Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
ICMP Protocol - Part 1: Introduction
| Read |
Suggested Articles:
Network Cabling
Unshielded Twisted Pair (UTP) - CAT 1 to CAT5, ...
Unshielded Twisted Pair (UTP) cable is most certainly by far the most popular cable around the world. UTP cable is used not only for networking but...
Ethernet Protocol, CSMA/CD, Collisions
Differences Between Classic Ethernet And Fast E...
The two primary areas for concern when upgrading the network from 10Mbps to 100Mbps are cabling and hubs. As discussed on the Fast Ethernet Introdu...
Network Address Translation - NAT
The Network Address Translation Table
After that simple and informative introduction to the NAT concept, it's time to find out more about how it works and this is where the NAT table co...
Network Fundamentals
Network Broadcast
The term "Broadcast" is used very frequently in the networking world . You will see it in most networking books and articles, or see it happening o...
Featured Subcategories:
Netflow Articles:

Netflow: Monitor Bandwidth & Network Utilizatio...
Monitoring network traffic & bandwidth usage via Netflow is mandatory for any type and size network. Gaining visibility into user traffic, appl...

Netflow vs SNMP. Two Different Approaches to Ne...
SNMP (Simple Network Management Protocol) and Netflow are both popular protocols with admins, prized for their ability to give visibility over the ...

NetFlow Analyzer: Free Download, Step-by-Step I...
In our previous article we explained how a Netflow Analyzer can help you gain visibility into your user traffic, application traffic and data flows...

Complete Guide to Netflow: How Netflow & its Co...
This article will cover the basics of Netflow, including its use cases, Netflow supported devices, Netflow history, and variants. We’ll also dive i...
Your IP address:
3.137.178.133
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
VLAN Networks
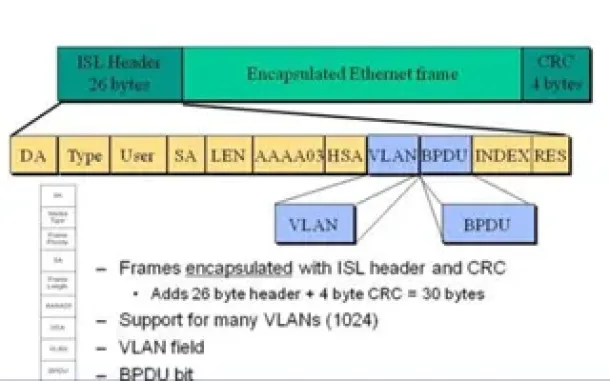
VLAN InterSwitch Link (ISL) Protocol Analysis
Deciding whether to use ISL or IEEE 802.1q to power your trunk links can be quite confusing if you cannot identify the advantages and disadvantages of e...
VLAN Networks
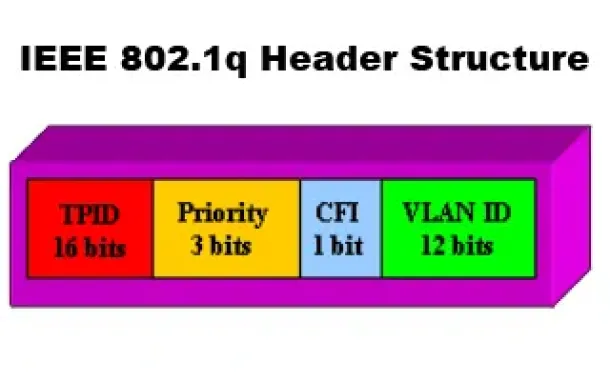
VLANs - IEEE 802.1q Trunk Link Protocol Analysis
While the VLAN Tagging article briefly covered the IEEE 802.1q protocol this article will continue building upon it by further analyzing the IEEE 802.1q...

VLAN Networks
VLAN Tagging - Understanding VLANs Ethernet Frames
We mentioned that Trunk Links are designed to pass frames (packets) from all VLANs, allowing us to connect multiple switches together and independently ...
VLAN Networks
VLAN Security - Making the Most of VLANs
It's easy to see why virtual LANs have become extremely popular on networks of all sizes. In practical terms, multiple VLANs are pretty much the same as...
Routing
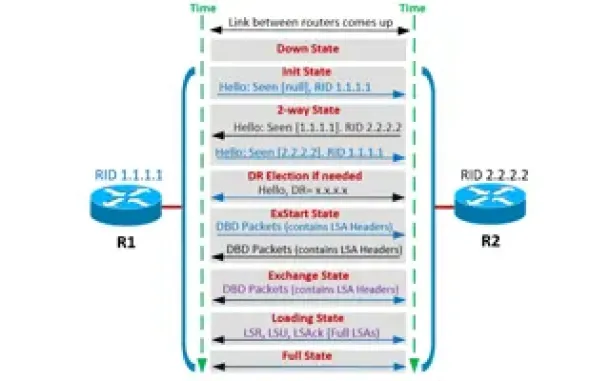
OSPF - Part 4: OSPF Neighbor States – OSPF Neighbor ...
This is the third article of our OSPF series which analyzes the different OSPF States routers go through during the OSPF discovery and neighbor forming ...
Routing
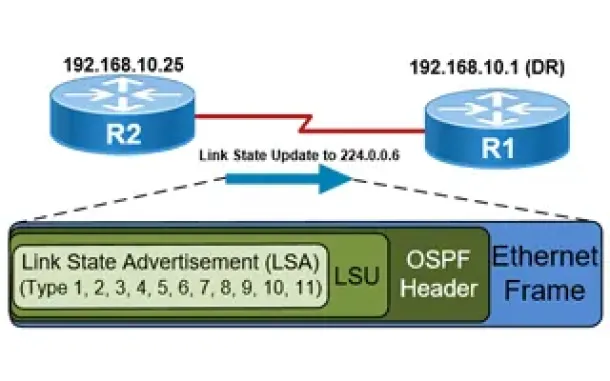
OSPF - Part 5: Analysis of OSPF Link State Update (L...
This article explains how OSPF uses Link State Advertisement (LSA) to exchange information about the network topology between routers. When a router rec...
Routing
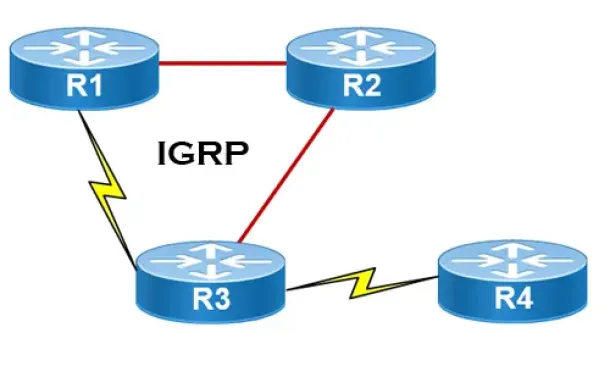
Interior Gateway Protocol - IGRP
IGRP (Interior Gateway Routing Protocol) is a Cisco proprietary distance-vector routing protocol used in enterprise networks to exchange routing informa...

Routing
OSPF - Part 3: OSPF Adjacency & Neighbor Forming Pro...
This is the thrid article of our 6-part OSPF series (see below) that describes how OSPF routers perform neighbor relationship and adjacency. We’ll exami...
SASE & SD-WAN Networks
Check Point Software and Cato Networks Co-Founder Sh...
By: Shlomo Kramer, Check Point Software & Cato Networks Co-Founder
As one of the founders of Check Point Software and more recently Cato Networks, ...
Network Protocol Analyzers
How to Detect SYN Flood Attacks with Capsa Network P...
This article explains how to detect a SYN Flood Attack using an advanced protocol analyser like Colasoft Capsa. We’ll show you how to identify and inspe...

Windows Servers
Deploying Active Directory & DNS Services on Windows...
This article provides a comprehensive guide to deploying Active Directory and DNS Services on Windows Server 2022, encompassing the Essential, Standard,...
Windows Servers
The Importance of a Comprehensive Backup Strategy fo...
People and companies usually adopt a backup strategy suited to the needs of their working environment. As such, there is no absolute right or wrong meth...




















