Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
Suggested Articles:
SASE & SD-WAN Networks
WAN Optimization vs SD WAN Networks. Today’s Ch...
Enterprises have been successfully running WAN optimization appliances at their many distributed sites for years. The devices have done a good job ...
SASE & SD-WAN Networks
SASE and VPNs: Reconsidering your Mobile Remote...
The Virtual Private Network (VPN) has become the go to security solution for keeping communications between networks and endpoints secure. After al...
Palo Alto Networks
Introduction to Palo Alto Next-Generation Netwo...
During the past decade, we’ve seen the global IT security market flooded with new network security and firewall security appliances. New vendors em...
Palo Alto Networks
How to Register a Palo Alto Firewall and Activa...
This article explains how to register and activate your Palo Alto Firewall Appliance to obtain technical support, RMA hardware replacement, product...
Featured Subcategories:
SASE & SD-WAN Articles:
The Most Common Worst Networking Practices and ...
In the rush to keep pace with the many challenges facing today’s organizations, all too often networking teams end up adopting practices and proces...
MPLS vs. SD-WAN vs. Internet vs. Cloud Network....
The Wide Area Network (WAN) is the backbone of the business. It ties together the remote locations, headquarters and data centers into an integrate...
How To Secure Your SD-WAN. Comparing DIY, Manag...
With so much enterprise network traffic now destined for the cloud, backhauling traffic across an expensive MPLS connection to a data center to app...
Configuring A SASE Unified Network: Data center...
This article explores the need for Secure Access Service Edge (SASE) in today’s organizations. We show how one of the most advanced SASE platforms ...
Your IP address:
3.17.154.171
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Palo Alto Networks
Palo Alto Networks Firewall - Web & CLI Initial Conf...
This article is the second-part of our Palo Alto Networks Firewall technical articles. Our previous article was introduction to Palo Alto Networks Firew...

Palo Alto Networks
How to Manually Download, Import & Install PAN-OS on...
This article provides comprehensive guidance on the manual processes involved in downloading, uploading, and installing (import) any PAN-OS version on a...
Palo Alto Networks
How to Register a Palo Alto Firewall and Activate Su...
This article explains how to register and activate your Palo Alto Firewall Appliance to obtain technical support, RMA hardware replacement, product upda...

Palo Alto Networks
Configuring QoS on Palo Alto Firewalls: Class-based ...
This article’s purpose is to help you quickly master Palo Alto QoS concepts and learn to configure QoS on Palo Alto Firewalls in a simple and efficient ...
Popular Topics
Cisco Wireless
Cisco WLC Interfaces, Ports & Their Functionality. U...
Our previous article introduced Cisco’s popular Wireless ControllerCisco’s popular Wireless Controller (WLC) devices and examined their benefits to ente...

Network Fundamentals
Introduction To Networking
A network is simply a group of two or more Personal Computers linked together. Many types of networks exist, but the most common types of networks are L...
Cisco Routers
How To Fix Cisco Configuration Professional (CCP) 'J...
Our previous article covered how to fix the Cisco Configuration Professional display/window problem where the CCP application is displayed in about one ...
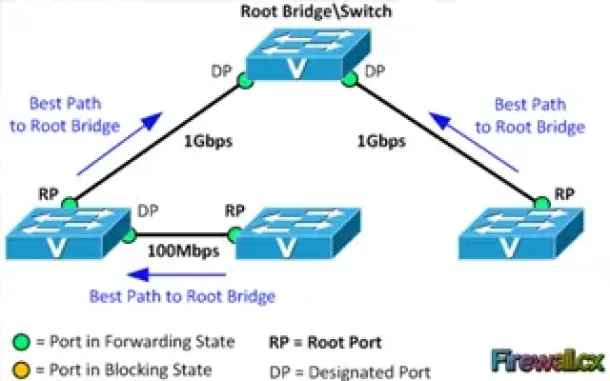
Spanning Tree Protocol (STP)
Spanning Tree Protocol – Part 2: Rapid STP Port Cost...
Spanning Tree Protocol, Rapid STP port costs and port states are an essential part of the STP algorithm that affect how STP decides to forward or block ...



















