Network Fundamentals: Top Picks
Network Fundamentals
Hubs & Repeaters
Network hubs were once the primary method of interconnecting network devices to create a local area network (LAN). Hubs were inexpensive, easy to i...
Network Fundamentals
Introduction To Networking
A network is simply a group of two or more Personal Computers linked together. Many types of networks exist, but the most common types of networks ...
Network Fundamentals
Controlling Broadcasts and Multicasts
The first step in controlling broadcast and multicast traffic is to identify which devices are involved in a broadcast or multicast storm. The foll...
Network Fundamentals
Media Access Control - MAC Addresses
A MAC address, or Media Access Control address, is a unique identifier assigned to a network interface controller (NIC) for use as a network addr...
Featured Subcategories:
Netflow Articles:
Netflow
NetFlow Analyzer: Free Download, Step-by-Step I...
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows...
Netflow
Netflow vs SNMP. Two Different Approaches to Ne...
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ...
Netflow
Netflow: Monitor Bandwidth & Network Utilizatio...
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, appl...
Netflow
Complete Guide to Netflow: How Netflow & its Co...
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive i...
Network Protocols:
Domain Name System (DNS)
The DNS Protocol - Part 2: DNS Queries & Resolu...
This section will help you understand how the DNS queries work on the Internet and your home network. There are two ways to use the domain name sys...
Subnetting
IP Subnetting - Part 5: Subnetting Guidelines
There is always that day when you are called upon to provide a solution to a network problem. The number of problems that can occur in a network ar...
TCP - UDP Protocol Analysis
Transmission Control Protocol - Part 4: In-Dept...
This article is an introduction to the 7-page TCP Header analysis section that follows. We briefly view each section of the TCP Header and then mov...
IP Protocol
IP Protocol - Part 1: Binary & The Internet Pro...
To understand the Internet Protocol, we need to learn and understand Binary. It is very important to know and understand Binary because part of the...
Subnetting
IP Subnetting - Part 3: Subnet Mask Bits & Anal...
So we have covered to some depth the subnetting topic, but there is still much to learn ! We are going to explain here the available subnet masks a...
TCP - UDP Protocol Analysis
TCP Header Anaylsis - Section 6: TCP Options
The TCP Options (MSS, Window Scaling, Selective Acknowledgements, Timestamps, Nop) are located at the end of the TCP Header which is also why they ...
Supernetting & CIDR
Supernetting In-Depth Analysis - Learn to Ident...
Our previous article served as an introduction to Supernetting, also known as Route Summarization. We covered the concept of Supernetting, how it w...
Subnetting
IP Subnet Calculator
This free online Subnet Calculator provides a fast and easy way to calculate all aspects of any IP Address and Subnet Mask. Simply enter your des...
STP/ICMP Protocols:
ICMP Protocol
ICMP Protocol - Part 6: Redirect Messages
The ICMP - Redirect Message is always sent from a gateway to the host and the example below will illustrate when this is used.
Putting it simply (...
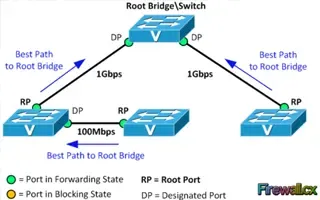
Spanning Tree Protocol (STP)
Spanning Tree Protocol – Part 2: Rapid STP Port...
Spanning Tree Protocol, Rapid STP port costs and port states are an essential part of the STP algorithm that affect how STP decides to forward or b...
ICMP Protocol
ICMP Protocol - Part 4: Destination Unreachable...
The 'ICMP Destination unreachable' message is quite interesting, because it doesn't actually contain one message, but infact six! This means that t...
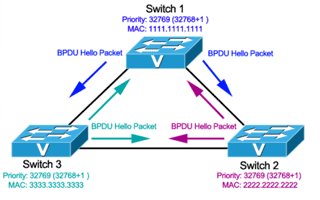
Spanning Tree Protocol (STP)
Spanning Tree Protocol – Part 3: Bridge ID, Pri...
In this article we will examine the Spanning Tree Bridge ID structure, explain why it has increments of 4096, how VLAN information is embedded (for...
Your IP address:
18.222.104.196
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
VLAN Networks
VTP Protocol - In-Depth Analysis
The previous article introduced the VTP protocol, we examined how it can be used within a network, to help manage VLANs and ease the administrative over...

VLAN Networks
InterVLAN Routing - Routing between VLAN Networks
This article deals with the popular topic of InterVLAN routing, which is used to allow routing & communication between VLAN networks. Our article an...

VLAN Networks
VTP Pruning
VTP (VLAN Trunking Protocol) pruning is a feature that is used in Cisco switches to reduce unnecessary traffic in VLAN (Virtual Local Area Network) trun...
VLAN Networks
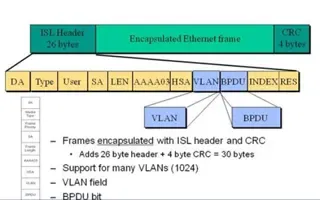
VLAN InterSwitch Link (ISL) Protocol Analysis
Deciding whether to use ISL or IEEE 802.1q to power your trunk links can be quite confusing if you cannot identify the advantages and disadvantages of e...
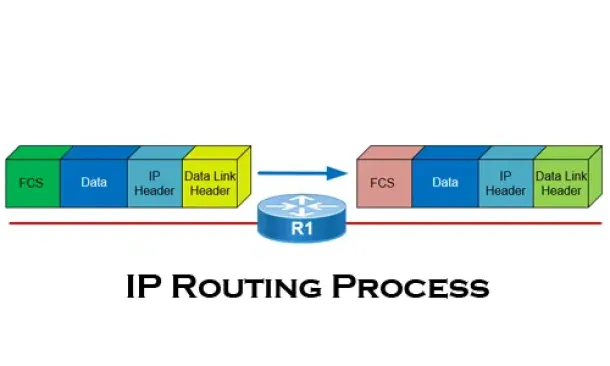
Routing
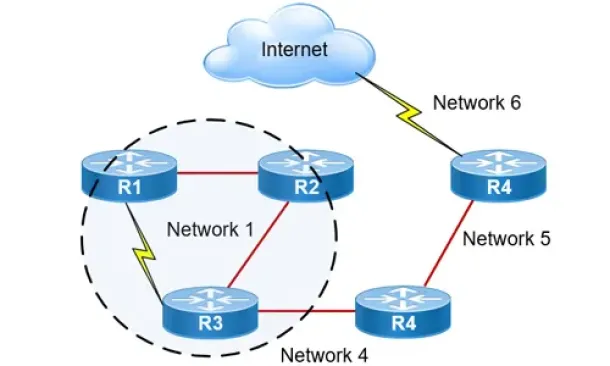
The IP Routing Process - Step-by-Step Analysis
We are going to analyse what happens when routing occurs on a network (IP routing process). When I was new to the networking area, I thought that all yo...
Routing
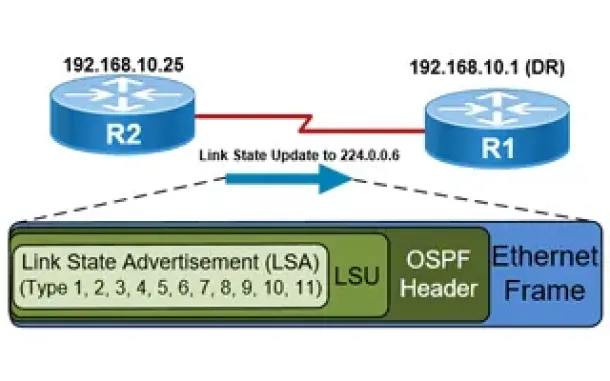
OSPF - Part 5: Analysis of OSPF Link State Update (L...
This article explains how OSPF uses Link State Advertisement (LSA) to exchange information about the network topology between routers. When a router rec...
Routing
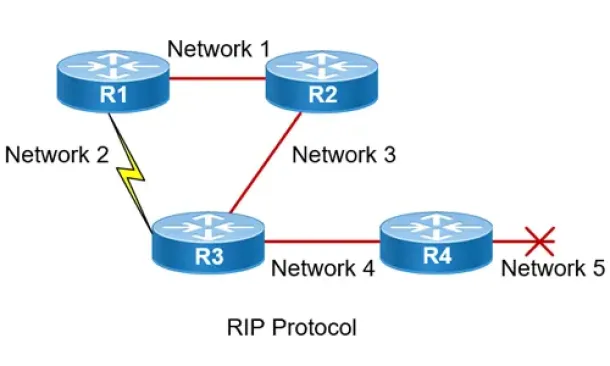
Routing Information Protocol - RIP
Routing Information Protocol (RIP) is a distance-vector routing protocol that is commonly used in small to medium-sized networks. It is one of the...
Routing
Hybrid Routing Protocols - Advantages and Disadvanta...
Hybrid routing protocols are a combination of distance-vector and link-state routing protocols, and are used to provide a more efficient and scala...
Network Address Translation - NAT
Network Address Translation (NAT) Concepts
Before we dive into the deep waters of NAT, we need to make sure we understand exactly what NAT does. So let me give you the background of NAT, why it's...
Network Address Translation - NAT
Dynamic NAT - Part 1
Dynamic NAT is the second NAT mode we're going to talk about. Dynamic NAT, like Static NAT, is not that common in smaller networks but you'll find it us...
Network Address Translation - NAT
The Network Address Translation Table
After that simple and informative introduction to the NAT concept, it's time to find out more about how it works and this is where the NAT table comes i...
Network Address Translation - NAT
Dynamic NAT - Part 2
Our previous article, Dynamic NAT - Part 1, covered the basic idea of Dynamic Network Address Translation. We are now going to take a closer look at the...