-
 HornetSecurity
HornetSecurityAll-in-one protection for Microsoft 365
All-in-one protection for Microsoft 365
-
 ManageEngine
ManageEngineOpManager: Network & DC Monitoring
Monitor & Manage Network, Datacenters, endpoints & more.
-

Latest Articles
Detecting Windows Server Security Threats with Advanced Event Log Analyzers
 Windows Servers stand as prime targets for hackers and malicious actors due to their widespread usage and historical vulnerabilities. These systems often serve as the backbone for critical business operations, housing sensitive data and facilitating essential services. However, their prevalence also makes them vulnerable to cyber threats, including ransomware attacks, distributed denial-of-service (DDoS) assaults and more.
Windows Servers stand as prime targets for hackers and malicious actors due to their widespread usage and historical vulnerabilities. These systems often serve as the backbone for critical business operations, housing sensitive data and facilitating essential services. However, their prevalence also makes them vulnerable to cyber threats, including ransomware attacks, distributed denial-of-service (DDoS) assaults and more.
Windows Servers have a documented history of vulnerabilities and exploits, which further intensifies their attractiveness to attackers seeking to exploit weaknesses for unauthorized access or data theft. Consequently, it is paramount for organizations to prioritize mitigating these risks and safeguarding the integrity and continuity of operations within Windows Server environments.
Fortunately, tools like EventLog Analyzer offer robust capabilities for automatically identifying and countering such threats, uplifting the security posture of Windows Server setups. To effectively leverage these defenses, it's imperative to understand the nature of common Windows server threats and how they manifest. In this document, we delve into several prevalent threats targeting Windows servers and outline strategies for their detection and mitigation.
Furthermore, implementing robust security measures, such as regular patching, network segmentation, intrusion detection systems, and data encryption, Windows VM Backups, is essential to fortify Windows Servers against potential threats and ensure the resilience of critical business functions.
Key Topics:
- Common Windows Server Threats
- Ransomware
- Denial of Service Attacks
- Insider Threats
- Malware Infections
- Phishing Attacks
- Brute Force Attacks
- Vulnerability Exploitation
- Data Breaches
- Web Application Attacks
- Misconfiguration Errors
- Using Advanced Event Log Analyzers to Detect Server Threats
- EventLog Analyzer: Ransomware Detection
- EventLog Analyzer: DoS Attack Detection
- EventLog Analyzer: Insider Threat Detection
- Moving Forward with Robust Log Management Solutions
- Summary
Download now the world’s leading Event Log Management System.
Common Windows Server Threats
Boost Your Microsoft 365 Security with Expert Guidance and Proven Best Practices
 This article serves as a comprehensive guide to fortifying the security posture of Microsoft 365, covering essential aspects ranging from foundational security principles to advanced strategies for optimizing productivity without compromising security. From introducing the fundamental Microsoft 365 Security Essentials to defining proactive measures such as regular audits, secure configurations, and Data Loss Prevention (DLP) protocols, this guide equips organizations with the knowledge necessary to establish a resilient security framework.
This article serves as a comprehensive guide to fortifying the security posture of Microsoft 365, covering essential aspects ranging from foundational security principles to advanced strategies for optimizing productivity without compromising security. From introducing the fundamental Microsoft 365 Security Essentials to defining proactive measures such as regular audits, secure configurations, and Data Loss Prevention (DLP) protocols, this guide equips organizations with the knowledge necessary to establish a resilient security framework.
Furthermore, the article delves into protecting user identities and sensitive data, proven strategies such as Multi-Factor Authentication (MFA), identity protection mechanisms, and data encryption techniques. By prioritizing these measures, businesses can mitigate the risk of unauthorized access and data breaches, thereby bolstering trust and compliance with regulatory standards.
Moreover, the article explores how organizations can optimize security measures to enhance productivity, emphasizing the role of role-based access control (RBAC), security awareness training, and the utilization of security dashboards and reports. By integrating security seamlessly into daily workflows, businesses can foster a culture of vigilance while empowering employees to navigate digital environments securely.
Key Topics:
- Introduction to Microsoft 365 Security Essentials
- How to Implement Proactive Security Measures
- Protecting User Identities and Data
- Learn More About Safeguarding Against Common Threats
- Optimizing Security for Enhanced Productivity
- Summary
Introduction to Microsoft 365 Security Essentials
Challenges & Solutions to Managing Firewall Rules in Complex Network Environments
 In today's interconnected digital landscape, where businesses rely heavily on networked systems and the internet for their operations, the importance of cybersecurity cannot be overstated. Among the essential tools in a cybersecurity arsenal, firewalls stand as a frontline defense against cyber threats and malicious actors.
In today's interconnected digital landscape, where businesses rely heavily on networked systems and the internet for their operations, the importance of cybersecurity cannot be overstated. Among the essential tools in a cybersecurity arsenal, firewalls stand as a frontline defense against cyber threats and malicious actors.
One of the primary functions of a firewall is to filter traffic, which entails scrutinizing packets of data to determine whether they meet the criteria set by the organization's security policies. This process involves examining various attributes of the data packets, such as source and destination IP addresses, port numbers, and protocols. By enforcing these rules, firewalls can thwart a wide range of cyber threats, including unauthorized access attempts, malware infections, denial-of-service attacks and more.
Enforcing and managing firewall rules effectively can be a daunting task, particularly in complex network environments with numerous rules, policies and configurations. While solutions like ManageEngine Firewall Analyzer step in, to offer a comprehensive way to streamline firewall rule management and enhance security posture, it’s worthwhile take a look at the real challenges firewall rule management present across all known platforms such as Cisco (FTD, Firepower, ASA), Palo AltoPalo Alto Next-Gen firewalls, Checkpoint, Fortinet, Juniper and more.
Key Topics:
- Challenges in Firewall Rule Management
- How to Simplify Firewall Rules
- The Benefits of Effective Firewall Rule Management
- Summary
Challenges with Firewall Rule Management
Configuring QoS on Palo Alto Firewalls: Class-based Policies, QoS Profiles, Enabling QoS on Firewall Interfaces
 This article’s purpose is to help you quickly master Palo Alto QoS concepts and learn to configure QoS on Palo Alto Firewalls in a simple and efficient way. QoS is considered a complicated topic however thanks to Palo Alto’s intuitive firewall GUI interface and our real-scenarios, you’ll quickly grasp all necessary QoS basics and be ready to implement your own QoS policies!
This article’s purpose is to help you quickly master Palo Alto QoS concepts and learn to configure QoS on Palo Alto Firewalls in a simple and efficient way. QoS is considered a complicated topic however thanks to Palo Alto’s intuitive firewall GUI interface and our real-scenarios, you’ll quickly grasp all necessary QoS basics and be ready to implement your own QoS policies!
You’ll learn basic QoS terms such as Ingress and Egress traffic, Differentiated Service Code Point (DSCP), Traffic Policing, Traffic Shaping, Palo Alto QoS Classes, Palo Alto QoS Policies, how to build Palo Alto QoS policies, how to configure Palo Alto QoS Classes and finally how to enable and monitor QoS on Palo Alto firewall interfaces (both standalone & AE Aggregate interfaces), view QoS bandwidth graphs and more!
Key Topics:
- Introduction to Palo Alto QoS
- Palo Alto QoS Classes
- Palo Alto QoS Policies
- Configuring QoS Class-based Policies & Profiles
- Enabling QoS on Palo Alto Firewall Physical & Aggregate (AE) Interfaces
- Summary
Find more great articles by visiting our Palo Alto Firewall Section.
Introduction to Palo Alto QoS
QoS was born from the IEEE group during 1995-1998 by establishing the standard IEEE 802.1P. The main purpose of QoS is to prioritise desired traffic over other type of traffic or to limit the amount of bandwidth applications can consume, by utilizing different mechanisms. This ensures network performance, avoids bottlenecks, congestion or overutilization of network links. A frequently used example of QoS is the prioritising Real-time traffic e.g voice or video, over other type of traffic:
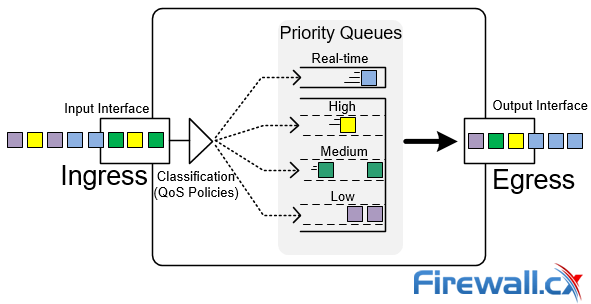 QoS Priority Queues - Packet classification and prioritization
QoS Priority Queues - Packet classification and prioritization
In the example above, voice packets (blue) are given a higher priority against others, therefore immediately being forwarded by the firewall out via the output interface. Since voice packets are very sensitive to delay, they are usually handled with priority to avoid issues in a real-time voice streams e.g VoIP telephone call between two endpoints.
Overview of QoS Configuration on Palo Alto Firewalls
Your IP address:
18.225.56.251
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Featured Categories:
Top Picks:
6 Key Areas to Consider When Selecting a VM Bac...
Palo Alto Firewall Configuration Options. Tap M...
Complete Guide: Configuring IPSec VPN between P...
Palo Alto Firewall Application-based Policy Enf...
Check Point Software and Cato Networks Co-Founder Shlomo Kramer Shares His Journey: From ‘Firewall-1’ Software to Today’s Firewall as a Service
MPLS vs. SD-WAN vs. Internet vs. Cloud Network. Connectivity, Optimization and Security Options for the ‘Next Generation WAN’
How To Secure Your SD-WAN. Comparing DIY, Managed SD-WAN and SD-WAN Cloud Services
Key Features of a True Cloud-Native SASE Service. Setting the Right Expectations

Static VLANs

Comparing Traditional Flat & VLAN Networks

InterVLAN Routing - Routing between VLAN Networks
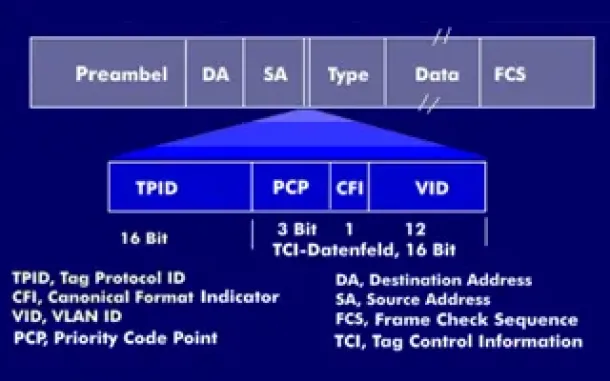
VLAN Tagging - Understanding VLANs Ethernet Frames
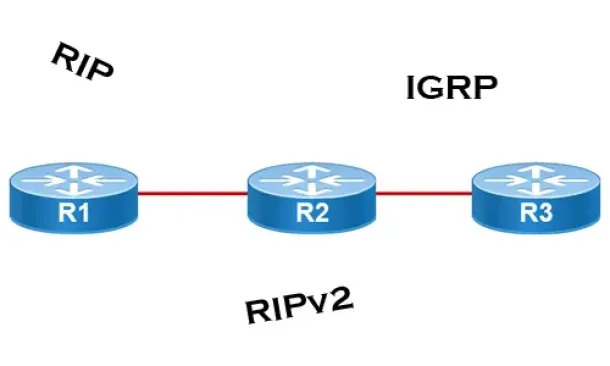
Distance Vector Routing Protocols
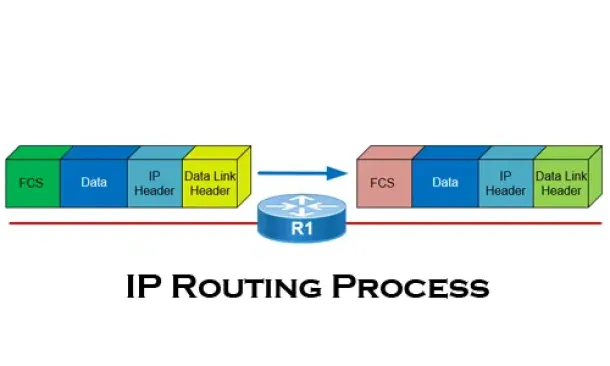
The IP Routing Process - Step-by-Step Analysis
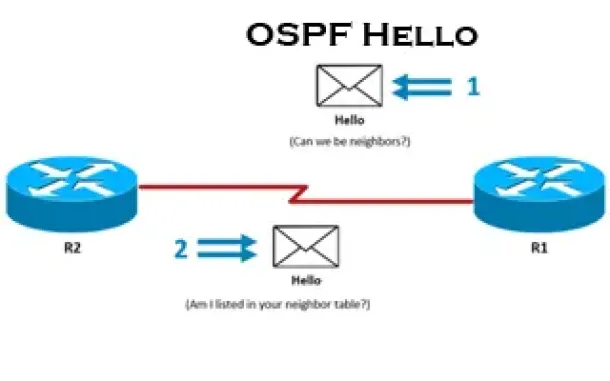
OSPF - Part 3: OSPF Adjacency & Neighbor Forming Process. OSPF Hello Messages, OSPF Database Updates via Link State Requests (LSR & LSU)