit) and Cisco Catalyst 3560-x switch without losing its startup…
Cisco Switches
Forcing A Cisco Catalyst Switch To Use 3rd Party SFP M…
Many companies are seeking for Cisco SFP alternatives to help cut down the costs on these expensive modules.
A frequent customer problem with Cisco's new…
Cisco Firewalls
Cisco ASA 5500 Series Firewall Modules & Cards – Conte…
Cisco’s Adaptive Security Appliance (ASA) Firewalls are one of the most popular and proven security solutions in the industry. Since the introduction of t…
Cisco Firewalls
Cisco ASA 5500-X Series Firewall with IPS, ASA CX & Fi…
The Cisco ASA Firewall 5500-X series has evolved from the previous ASA 5500 Firewall series, designed to protect mission critical corporate networks and d…
Cisco Firewalls
Cisco ASA5500 (5505, 5510, 5520, etc) Series Firewall…
The Cisco ASA 5500 series security appliances have been around for quite some time and are amongst the most popular hardware firewalls available in the ma…
Cisco Firewalls
Converting Cisco Firepower from Platform mode to Appli…
This article explains how to configure a Cisco Firepower 2100 series device to operate in Appliance mode. We’ll show you how to switch from Platform mode…
Popular Topics
Virtualization & VM Backup
How to Enable or Disable SSH on VMware ESXi via Web GU…
SSH access to VMware’s ESXi server is by disabled by default however there are many reasons where SSH might be required. VMware and System administrators…
Palo Alto Networks
How to Register a Palo Alto Firewall and Activate Supp…
This article explains how to register and activate your Palo Alto Firewall Appliance to obtain technical support, RMA hardware replacement, product update…
Palo Alto Networks
Complete Guide to Upgrading Palo Alto Firewall PAN-OS…
Upgrading your Palo Alto Firewall or Panorama Management System to the preferred PAN-OS release is always recommended as it ensures it remains stable, saf…
SASE & SD-WAN Networks
MPLS vs. SD-WAN vs. Internet vs. Cloud Network. Connec…
The Wide Area Network (WAN) is the backbone of the business. It ties together the remote locations, headquarters and data centers into an integrated netwo…

















