The New GFI EventsManager 2013 - Active Network and Server Monitoring
On the 21st of January 2013, GFI announced its new version of its popular GFI EventsManager, now named, GFI EventsManager 2013.
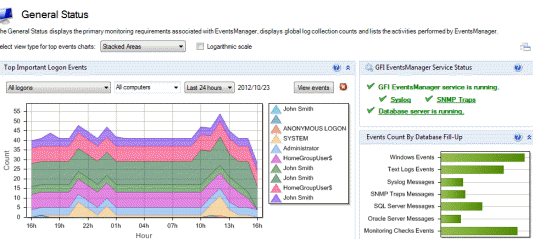
For those who are unaware of the product, GFI EventsManager is one of the most popular software solutions that allows a network administrator, engineer or IT manager to actively monitor a whole IT infrastructure from a single intuitive interface.
Even though GFI EventsManager has been in continuous development, this time GFI has surprised us once again by introducing highly anticipated features that make this product a one-of-a-kind winner.
Below is a list of some of the new features included in GFI EventsManager 2013 that make this product a must for any company:
- Active network and server monitoring based on monitoring checks is now available and can function in conjunction with the log based monitoring system in order to provide a complete and thorough view of the status of your environment.
- The unique combination of active network and server monitoring through log-based network and server monitoring provides you not only with incident identification but also with a complete set of logs from the assets that failed, making problem investigation and solving much easier.
- Enhanced console security system helps complying with 'best practices' recommendations that imply access to data on a “need-to-know” basis. Starting with this version, each GFI EventsManager user can be assigned a subset of computers that he/she manages and the console will only allow usage of the data coming from those configured computers while the user is logged in.
- New schema for parsing XML files, available by default, that enables monitoring of XML–based logs and configuration files.
- New schema for parsing DHCP text logs that enables monitoring of DHCP IP assignment.
- More flexibility for storing events: the new database system has been updated to include physical deletion of events for easier maintenance and collection to remote databases.
- Hashing of log data for protection against attempts at tampering with the logs coming from outside the product, enables enhanced log consolidation and security.
- New reports for J Sox and NERC CIP compliance.
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!











