Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
|
Articles:
Renaming Windows 2000 Domain Name
| Read |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
MS Server Articles:
Windows Servers
Easy, Fast & Reliable Hyper-V & VMware Backup wit…
As more companies around the world adopt the virtualization technology to increase efficiency and productivity, Microsoft’s Hyper-V virtualization pl…
Windows Servers
Free Webinar & eBook on Microsoft Licensing for V…
Microsoft Licensing for Virtual environments can become a very complicated topic, especially with all the misconceptions and false information out th…
Windows Servers
Installing Windows Server 2012 Active Directory v…
This article serves as an Active Directory tutorial covering installation and setup of a Windows 2012 Domain Controller using Windows Server Manager…
Windows Servers
Windows 2003 DNS Server Installation & Configurat…
DNS is used for translating host names to IP addresses and the reverse, for both private and public networks (i.e.: the Internet). DNS does this by u…
Featured Subcategories:
Virtualization & VM Backup Articles:

8 Critical Features to Have in a VM Backup Soluti…
Businesses that rely on virtual machines for their day-to-day operations should think twice about securing their infrastructure. Modern use of virtua…
6 Key Areas to Consider When Selecting a VM Backu…
Backup and Disaster recovery are core considerations for any business with an IT footprint, whether that is on-premises or in the cloud.
Your busine…
How to Enable SNMP on VMware ESXi Host & Configur…
In this article we will show you how to enable SNMP on your VMware ESXi host, configure SNMP Community string and configure your ESXi firewall to all…

Ultimate Guide: Install Windows 11 on VMware ESXi…
In this article, we’ll show you how to setup or install Microsoft Windows 11 on VMware’s ESXi servers and bypass the Trusted Platform Module version…
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Linux - Unix
The Linux Command Line
You could actually skip this whole section for those who are already familiar with the topic, but we highly recommend you read it because this is the hear…
Linux - Unix
Working with Linux TCP/IP Network Configuration Files
This article covers the main TCP/IP network configuration files used by Linux to configure various network services of the system such as IP Address, Defa…
Linux - Unix
Updating Your Linux Server - How to Update Linux Works…
Like any other software, an operating system needs to be updated. Updates are required not only because of the new hardware coming into the market, but al…
Linux - Unix
Linux File & Folder Permissions
File & folder security is a big part of any operating system and Linux is no exception!
These permissions allow you to choose exactly who can access…
Popular Topics

ManageEngine Firewall Analyzer
Master Your Firewall: 6 Expert-Backed Steps to Boost S…
In today’s evolving threat landscape, firewall audits are more than just a best practice—they're a critical line of defense. Regular audits ensure your fi…
Cisco Switches
VLAN Security Tips - Best Practices
This article focuses on VLAN Security and its implementation within the business network environment. We provide tips and Cisco CLI commands that will hel…
Cisco Switches
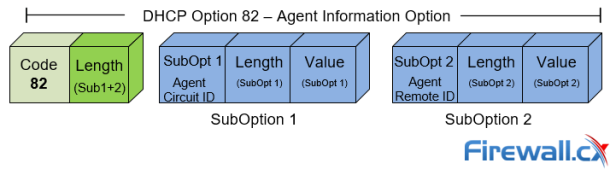
DHCP Option 82 Message Format, Analysis. DHCP Snooping…
This article provides in-depth analysis of DHCP Option 82 (DHCP Relay Agent) which is one of the +180 DHCP Options available to the DHCP protocol and used…
Cisco Routers
Configuring Cisco SSL VPN AnyConnect (WebVPN) on Cisco…
Our Web SSL VPN article written back in 2011 introduced this new wave of VPN services. This article extends the topic by covering the installation a…















