Scan and Generate Firewall Rules to Secure your Website and WebServer with ModSecurity. Block Exploits & Vulnerability Attacks
ModSecurity is a very popular open-source web application Firewall used to protect webservers and websites from vulnerability attacks, exploits, unauthorized access and much more. In this article, we’ll show you how web vulnerability scanners, can be used to automatically generate the necessary rules that block all vulnerabilities identified during the scan.
This great feature of automatically generating ModSecurity rules for identified vulnerabilities through a web vulerability scanner, giving all users the ability to now create and deploy ModSecurity rules immediately – saving valuable time and accelerating the whole scan-&-patching process considerably. 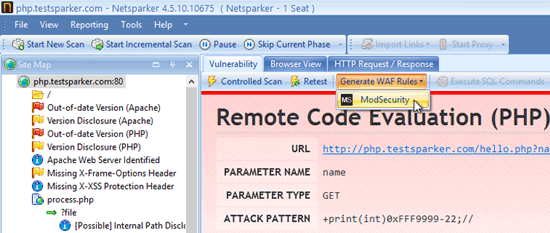 Figure 1. Generating ModSecurity Rules from a Web Application Vulnerability Scanner
Figure 1. Generating ModSecurity Rules from a Web Application Vulnerability Scanner
ModSecurity is used by many vendors and webservice providers as it is capable of delivering a number of security services including:
- Full HTTP traffic logging. ModSecurity gives you the ability to log anything you need, including raw transaction data, which is essential for forensics analysis and in-depth tracing.
- Web Application Hardening. Helps fix cross-site request forgery vulnerabilities and enforce security policies with other Apache modules.
- Real-time application security monitoring. ModSecurity provides full access to the HTTP traffic stream along with the ability to inspect and action against attacks.
- Becomes a powerful exploit prevention tool when paired with web server and web application vulnerability scanners such as Netsparker.
Most Web Application Vulnerability Scanner vendors provide full details on how to use their web application scanner to successfully generate ModSecurity rules that will help identify and block existing vulnerabilities in web applications and web servers.
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!











