Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
|
Articles:
Firewall.cx Free Cisco Lab: Our Partners
| Read |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
Suggested Articles:
Network Protocol Analyzers
Improve Network Analysis Efficiency with Colaso...
Troubleshooting network problems can be a very difficult and challenging task. While most IT engineers use a network analyzer to help solve network...
Network Protocol Analyzers
How to Use Multi-Segment Analysis to Troublesho...
Troubleshooting network problems can be a very intensive and challenging process. Intermittent network problems are even more difficult to troubles...
Network Protocol Analyzers
Advanced Network Protocol Analyzer Review: Cola...
Firewall.cx has covered Colasoft Capsa several times in the past, but its constant improvements make it well worth revisiting. Since the last revie...
Network Protocol Analyzers
How to Perform TCP SYN Flood DoS Attack & Detec...
This article will help you understand TCP SYN Flood Attacks, show how to perform a SYN Flood Attack (DoS attack) using Kali Linux & hping3 and ...
Featured Subcategories:
WireShark Articles:
How To Detect ARP Attacks & ARP Flooding With C...
ARP attacks and ARP flooding are common problems small and large networks are faced with. ARP attacks target specific hosts by using their MAC addr...
How to Reconstruct HTTP Packets/Data & Monitor ...
HTTP reconstruction is an advanced network security feature offered by nChronos version 4.3.0 and later. nChronos is a Network Forensic Analysis ap...
Introducing Colasoft Unified Performance Manage...
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, qua...
How to Detect P2P (peer-to-peer) File Sharing, ...
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing proce...
Your IP address:
3.140.188.16
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Palo Alto Networks
How to Register a Palo Alto Firewall and Activate Su...
This article explains how to register and activate your Palo Alto Firewall Appliance to obtain technical support, RMA hardware replacement, product upda...

Palo Alto Networks
How to Manually Download, Import & Install PAN-OS on...
This article provides comprehensive guidance on the manual processes involved in downloading, uploading, and installing (import) any PAN-OS version on a...
Palo Alto Networks
Palo Alto Firewalls Security Zones – Tap Zone, Virtu...
Palo Alto Networks Next-Generation Firewalls rely on the concept of security zones in order to apply security policies. This means that access lists (fi...
Palo Alto Networks
The Benefits of Palo Alto Networks Firewall Single P...
What makes Palo Alto Networks Next-Generation Firewall (NGFW) so different from its competitors is its Platform, Process and Architecture. Palo Alto Net...
Windows Servers
Windows 2012 Server Foundation, Essential, Standard ...
FREE Hyper-V & VMware Virtualization Backup: FREE for Firewall.cx readers for a Limited Time! Download Now!
Windows Server 2012 Edition...
Windows Servers
Installation and Configuration of Fine-Grained Passw...
Microsoft introduced Fine-Grained Password Policy for the first time in Windows Server 2008 and the policy has been part of every Windows Server since t...
Windows Servers
Free Webinar & eBook on Microsoft Licensing for Virt...
Microsoft Licensing for Virtual environments can become a very complicated topic, especially with all the misconceptions and false information out there...
Windows Servers
How to Install and Configure SNMP for Windows Server...
Simple Network Management Protocol (SNMP) is a UDP protocol that uses port 161 to monitor and collect detailed information on any network device support...
Popular Topics
Virtualization & VM Backup
Understanding Deduplication. Complete Guide to Dedup...
When considering your VM backup solution, key features such as deduplication are incredibly important. This is not simply from a cost perspective but al...
Network Protocol Analyzers
Improve Network Analysis Efficiency with Colasoft's ...
Troubleshooting network problems can be a very difficult and challenging task. While most IT engineers use a network analyzer to help solve network prob...
Routing
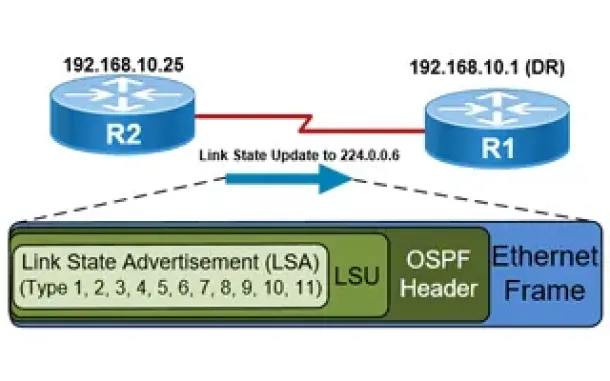
OSPF - Part 5: Analysis of OSPF Link State Update (L...
This article explains how OSPF uses Link State Advertisement (LSA) to exchange information about the network topology between routers. When a router rec...
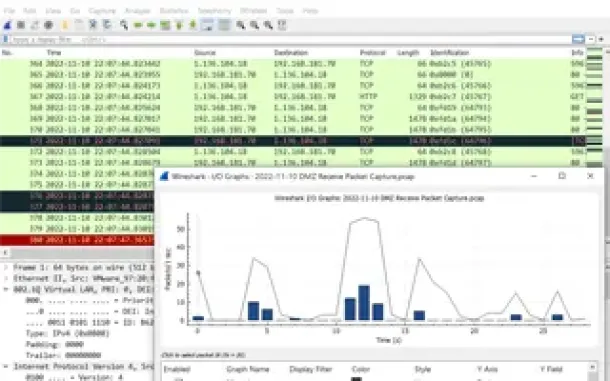
Network Fundamentals
The Importance of a Network Analyzer – Packet Sniffe...
Network Analyzers, also known as Packet Sniffers, are amongst the most popular network tools found inside any Network Engineer’s toolkit. A Network Anal...
Cisco Switches
VLAN Security Tips - Best Practices
This article focuses on VLAN Security and its implementation within the business network environment. We provide tips and Cisco CLI commands that will h...
Cisco CallManager-CCME
Connecting & Configuring SPA8000 with UC500, 520, 54...
When it comes to connecting multiple analog phones to VoIP systems like Cisco’s Unified Communication Manager Express (CallManager Express) or UC500 ser...
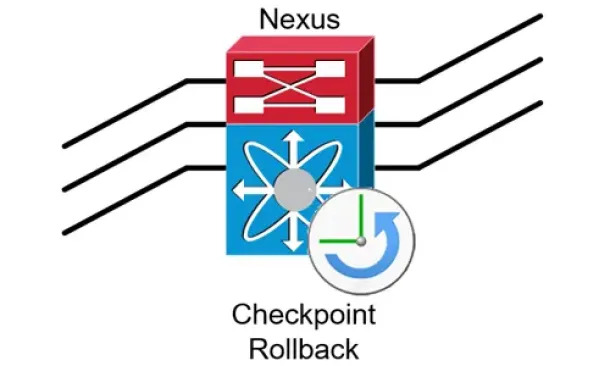
Cisco Data Center (Nexus/UCS)
Complete Guide to Nexus Checkpoint & Rollback Featur...
The Cisco NX-OS checkpoint feature provides the capability to capture at any time a snapshot (backup) of the Cisco Nexus configuration be...
Cisco CallManager-CCME
How to Upgrade - Update Cisco ATA186 / 188 Firmware ...
The Cisco ATA 186/188 device is well known amongst any Cisco VoIP engineer. It is used allow analog phone devices to connect to the VoIP network and fun...