Suggested Articles:
Network Protocol Analyzers
How to Perform TCP SYN Flood DoS Attack & Detec...
This article will help you understand TCP SYN Flood Attacks, show how to perform a SYN Flood Attack (DoS attack) using Kali Linux & hping3 and ...

ManageEngine Firewall Analyzer
Ensuring Compliance and Business Continuity in ...
In the wake of digital transformation, the work landscape as we know it has undergone a dynamic shift. People can now work from home, from the offi...

EventLog Analyzer
Event Log Monitoring System: Implementation, Ch...
An event log monitoring system, often referred to as an event log management, is a critical component to IT security & Management, that helps o...

ManageEngine Firewall Analyzer
Discover the Ultimate Firewall Management Tool:...
Firewall security management is a combination of monitoring, configuring, and managing your firewall to make sure it runs at its best to effectivel...
Featured Subcategories:
WireShark Articles:
How to Perform TCP SYN Flood DoS Attack & Detec...
This article will help you understand TCP SYN Flood Attacks, show how to perform a SYN Flood Attack (DoS attack) using Kali Linux & hping3 and ...
Detect Brute-Force Attacks with nChronos Networ...
Brute-force attacks are commonly known attack methods by which hackers try to get access to restricted accounts and data using an exhaustive list/d...
How to Detect SYN Flood Attacks with Capsa Netw...
This article explains how to detect a SYN Flood Attack using an advanced protocol analyser like Colasoft Capsa. We’ll show you how to identify and ...
How to Detect Routing Loops and Physical Loops ...
When working with medium to large scale networks, IT departments are often faced dealing with network loops and broadcast storms that are caused by...
Your IP address:
3.16.147.124
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Palo Alto Networks
The Benefits of Palo Alto Networks Firewall Single P...
What makes Palo Alto Networks Next-Generation Firewall (NGFW) so different from its competitors is its Platform, Process and Architecture. Palo Alto Net...

Palo Alto Networks
Configuring QoS on Palo Alto Firewalls: Class-based ...
This article’s purpose is to help you quickly master Palo Alto QoS concepts and learn to configure QoS on Palo Alto Firewalls in a simple and efficient ...
Palo Alto Networks
Palo Alto Firewalls Security Zones – Tap Zone, Virtu...
Palo Alto Networks Next-Generation Firewalls rely on the concept of security zones in order to apply security policies. This means that access lists (fi...
Palo Alto Networks
Palo Alto Firewall Configuration Options. Tap Mode, ...
Our previous article explained how Palo Alto Firewalls make use of Security Zones to process and enforce security policies. This article will explain th...
Windows Servers
Windows Server 2016 – Hyper-V Virtualization Update
The new Hyper-V virtualization features offered by Windows Server 2016 are planning to make major changes in the virtualization market. From Nested Hype...
Windows Servers
Creating a Virtual Machine in Windows Hyper-V. Confi...
Our previous articles covered basic concepts of Virtualization along with the installation and monitoring of Windows 2012 Hyper-V. This article takes th...
Windows Servers
How to Recover & Create "Show Desktop" Icon Function...
The Show Desktop feature, included with almost all versions of Windows up to Windows 7, allows a user to minimize or restore all open programs and easil...
Windows Servers
Easy, Fast & Reliable Hyper-V & VMware Backup with A...
As more companies around the world adopt the virtualization technology to increase efficiency and productivity, Microsoft’s Hyper-V virtualization platf...
Popular Topics
SASE & SD-WAN Networks
Check Point Software and Cato Networks Co-Founder Sh...
By: Shlomo Kramer, Check Point Software & Cato Networks Co-Founder
As one of the founders of Check Point Software and more recently Cato Networks, ...
Routing
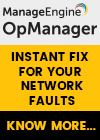
OSPF - Part 3: OSPF Adjacency & Neighbor Forming Pro...
This is the thrid article of our 6-part OSPF series (see below) that describes how OSPF routers perform neighbor relationship and adjacency. We’ll exami...
Network Protocol Analyzers
How To Detect ARP Attacks & ARP Flooding With Colaso...
ARP attacks and ARP flooding are common problems small and large networks are faced with. ARP attacks target specific hosts by using their MAC address a...
Routing
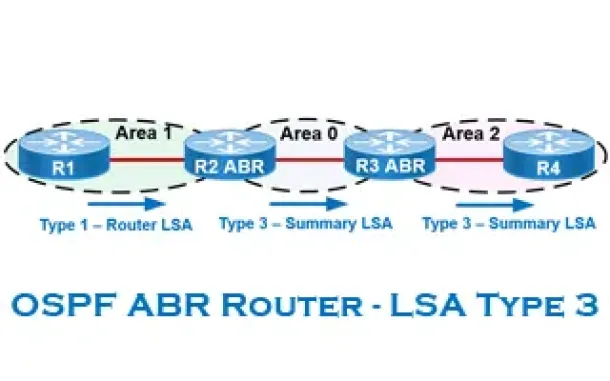
OSPF - Part 6: OSPF LSA Types - Purpose and Function...
Our previous article explained the purpose of Link State Update (LSU) packets and examined the Link State Advertisement (LSA) information contained with...
Cisco Routers
How To Configure DHCP Server On A Cisco Router
DHCP (Dynamic Host Configuration Protocol) is the protocol used by network devices (such as PCs, network printers, etc) to automatically obtain correct ...
Cisco Services & Technologies
Cisco VPN Client & Windows 8 (32bit & 64bit) - Reaso...
The Cisco VPN client is one of the most popular Cisco tools used by administrators, engineers and end-users to connect to their remote networks and acce...
Cisco Switches
Installation and Setup of Cisco SG500-52P - 500 Seri...
The SG500 series Cisco switches are the next step up from the already popular SG300 Layer-3 switches. Cisco introduced the SG Small Business series swit...
Cisco CallManager-CCME
How To Upgrade Cisco - Linksys SPA8000 Firmware
The Cisco - Linksys SPA8000 is an 8-port IP Telephony Gateway that allows connections for up to eight analog telephones (provides 8 FXS ports) to a VoIP...