Suggested Articles:

ManageEngine Firewall Analyzer
Discover the Ultimate Firewall Management Tool:...
Firewall security management is a combination of monitoring, configuring, and managing your firewall to make sure it runs at its best to effectivel...
OpManager - Network Monitoring & Management
Network Management Systems Help Businesses Accu...
Accurately monitoring your organization’s business application performance, service provider SLA breaches, network infrastructure traffic, bandwidt...
Network Protocol Analyzers
How to Detect Routing Loops and Physical Loops ...
When working with medium to large scale networks, IT departments are often faced dealing with network loops and broadcast storms that are caused by...
Network Protocol Analyzers
How to Detect P2P (peer-to-peer) File Sharing, ...
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing proce...
Featured Subcategories:
WireShark Articles:
How to Perform TCP SYN Flood DoS Attack & Detec...
This article will help you understand TCP SYN Flood Attacks, show how to perform a SYN Flood Attack (DoS attack) using Kali Linux & hping3 and ...
How to Use Multi-Segment Analysis to Troublesho...
Troubleshooting network problems can be a very intensive and challenging process. Intermittent network problems are even more difficult to troubles...
How to Reconstruct HTTP Packets/Data & Monitor ...
HTTP reconstruction is an advanced network security feature offered by nChronos version 4.3.0 and later. nChronos is a Network Forensic Analysis ap...
How To Detect ARP Attacks & ARP Flooding With C...
ARP attacks and ARP flooding are common problems small and large networks are faced with. ARP attacks target specific hosts by using their MAC addr...
Your IP address:
18.222.111.24
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Palo Alto Networks
Palo Alto Networks Firewall - Web & CLI Initial Conf...
This article is the second-part of our Palo Alto Networks Firewall technical articles. Our previous article was introduction to Palo Alto Networks Firew...
Palo Alto Networks
The Benefits of Palo Alto Networks Firewall Single P...
What makes Palo Alto Networks Next-Generation Firewall (NGFW) so different from its competitors is its Platform, Process and Architecture. Palo Alto Net...
Palo Alto Networks
How to Register a Palo Alto Firewall and Activate Su...
This article explains how to register and activate your Palo Alto Firewall Appliance to obtain technical support, RMA hardware replacement, product upda...
Palo Alto Networks
Palo Alto Firewall Application-based Policy Enforcem...
Our previous article examined the benefits of Palo Alto Networks Firewall Single Pass Parallel Processing (SP3) architecture and how its combine with th...
Windows Servers
Windows 2012 Server Foundation, Essential, Standard ...
FREE Hyper-V & VMware Virtualization Backup: FREE for Firewall.cx readers for a Limited Time! Download Now!
Windows Server 2012 Edition...
Windows Servers
New Features in Windows Server 2012 - Why Upgrade t...
There is no doubt that Cloud Computing is hot topic these days. Innovations in cloud computing models have made every industry and company IT department...
Windows Servers
Creating a Virtual Machine in Windows Hyper-V. Confi...
Our previous articles covered basic concepts of Virtualization along with the installation and monitoring of Windows 2012 Hyper-V. This article takes th...
Windows Servers
Free Hyper-V eBook - Create, Manage and Troubleshoot...
With the introduction of Hyper-V on the Windows Server platform, virtualization has quickly become the de facto standard for all companies seeking to co...
Popular Topics
Network Protocol Analyzers
How to Use Multi-Segment Analysis to Troubleshoot Ne...
Troubleshooting network problems can be a very intensive and challenging process. Intermittent network problems are even more difficult to troubleshoot ...
Security Service Edge (SSE)
Security Service Edge (SSE) Limitations & Disadvanta...
This article explores the Security Service Edge (SSE) portion of Secure Access Service Edge (SASE) and the need for holistic cybersecurity protections.
...
Windows Servers
Windows 2012 Server NIC Teaming – Load Balancing/Fai...
NIC Teaming, also known as Windows Load Balancing or Failover (LBFO), is an extremely useful feature supported by Windows Server 2012 that allows the ag...
Routing
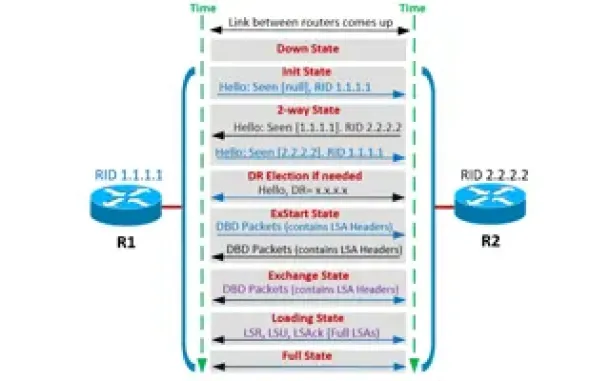
OSPF - Part 4: OSPF Neighbor States – OSPF Neighbor ...
This is the third article of our OSPF series which analyzes the different OSPF States routers go through during the OSPF discovery and neighbor forming ...
Cisco Routers
Troubleshooting PPP Internet Connection On A Cisco R...
The Point-to-Point Protocol is one of the most popular protocols around used by engineers, ISPs and companies around the globe for authentication of rem...
Cisco Wireless
Wireless (Wifi) WEP WPA WPA2 Key Generator
The Firewall.cx Wireless LAN Key Generator will allow the generation of a WEP or WPA ASCII based encryption key and will provide the equivalent HEX o...
Cisco Switches
Forcing A Cisco Catalyst Switch To Use 3rd Party SFP...
Many companies are seeking for Cisco SFP alternatives to help cut down the costs on these expensive modules.
A frequent customer problem with Cisco's n...

Cisco Data Center (Nexus/UCS)
Nexus 7000/7700 Software Upgrade via ISSU. Complete ...
This article shows how to perform an ISSU (In-Service Software Upgrade) on a Nexus Data Center switch (7000 and 7700 models) and avoid service and netwo...




















