GFI EventsManager 7 Review
Imagine having to trawl dutifully through the event logs of twenty or thirty servers every morning, trying to spot those few significant events that could mean real trouble among that avalanche of operational trivia. Now imagine being able to call up all those events from all your servers in a single browser window and, with one click, open an event category to display just those events you are interested in…
Sounds good? Install this product, and you’ve got it.
A product of the well-known GFI stables, EventsManager 7 replaces their earlier LANguard Security Event Log Monitor (S.E.L.M.) which is no longer available. There’s also a Reporting Suite to go with it; but we haven’t reviewed that here.
In a nutshell the product enables you to collect and archive event logs across your organisation, but there’s so much more to it than that. It’s hard to condense the possibilities into a review of this size, but what you actually get is:
- Automatic, scheduled collection of event logs across the network; not only from Windows machines but from Linux/Unix servers too, and even from any network kit that can generate syslog output;
- The ability to group your monitored machines into categories and to apply different logging criteria to each group;
- One tool for looking at event logs everywhere. No more switching the event log viewer between servers and messing around with custom MMCs;
- The ability to display events by category or interest type regardless of where they occurred (for example just the Active Directory replication events, just the system health events, just the successful log-on events outside normal working hours);
- Automated response actions for particular events or types of events including alerting staff by email or pager or running an external script to deal with the problem;
- A back-end database into which you can archive raw or filtered events and which you can search or analyse against – great for legal compliance and for forensic investigation.
You can download the software from GFI’s website and, in exchange for your details, they’ll give you a thirty-day evaluation key that unlocks all the features; plenty of time to decide if it’s right for you. This is useful, because you do need to think about the deployment.
One key issue is the use of SQL-Server as the database back-end. If you have an existing installation you can use that if capacity permits, or you could download SQL Server Express from Microsoft. GFI do tell you about this but it’s hidden away in Appendix 3 of the manual, and an early section giving deployment examples might have been useful.
That said, once you get installed a handy wizard pops up to lead you through the key things you need to set up:

Here again are things you’ll need to think about – such as who will get alerted, how, when and for what, and what actions need to be taken.
You’ll also need to give EventsManager a user that has administrative access to the machines you want to monitor and perhaps the safest way to do this is to set up a new user dedicated to that purpose.
Once you’ve worked through the wizard you can add your monitored machines under the various categories previously mentioned. Ready-made categories allow you to monitor according to the type, function or importance of the target machine and if you don’t like those you can edit them or create your own.
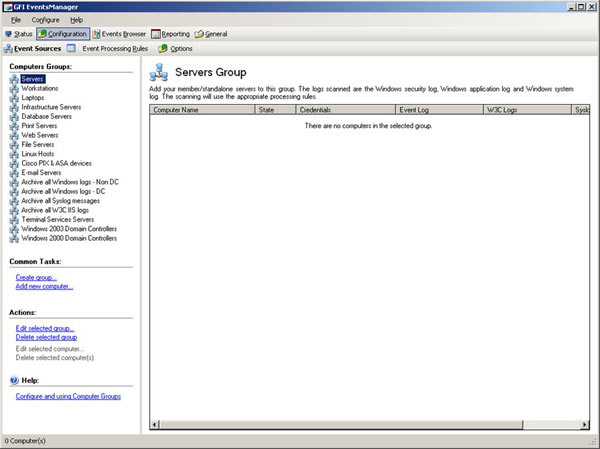
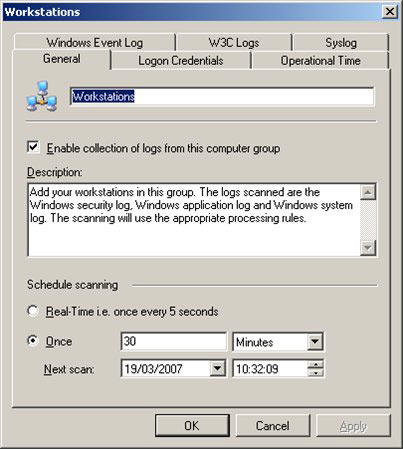
The categories are more than just cosmetic; each one can be set up to define how aggressively EventsManager monitors the machines, their ‘working week’, (useful for catching unauthorised out-of-hours activity) and the types of events you’re interested in (you might not want Security logs from your workstations, for example). Encouragingly though, the defaults provided are completely sensible and can be used without worry.
Once your targets are defined you’ll begin seeing logs in the Events Browser, and this is where the product really scores. To the left of the browser is a wealth of well-thought-out categories and types; click on one of these and you’ll see those events from across your enterprise. It’s as simple, and as wonderful as that.
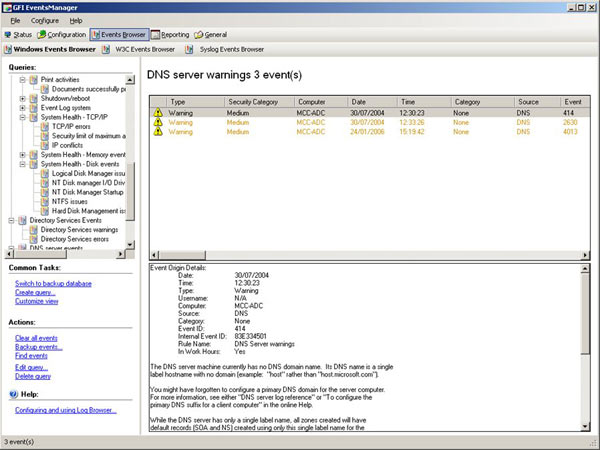
You can click on the higher-level categories to view, for example, all the SQL Server events, or you can expand that out and view the events by subcategory (just the Failed SQL Server Logons for example).
Again, if there are events of particular significance in your environment you can edit the categories to include them or even create your own, right down to the specifics of the event IDs and event types they collect. A particularly nice category is ‘Noise’, which you can use to collect all that day-to-day operational verbiage and keep it out of the way
For maximum benefit you’ll also want to assign actions to key categories or events. These can be real-time alerts, emails, corrective action scripts and log archiving. And again, you guessed it, this is fully customisable. The ability to run external scripts is particularly nice as with a bit of tweaking you can make the product do anything you like.

Customisation is one of the real keys to this product. Install it out of the box, just as it comes, and you’ll find it useful. But invest some time in tailoring it to suit your organisation and you’ll increase its value so much you’ll wonder how you ever managed without it.
In operation the product proved stable though perhaps a little on the slow side when switching between screens and particularly when starting up. This is a testimony to the fact that the product is doing a lot of work on your behalf and, to get the best from it, you really should give it a decent system to run on. The benefits you’ll gain will more than make up for the investment.
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!












