Suggested Articles:
Cisco Switches
Discover Features & Capabilities - Cisco Catalyst…
There’s a new switch around the block and its name is Catalyst 3850 – Cisco’s latest addition to its successful Catalyst series switches. The Cisco C…
Cisco Routers
Troubleshooting PPP Internet Connection On A Cisc…
The Point-to-Point Protocol is one of the most popular protocols around used by engineers, ISPs and companies around the globe for authentication of…
Cisco Switches
Cisco Catalyst Err-disabled Port State, Enable &…
Errdisable is a feature that automatically disables a port on a Cisco Catalyst switch. When a port is error disabled, it is effectively shut dow…
Cisco Services & Technologies
Cisco SmartCare Update - Next Generation Appliance
It's been more than a year since we introduced the Cisco SmartCare service and appliance. It's been extremely popular and has successfully penetrated…
Featured Subcategories:
Data Center Articles:
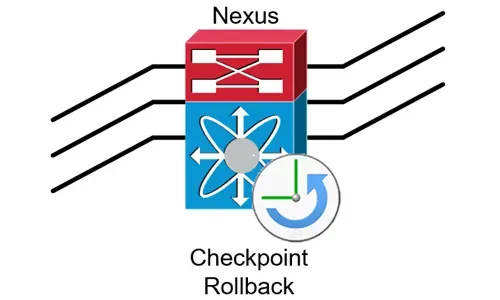
Complete Guide to Nexus Checkpoint & Rollback Fea…
The Cisco NX-OS checkpoint feature provides the capability to capture at any time a snapshot (backup) of the Cisco Nexus configuration…

NEXUS NX-OS: Useful Commands, CLI Scripting, Hint…
Whether you’re new to Cisco Nexus switches or have been working with them for years this article will show how to get around the Nexus NX-OS usi…

Introduction to Cisco Nexus Switches – Nexus Prod…
This article introduces the Cisco Nexus product family (Nexus 9000, Nexus 7000, Nexus 5000, Nexus 3000, Nexus 2000, Nexus 1000V and MDS 9000). We exp…

Join Australia’s First Official Cisco Data Center…
It’s a reality – Australia now has its own Official Cisco Data Center User Group (DCUG) and it’s growing fast! Originally inspired by Cisco Champions…
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Cisco Switches
Password Recovery / Password Reset Procedure for Catal…
This article shows how to reset a password on a Cisco Catalyst 3750-X (stacked or single unit) and Cisco Catalyst 3560-x switch without losing its startup…
Cisco Switches
Cisco Nexus 7000 Series Module Shutdown and Removal Pr…
This article explains the procedure that should be followed to correctly shutdown/powerdown a Cisco Nexus 7000 series module and remove it from the chassi…
Cisco Switches
Resolving Cisco Switch & Router ‘DHCP Server Pool Exha…
In previous articles, we showed how it is possible to configure a Cisco router or Catalyst switch to provide DHCP server services to network clients. Ever…
Cisco Switches
Spanning Tree BPDU Guard and Errdisable Interface Auto…
Running Spanning Tree Protocol (STP) in a large network environment can be a challenging task especially when features/enhancements such as BPDU Filter an…
Cisco Firewalls
Cisco ASA Firepower Threat Defense (FTD): Download and…
One Appliance – One Image is what Cisco is targeting for its Next Generation Firewalls. With this vision, Cisco has created a unified software image named…
Cisco Firewalls
Demystifying Cisco AnyConnect 4.x Licensing. Plus, Plu…
In late 2014, Cisco announced the new licensing model for the latest AnyConnect Secure Mobility client v4.x. With this new version, Cisco introduced a num…
Cisco Firewalls
Cisco ASA5500 (5505, 5510, 5520, etc) Series Firewall…
The Cisco ASA 5500 series security appliances have been around for quite some time and are amongst the most popular hardware firewalls available in the ma…
Cisco Firewalls
Understand & Configure NAT Reflection, NAT Loopback, H…
This article examines the concept of NAT Reflection, also known as NAT Loopback or Hairpinning, and shows how to configure a Cisco ASA Firewall running AS…
Popular Topics
Palo Alto Networks
Palo Alto Networks Firewall - Web & CLI Initial Config…
This article is the second-part of our Palo Alto Networks Firewall technical articles. Our previous article was introduction to Palo Alto Networks Firewal…
SASE & SD-WAN Networks
Configuring A SASE Unified Network: Data centers, Remo…
This article explores the need for Secure Access Service Edge (SASE) in today’s organizations. We show how one of the most advanced SASE platforms availab…
Palo Alto Networks
Palo Alto Firewall Application-based Policy Enforcemen…
Our previous article examined the benefits of Palo Alto Networks Firewall Single Pass Parallel Processing (SP3) architecture and how its combine with the…
Palo Alto Networks
Introduction to Palo Alto Next-Generation Network Fire…
During the past decade, we’ve seen the global IT security market flooded with new network security and firewall security appliances. New vendors emerging…
















