Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
|
Articles:
Firewall.cx Free Cisco Lab: Our Partners
| Read |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
Suggested Articles:

OpManager - Network Monitoring & Management
Elevate your network management: Maximizing effic…
As technology evolves, so do our networks. Today's sprawling network infrastructures are intricate ecosystems, demanding more from IT teams than ever…

ManageEngine Firewall Analyzer
Detecting Insider Threats and Shadow IT Through F…
This article explores the key indicators of insider threats and shadow IT hidden within firewall logs, the behavioral patterns security teams should…

OpManager - Network Monitoring & Management
AIOps for Modern IT Operations: Automating Monito…
The days of relying solely on static monitoring dashboards and manual firefighting are long gone. Today’s environments demand automation-first operat…
Network Protocol Analyzers
How to Reconstruct HTTP Packets/Data & Monitor HT…
HTTP reconstruction is an advanced network security feature offered by nChronos version 4.3.0 and later. nChronos is a Network Forensic Analysis appl…
Featured Subcategories:
WireShark Articles:
Detect Brute-Force Attacks with nChronos Network…
Brute-force attacks are commonly known attack methods by which hackers try to get access to restricted accounts and data using an exhaustive list/dat…
Introducing Colasoft Unified Performance Manageme…
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, quali…
How to Detect P2P (peer-to-peer) File Sharing, To…
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing process…
How to Detect Routing Loops and Physical Loops wi…
When working with medium to large scale networks, IT departments are often faced dealing with network loops and broadcast storms that are caused by u…
Wi-Fi Key Generator
Follow Firewall.cx
Recommended Downloads
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Palo Alto Networks
How to Fix Palo Alto Firewall “Error: Image File Authe…
Keeping your Palo Alto Firewall up to date with the latest PAN-OS software updates is an important step to ensure your organization is protected against t…

Palo Alto Networks
The Ultimate Guide to Palo Alto Networks Software NGFW…
Discover the ins and outs of using Palo Alto Networks’ Software NGFW (Flex) credits to seamlessly renew your cloud-based or virtualized software NGFW devi…
Palo Alto Networks
Palo Alto Firewalls Security Zones – Tap Zone, Virtual…
Palo Alto Networks Next-Generation Firewalls rely on the concept of security zones in order to apply security policies. This means that access lists (fire…
Palo Alto Networks
Introduction to Palo Alto Next-Generation Network Fire…
During the past decade, we’ve seen the global IT security market flooded with new network security and firewall security appliances. New vendors emerging…
Windows Servers
Installing Windows Server 2012 Active Directory via Se…
This article serves as an Active Directory tutorial covering installation and setup of a Windows 2012 Domain Controller using Windows Server Manager (GUI)…
Windows Servers
New Upcoming Features in Hyper-V vNext - Free Trainin…
With the release of Hyper-V vNext just around the corner, Altaro has organized a Free webinar that will take you right into the new Hyper-V vNext release…
Windows Servers
How to Install and Configure Windows 2012 DNS Server R…
Our previous article covered introduction to the Domain Name System (DNS) and explained the importance of the DNS Server role within the network infrastru…
Windows Servers
Windows 2016 Server Licensing Explained – Free Webinar
With Windows 2016 Server already making its way into data centers Windows 2016 Server Licensing is becoming a very hot topic. Windows 2016 Server is jam-p…
Popular Topics
VLAN Networks
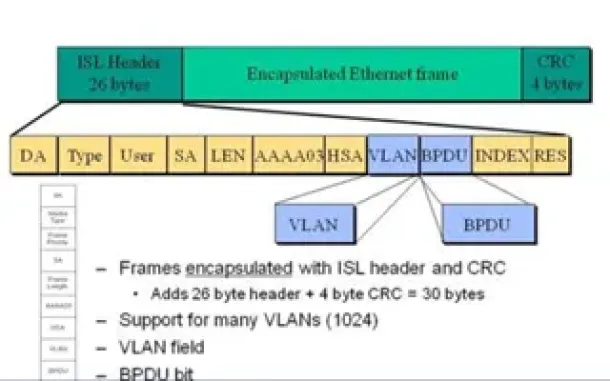
VLAN InterSwitch Link (ISL) Protocol Analysis
Deciding whether to use ISL or IEEE 802.1q to power your trunk links can be quite confusing if you cannot identify the advantages and disadvantages of eac…
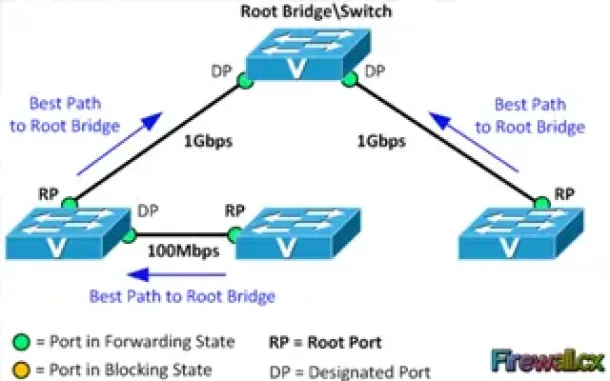
Spanning Tree Protocol (STP)
Spanning Tree Protocol – Part 2: Rapid STP Port Costs…
Spanning Tree Protocol, Rapid STP port costs and port states are an essential part of the STP algorithm that affect how STP decides to forward or block a…
Network Protocol Analyzers
Introducing Colasoft Unified Performance Management
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, quality, f…

Network Fundamentals
Securing Your Home Network
In today's world, securing your home network is more important than ever. With the increasing number of cyberattacks, data breaches, and online frauds, pr…
Cisco CallManager-CCME
Risk Management for Cisco Unified Communication Soluti…
As technology has advanced, things have become simpler yet more complex. One prime example is that of today’s communication networks. With the evolution o…
Cisco Switches
End-of-Sale and End-of-Life Announcement for the Cisco…
Cisco announces the end-of-sale and end-of-life dates for the Cisco Catalyst 3750G, 3560G, 3750-E, and 3560-E Series Switches. The last day to order the a…
Cisco CallManager-CCME
Cisco Unity Express Installation & Setup - ISM-SRE-300…
Unity Express is a popular add-on for Cisco Unified Communication Manager Express (CallManager Express) and Cisco Unified Communication Manager (CUCM), ad…
Cisco Services & Technologies
Comparing Cisco VPN Technologies – Policy Based vs Rou…
Virtual Private Networks constitute a hot topic in networking because they provide low cost and secure communications between sites (site-to-site VPNs) wh…

















