Suggested Articles:
Network Protocol Analyzers
How to Detect Routing Loops and Physical Loops ...
When working with medium to large scale networks, IT departments are often faced dealing with network loops and broadcast storms that are caused by...

ManageEngine Firewall Analyzer
Challenges & Solutions to Managing Firewall Rul...
In today's interconnected digital landscape, where businesses rely heavily on networked systems and the internet for their operations, the importan...

ManageEngine Firewall Analyzer
Dealing with Security Audit Challenges: Discove...
The utilization of log analyzers, such as Firewall Analyzer, in network infrastructure plays a pivotal role in enhancing cybersecurity and fortifyi...
OpManager - Network Monitoring & Management
Network Management Systems Help Businesses Accu...
Accurately monitoring your organization’s business application performance, service provider SLA breaches, network infrastructure traffic, bandwidt...
Featured Subcategories:
WireShark Articles:
Detect Brute-Force Attacks with nChronos Networ...
Brute-force attacks are commonly known attack methods by which hackers try to get access to restricted accounts and data using an exhaustive list/d...
Introducing Colasoft Unified Performance Manage...
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, qua...
How to Detect P2P (peer-to-peer) File Sharing, ...
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing proce...
How to Use Multi-Segment Analysis to Troublesho...
Troubleshooting network problems can be a very intensive and challenging process. Intermittent network problems are even more difficult to troubles...
Your IP address:
3.139.240.142
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Palo Alto Networks
Palo Alto Networks Firewall - Web & CLI Initial Conf...
This article is the second-part of our Palo Alto Networks Firewall technical articles. Our previous article was introduction to Palo Alto Networks Firew...
Palo Alto Networks
Introduction to Palo Alto Next-Generation Network Fi...
During the past decade, we’ve seen the global IT security market flooded with new network security and firewall security appliances. New vendors emergin...
Palo Alto Networks
Complete Guide: Configuring IPSec VPN between Palo A...
This article will show you how to configure an IPSec VPN tunnel between a Palo Alto firewall (all PANOS versions) and Meraki MX security appliance. Our ...
Palo Alto Networks
The Benefits of Palo Alto Networks Firewall Single P...
What makes Palo Alto Networks Next-Generation Firewall (NGFW) so different from its competitors is its Platform, Process and Architecture. Palo Alto Net...
Windows Servers
Windows 2012 Server Foundation, Essential, Standard ...
FREE Hyper-V & VMware Virtualization Backup: FREE for Firewall.cx readers for a Limited Time! Download Now!
Windows Server 2012 Edition...
Windows Servers
Windows Server 2016 Licensing Made Easy – Understand...
This article describes the new Windows Server 2016 Licensing model (per-core licensing) Microsoft has implemented for its new server-based operating sys...
Windows Servers
Free Webinar: Scripting & Automation in Hyper-V with...
System Center Virtual Machine Manager (SCVMM) provides some great automation benefits for those organizations that can afford the hefty price tag. Howev...
Windows Servers
Windows Server 2016 VM Backup with Altaro's New VM B...
Altaro has released Altaro VM Backup, a faster and lighter upgrade to its flagship Hyper-V and VMware backup solution, which now supports all Windows Se...
Popular Topics
Routing
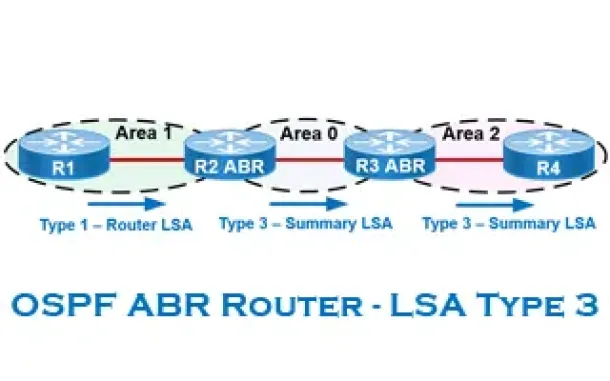
OSPF - Part 6: OSPF LSA Types - Purpose and Function...
Our previous article explained the purpose of Link State Update (LSU) packets and examined the Link State Advertisement (LSA) information contained with...
Windows Servers
Free Hyper-V eBook - Create, Manage and Troubleshoot...
With the introduction of Hyper-V on the Windows Server platform, virtualization has quickly become the de facto standard for all companies seeking to co...
VLAN Networks
The VLAN Concept - Introduction to VLANs
We hear about them everywhere, vendors around the world are constantly trying to push them into every type of network and as a result, the Local Area Ne...

Network Fundamentals
LAN Network Topologies
Network topologies can take a bit of time to understand when you're all new to this kind of cool stuff, but it's very important to fully understand them...
Cisco CallManager-CCME
How to Upgrade - Update Cisco ATA186 / 188 Firmware ...
The Cisco ATA 186/188 device is well known amongst any Cisco VoIP engineer. It is used allow analog phone devices to connect to the VoIP network and fun...
Cisco Services & Technologies
Troubleshooting Cisco VPN Client Windows 7 - How To ...
This article shows how to fix the Cisco VPN Reason 442: Failed to enable Virtual Adapter error on the Windows 7 (32bit or 64bit) operating system. If yo...
Cisco Routers
Resolving Cisco Router/Switch Tftp Problems: Source ...
When working with Cisco equipment that has multiple ip interfaces, a common problem engineers are faced with is trying to successfully tftp to or from t...
Cisco Routers
How and Why You Should Verify IOS Images On Cisco Ro...
Chances are we’ve all needed to upgrade our Cisco’s device IOS software at some point. While upgrading the IOS software on a Cisco device is considered ...