Network Fundamentals: Top Picks
Network Fundamentals
Measuring Network Performance: Test Network Thr...
Measuring network performance has always been a difficult and unclear task, mainly because most engineers and administrators are unsure which appro...
Network Fundamentals
Media Access Control - MAC Addresses
A MAC address, or Media Access Control address, is a unique identifier assigned to a network interface controller (NIC) for use as a network addr...
Network Fundamentals
Firewall Topologies
In this section we are going to talk about the different ways a firewall can be set up. Depending on your needs, you can have a very simple firewal...
Network Fundamentals
Need for Speed – The Data Tsunami & Advancement...
A long-long time ago (not long ago in earth time) 100 Mbps was THE technology. 100 Mbps uplinks bundled with ether-channel was the ultimate uplink ...
Featured Subcategories:
Netflow Articles:
Netflow
Complete Guide to Netflow: How Netflow & its Co...
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive i...
Netflow
Netflow vs SNMP. Two Different Approaches to Ne...
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ...
Netflow
NetFlow Analyzer: Free Download, Step-by-Step I...
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows...
Netflow
Netflow: Monitor Bandwidth & Network Utilizatio...
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, appl...
Network Protocols:
Domain Name System (DNS)
The DNS Protocol - Part 2: DNS Queries & Resolu...
This section will help you understand how the DNS queries work on the Internet and your home network. There are two ways to use the domain name sys...
Subnetting
IP Subnet Calculator
This free online Subnet Calculator provides a fast and easy way to calculate all aspects of any IP Address and Subnet Mask. Simply enter your des...
Domain Name System (DNS)
The DNS Protocol - Part 1: Introduction
If you ever wondered where DNS came from, this is your chance to find out ! The quick summary on DNS's history will also help you understand why DN...
Domain Name System (DNS)
The DNS Protocol - Part 3: DNS Query Message Fo...
This section will deal with the analysis of the DNS packets by examining how DNS messages are formatted and the options and variables they contain....
IP Protocol
IP Protocol - Part 3: IP Classes, Network & Hos...
This article explains the 'Network-ID' and 'Host-ID' concept found in IP addressing and subnetting. We analyse the structure of IP addresses and ne...
TCP - UDP Protocol Analysis
TCP Header Anaylsis - Section 7: TCP Data Paylo...
Finally, the last page of our incredible TCP Analysis. As most of you would expect, this section is dedicated to the DATA section that follows the ...
TCP - UDP Protocol Analysis
Transmission Control Protocol - Part 4: In-Dept...
This article is an introduction to the 7-page TCP Header analysis section that follows. We briefly view each section of the TCP Header and then mov...
Domain Name System (DNS)
The DNS Protocol - Part 4: DNS Response Message...
The previous article covered the DNS Query message formats. In the article we analysed them in great detail and showed how various options are sele...
STP/ICMP Protocols:
ICMP Protocol
ICMP Protocol - Part 4: Destination Unreachable...
The 'ICMP Destination unreachable' message is quite interesting, because it doesn't actually contain one message, but infact six! This means that t...
ICMP Protocol
ICMP Protocol - Part 1: Introduction
The Internet Control Message Protocol (ICMP), is a very popular protocol and actually part of an Internet Protocol (IP) implementation. Because IP ...
ICMP Protocol
ICMP Protocol - Part 6: Redirect Messages
The ICMP - Redirect Message is always sent from a gateway to the host and the example below will illustrate when this is used.
Putting it simply (...
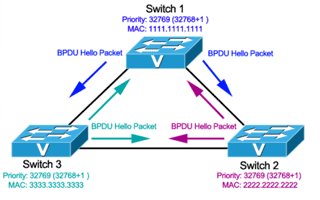
Spanning Tree Protocol (STP)
Spanning Tree Protocol – Part 3: Bridge ID, Pri...
In this article we will examine the Spanning Tree Bridge ID structure, explain why it has increments of 4096, how VLAN information is embedded (for...
Your IP address:
18.191.204.211
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
VLAN Networks
VTP Protocol - In-Depth Analysis
The previous article introduced the VTP protocol, we examined how it can be used within a network, to help manage VLANs and ease the administrative over...

VLAN Networks
Dynamic VLANs
Dynamic VLANs were introduced to grant the flexibility and complexity(!) that Static VLANs did not provide. Dynamic VLANs are quite rare because of thei...

VLAN Networks
Static VLANs
VLANs are usually created by the network administrator, assigning each port of every switch to a VLAN. Depending on the network infrastructure and secur...

VLAN Networks
VTP Introduction & Modes
The invention of VLANs was very much welcomed by all engineers and administrators, allowing them to extend, redesign and segment their existing network ...
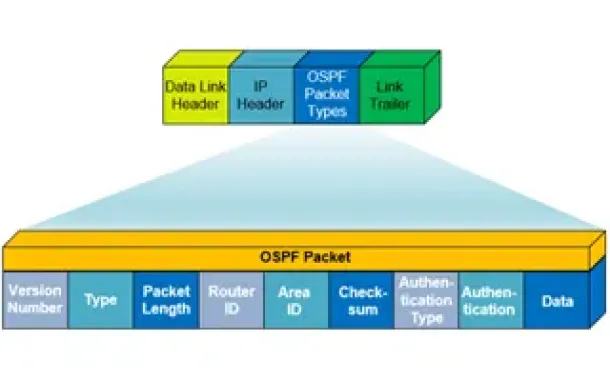
Routing
OSPF - Part 1: Introduction, OSPF Packet Structure, ...
Open Shortest Path First (OSPF) is a popular routing protocol developed for Internet Protocol (IP) networks by the Interior Gateway Protocol (IGP) worki...

Routing
Interior Gateway Protocol - IGRP
IGRP (Interior Gateway Routing Protocol) is a Cisco proprietary distance-vector routing protocol used in enterprise networks to exchange routing informa...

Routing
Enhanced Interior Gateway Routing Protocol - EIGRP
Enhanced Interior Gateway Routing Protocol (EIGRP), similar to IGRP, is a Cisco proprietary routing protocol that is used to exchange routing informatio...
Routing
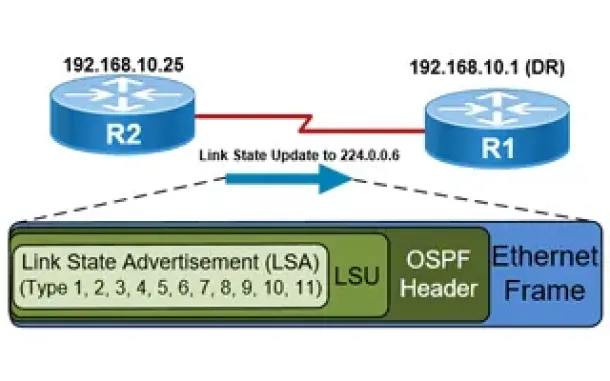
OSPF - Part 5: Analysis of OSPF Link State Update (L...
This article explains how OSPF uses Link State Advertisement (LSA) to exchange information about the network topology between routers. When a router rec...
Network Address Translation - NAT
Dynamic NAT - Part 1
Dynamic NAT is the second NAT mode we're going to talk about. Dynamic NAT, like Static NAT, is not that common in smaller networks but you'll find it us...
Network Address Translation - NAT
Static NAT - Part 1
Static NAT (also called inbound mapping) is the first mode we're going to talk about and also happens to be the most uncommon between smaller networks.
...
Network Address Translation - NAT
Network Address Translation (NAT) Overload - Part 2
In our previous article, Network Address Translation (NAT) Overload - Part 1, we explained what NAT Overload is and how it works. This page deals with t...
Network Address Translation - NAT
Dynamic NAT - Part 2
Our previous article, Dynamic NAT - Part 1, covered the basic idea of Dynamic Network Address Translation. We are now going to take a closer look at the...