Suggested Articles:

Network Fundamentals
Introduction To Networking
A network is simply a group of two or more Personal Computers linked together. Many types of networks exist, but the most common types of networks ...
Subnetting
IP Subnet Calculator
This free online Subnet Calculator provides a fast and easy way to calculate all aspects of any IP Address and Subnet Mask. Simply enter your des...

Network Fundamentals
Power over Ethernet - Understanding PoE Technol...
Power over Ethernet (PoE) was invented by PowerDsine back in 1997 and the first power injector (Midspan) was installed in 1998! Many manufacturespa...

Network Fundamentals
Securing Your Home Network
In today's world, securing your home network is more important than ever. With the increasing number of cyberattacks, data breaches, and online fra...
Featured Subcategories:
Netflow Articles:
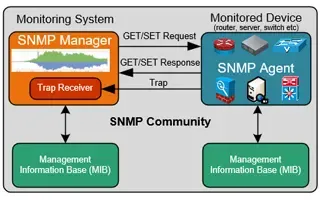
Netflow vs SNMP. Two Different Approaches to Ne...
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ...

NetFlow Analyzer: Free Download, Step-by-Step I...
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows...

Netflow: Monitor Bandwidth & Network Utilizatio...
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, appl...
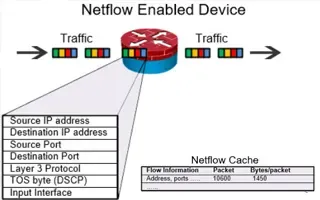
Complete Guide to Netflow: How Netflow & its Co...
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive i...
Your IP address:
18.226.82.163
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!

VLAN Networks
VTP Pruning
VTP (VLAN Trunking Protocol) pruning is a feature that is used in Cisco switches to reduce unnecessary traffic in VLAN (Virtual Local Area Network) trun...

VLAN Networks
VTP Protocol - In-Depth Analysis
The previous article introduced the VTP protocol, we examined how it can be used within a network, to help manage VLANs and ease the administrative over...

VLAN Networks
InterVLAN Routing - Routing between VLAN Networks
This article deals with the popular topic of InterVLAN routing, which is used to allow routing & communication between VLAN networks. Our article an...
VLAN Networks
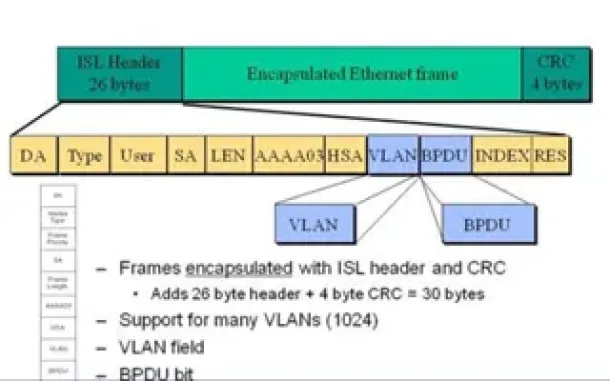
VLAN InterSwitch Link (ISL) Protocol Analysis
Deciding whether to use ISL or IEEE 802.1q to power your trunk links can be quite confusing if you cannot identify the advantages and disadvantages of e...

Routing
Link State Routing Protocols
Link State routing protocols do not view networks in terms of adjacent routers and hop counts, but they build a comprehensive view of the overall networ...
Routing
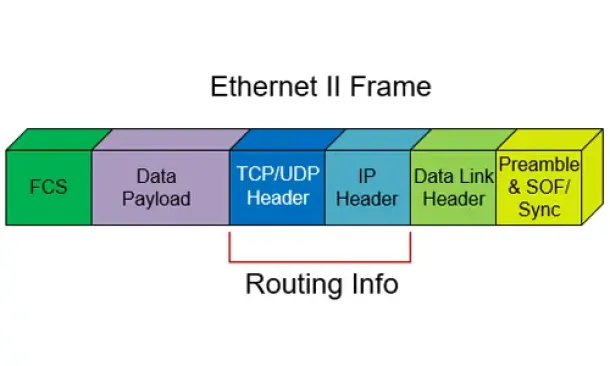
Routed Protocols
We all understand that TCP/IP, IPX-SPX are protocols which are used in a Local Area Network (LAN) so computers can communicate between with each other a...
Routing
Hybrid Routing Protocols - Advantages and Disadvanta...
Hybrid routing protocols are a combination of distance-vector and link-state routing protocols, and are used to provide a more efficient and scala...
Routing
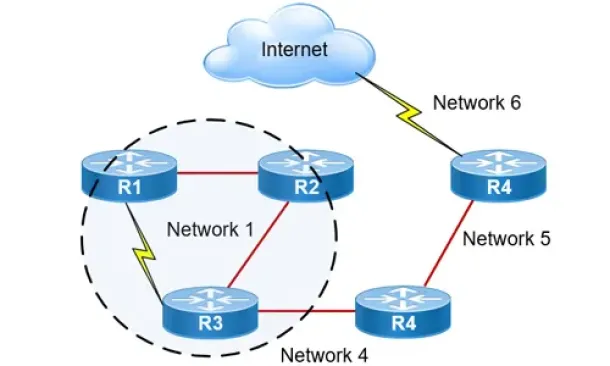
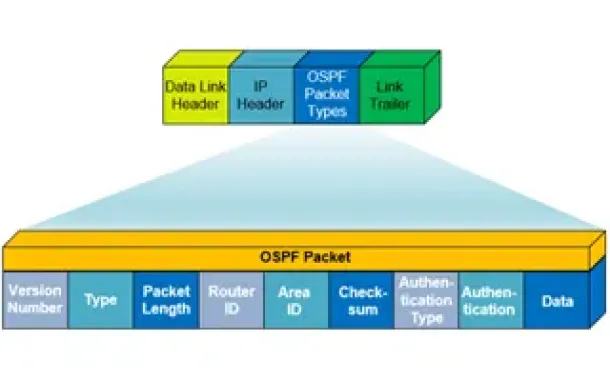
OSPF - Part 1: Introduction, OSPF Packet Structure, ...
Open Shortest Path First (OSPF) is a popular routing protocol developed for Internet Protocol (IP) networks by the Interior Gateway Protocol (IGP) worki...
Cisco Switches
Configuring SPAN On Cisco Catalyst Switches - Monito...
Being able to monitor your network traffic is essential when it comes to troubleshooting problems, performing a security audit or even casually checking...
Windows Servers
Windows 2012 Server Foundation, Essential, Standard ...
FREE Hyper-V & VMware Virtualization Backup: FREE for Firewall.cx readers for a Limited Time! Download Now!
Windows Server 2012 Edition...
Windows Servers
Installing Windows Server 2012 Active Directory via ...
This article serves as an Active Directory tutorial covering installation and setup of a Windows 2012 Domain Controller using Windows Server Manager (GU...
Cisco Routers
Configuring PPTP (VPDN) Server On A Cisco Router
The Point to Point Tunneling Protocol (PPTP) is a network protocol used to create VPN tunnels between public networks. These VPN tunnels are encrypted f...