Network Management Articles:

Netflow
Netflow: Monitor Bandwidth & Network Utilizatio...
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, application traffic and data flows allows network engi...
OpManager - Network Monitoring & Management
Ensuring Enterprise Network Readiness for Mobil...
Demands for Enterprise networks to properly support mobile users is on a continuous rise making it more than ever necessary for IT departments to provide high-quality services to its users. This ar...

ManageEngine Firewall Analyzer
Challenges & Solutions to Managing Firewall Rul...
In today's interconnected digital landscape, where businesses rely heavily on networked systems and the internet for their operations, the importance of cybersecurity cannot be overstated. Among th...

Netflow
NetFlow Analyzer: Free Download, Step-by-Step I...
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows while at the same time analyze traffic patterns, ...
Featured Subcategories:
Network Protocol Analyzer Articles:
Network Protocol Analyzers
How to Perform TCP SYN Flood DoS Attack & Detec...
This article will help you understand TCP SYN Flood Attacks, show how to perform a SYN Flood Attack (DoS attack) using Kali Linux & hping3 and correctly identify one using the Wireshark protoco...
Network Protocol Analyzers
How to Detect P2P (peer-to-peer) File Sharing, ...
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing processes that not only consumes valuable bandwidth, bu...
Network Protocol Analyzers
Introducing Colasoft Unified Performance Manage...
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, quality, fault, and security issues based on business...
Network Protocol Analyzers
How to Detect SYN Flood Attacks with Capsa Netw...
This article explains how to detect a SYN Flood Attack using an advanced protocol analyser like Colasoft Capsa. We’ll show you how to identify and inspect abnormal traffic spikes, drill into captur...
Virtualization & VM Backup:
Virtualization & VM Backup
6 Key Areas to Consider When Selecting a VM Bac...
Backup and Disaster recovery are core considerations for any business with an IT footprint, whether that is on-premises or in the cloud.
Your business depends on reliable IT systems to support the...
Virtualization & VM Backup
World Backup Day with Free Amazon Voucher and P...
Celebrate World Backup Day and WIN with Altaro!
We all remember how grateful we were to have backup software when facing so many data loss mishaps and near-catastrophes.
If you manage your com...
Virtualization & VM Backup
How to Enable or Disable SSH on VMware ESXi via...
SSH access to VMware’s ESXi server is by disabled by default however there are many reasons where SSH might be required. VMware and System administrators often find the need to perform advanced adm...
Virtualization & VM Backup
How to Fix VMware ESXi Virtual Machine 'Invalid...
In this article, we'll show you how to deal with VMs which are reported to have an Invalid Status as shown in the screenshot below. This is a common problem many VMware and System Adminis...
Firewall Articles:
Cisco Firewalls
Cisco ASA5500 (5505, 5510, 5520, etc) Series Fi...
The Cisco ASA 5500 series security appliances have been around for quite some time and are amongst the most popular hardware firewalls available in the market. Today Firewall.cx takes a look at how...
Palo Alto Networks
Palo Alto Firewalls Security Zones – Tap Zone, ...
Palo Alto Networks Next-Generation Firewalls rely on the concept of security zones in order to apply security policies. This means that access lists (firewall rules) are applied to zones and not in...
Palo Alto Networks
How to Fix Palo Alto Firewall “Error: Image Fil...
Keeping your Palo Alto Firewall up to date with the latest PAN-OS software updates is an important step to ensure your organization is protected against the PAN-OS latest software vulnerabilities, ...
Cisco Firewalls
Demystifying Cisco AnyConnect 4.x Licensing. Pl...
In late 2014, Cisco announced the new licensing model for the latest AnyConnect Secure Mobility client v4.x. With this new version, Cisco introduced a number of new features, but also simplified th...
Your IP address:
18.221.85.100
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Top Picks
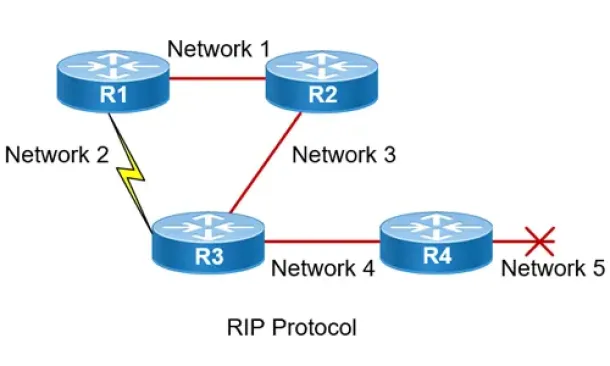
Routing
Routing Information Protocol - RIP
Routing Information Protocol (RIP) is a distance-vector routing protocol that is commonly used in small to medium-sized networks. It is one o...
Windows Servers
How to Install and Configure Windows 2012 DNS Server Role
Our previous article covered introduction to the Domain Name System (DNS) and explained the importance of the DNS Server role within the network in...
Windows Servers
Windows 2016 Server Licensing Explained – Free Webinar
With Windows 2016 Server already making its way into data centers Windows 2016 Server Licensing is becoming a very hot topic. Windows 2016 Server i...
Windows Servers
Easy, Fast & Reliable Hyper-V & VMware Backup with Altaro's Free Backup Solution
As more companies around the world adopt the virtualization technology to increase efficiency and productivity, Microsoft’s Hyper-V virtualization ...