-
 HornetSecurity
HornetSecurityAll-in-one protection for Microsoft 365
All-in-one protection for Microsoft 365
-
 ManageEngine
ManageEngineOpManager: Network & DC Monitoring
Monitor & Manage Network, Datacenters, endpoints & more.
-

Latest Articles
Challenges & Solutions to Managing Firewall Rules in Complex Network Environments
 In today's interconnected digital landscape, where businesses rely heavily on networked systems and the internet for their operations, the importance of cybersecurity cannot be overstated. Among the essential tools in a cybersecurity arsenal, firewalls stand as a frontline defense against cyber threats and malicious actors.
In today's interconnected digital landscape, where businesses rely heavily on networked systems and the internet for their operations, the importance of cybersecurity cannot be overstated. Among the essential tools in a cybersecurity arsenal, firewalls stand as a frontline defense against cyber threats and malicious actors.
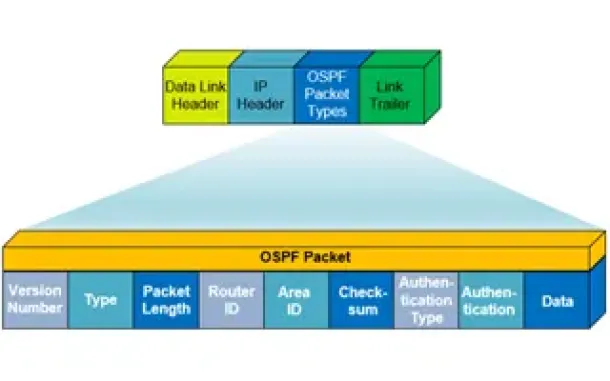
One of the primary functions of a firewall is to filter traffic, which entails scrutinizing packets of data to determine whether they meet the criteria set by the organization's security policies. This process involves examining various attributes of the data packets, such as source and destination IP addresses, port numbers, and protocols. By enforcing these rules, firewalls can thwart a wide range of cyber threats, including unauthorized access attempts, malware infections, denial-of-service attacks and more.
Enforcing and managing firewall rules effectively can be a daunting task, particularly in complex network environments with numerous rules, policies and configurations. While solutions like ManageEngine Firewall Analyzer step in, to offer a comprehensive way to streamline firewall rule management and enhance security posture, it’s worthwhile take a look at the real challenges firewall rule management present across all known platforms such as Cisco (FTD, Firepower, ASA), Palo AltoPalo Alto Next-Gen firewalls, Checkpoint, Fortinet, Juniper and more.
Key Topics:
- Challenges in Firewall Rule Management
- How to Simplify Firewall Rules
- The Benefits of Effective Firewall Rule Management
- Summary
Challenges with Firewall Rule Management
Configuring QoS on Palo Alto Firewalls: Class-based Policies, QoS Profiles, Enabling QoS on Firewall Interfaces
 This article’s purpose is to help you quickly master Palo Alto QoS concepts and learn to configure QoS on Palo Alto Firewalls in a simple and efficient way. QoS is considered a complicated topic however thanks to Palo Alto’s intuitive firewall GUI interface and our real-scenarios, you’ll quickly grasp all necessary QoS basics and be ready to implement your own QoS policies!
This article’s purpose is to help you quickly master Palo Alto QoS concepts and learn to configure QoS on Palo Alto Firewalls in a simple and efficient way. QoS is considered a complicated topic however thanks to Palo Alto’s intuitive firewall GUI interface and our real-scenarios, you’ll quickly grasp all necessary QoS basics and be ready to implement your own QoS policies!
You’ll learn basic QoS terms such as Ingress and Egress traffic, Differentiated Service Code Point (DSCP), Traffic Policing, Traffic Shaping, Palo Alto QoS Classes, Palo Alto QoS Policies, how to build Palo Alto QoS policies, how to configure Palo Alto QoS Classes and finally how to enable and monitor QoS on Palo Alto firewall interfaces (both standalone & AE Aggregate interfaces), view QoS bandwidth graphs and more!
Key Topics:
- Introduction to Palo Alto QoS
- Palo Alto QoS Classes
- Palo Alto QoS Policies
- Configuring QoS Class-based Policies & Profiles
- Enabling QoS on Palo Alto Firewall Physical & Aggregate (AE) Interfaces
- Summary
Find more great articles by visiting our Palo Alto Firewall Section.
Introduction to Palo Alto QoS
QoS was born from the IEEE group during 1995-1998 by establishing the standard IEEE 802.1P. The main purpose of QoS is to prioritise desired traffic over other type of traffic or to limit the amount of bandwidth applications can consume, by utilizing different mechanisms. This ensures network performance, avoids bottlenecks, congestion or overutilization of network links. A frequently used example of QoS is the prioritising Real-time traffic e.g voice or video, over other type of traffic:
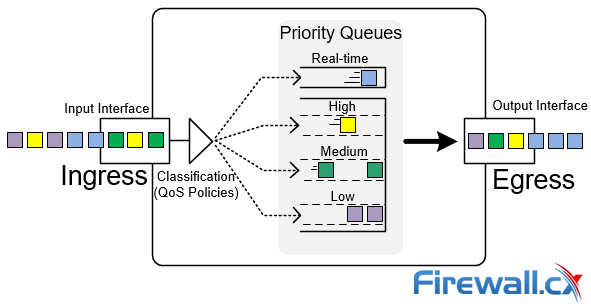 QoS Priority Queues - Packet classification and prioritization
QoS Priority Queues - Packet classification and prioritization
In the example above, voice packets (blue) are given a higher priority against others, therefore immediately being forwarded by the firewall out via the output interface. Since voice packets are very sensitive to delay, they are usually handled with priority to avoid issues in a real-time voice streams e.g VoIP telephone call between two endpoints.
Overview of QoS Configuration on Palo Alto Firewalls
Dealing with Security Audit Challenges: Discovering vulnerabilities, unauthorized access, optimize network security & reporting
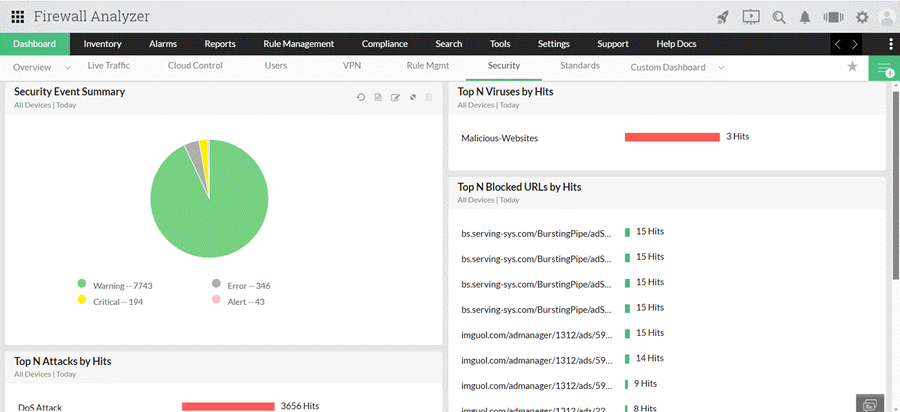
 The utilization of log analyzers, such as Firewall Analyzer, in network infrastructure plays a pivotal role in enhancing cybersecurity and fortifying the overall security posture of an organization. Security audits, facilitated by log analyzers, serve as a critical mechanism for systematically reviewing and analyzing recorded events within the network.
The utilization of log analyzers, such as Firewall Analyzer, in network infrastructure plays a pivotal role in enhancing cybersecurity and fortifying the overall security posture of an organization. Security audits, facilitated by log analyzers, serve as a critical mechanism for systematically reviewing and analyzing recorded events within the network.
This proactive approach enables the identification of potential security risks, unauthorized access attempts, and abnormal activities that might signify a breach. The log analyzer sifts through vast amounts of data & logs, providing insights into patterns and anomalies that might go unnoticed otherwise.
By uncovering vulnerabilities and irregularities, organizations can take timely corrective actions, preventing potential security breaches. Moreover, the information gleaned from these audits is instrumental in formulating a comprehensive security strategy that extends across the entire network infrastructure.
This strategic approach ensures a holistic defense against cyber threats, fostering a resilient and adaptive cybersecurity framework that aligns with the evolving landscape of security challenges.
This article will delve into the concept of security audits and how a product like Firewall Analyzer can streamline this crucial procedure.
Key Topics:
- Security Audits Explained
- Security Audit Challenges
- Tool for Effective Network Security Management
- Conducting a Security Audit with Firewall Analyzer
- Summary
Download your copy of ManageEngine's popular Firewall Analyzer here.
Security Audits Explained
How to Manually Download, Import & Install PAN-OS on Palo Alto Firewalls via CLI & Web GUI interface
 This article provides comprehensive guidance on the manual processes involved in downloading, uploading, and installing (import) any PAN-OS version on a Palo Alto Firewall. It details the steps for searching and downloading the desired PAN-OS version, as well as the supported methods for uploading the software to your Palo Alto Firewall, including Web, TFTP, and SCP. Additionally, the article offers valuable tips aimed at facilitating a smooth and successful upgrade process.
This article provides comprehensive guidance on the manual processes involved in downloading, uploading, and installing (import) any PAN-OS version on a Palo Alto Firewall. It details the steps for searching and downloading the desired PAN-OS version, as well as the supported methods for uploading the software to your Palo Alto Firewall, including Web, TFTP, and SCP. Additionally, the article offers valuable tips aimed at facilitating a smooth and successful upgrade process.
The necessity for a manual upgrade of a Palo Alto firewall arises in instances where the system operates within an isolated environment employing air-gap architecture and lacks direct internet access. This requirement is further applicable in scenarios where the firewall is devoid of valid licenses, remains unregistered, or serves as a replacement unit as exemplified in a Return Merchandise Authorization (RMA) context.
Whether performing upgrades manually or automatically, it is crucial to consider the same upgrade path rules outlined in our article Complete guide to upgrading Palo Alto firewalls. Individuals unfamiliar with these rules are strongly encouraged to review the article before initiating any PAN-OS upgrade.
Key Topics:
- Downloading PAN-OS Software
- Uploading PAN-OS Software Images to the Firewall
- Verifying Uploaded PAN-OS Software Images (GUI & CLI)
- Installing PAN-OS Software Images
- Summary
Explore our dedicated Palo Alto section to access a collection of high-quality technical articles.
Downloading PAN-OS Software
Begin by downloading the needed software from the Palo Alto Networks support page. Make sure you have a valid support contract.
Once logged in, select Updates on the left pane, followed by Software Updates from the right pane:
Your IP address:
18.216.32.116
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Featured Categories:
Top Picks:
Understanding Deduplication. Complete Guide to ...

Dealing with Security Audit Challenges: Discove...
Free Webinar: Enterprise-Grade Security and Man...

How to Manually Download, Import & Install PAN-...
Key Features of a True Cloud-Native SASE Service. Setting the Right Expectations
Check Point Software and Cato Networks Co-Founder Shlomo Kramer Shares His Journey: From ‘Firewall-1’ Software to Today’s Firewall as a Service
SASE and VPNs: Reconsidering your Mobile Remote Access and Site-to-Site VPN strategy
The Most Common Worst Networking Practices and How To Fix Them

VLANs - Access & Trunk Links
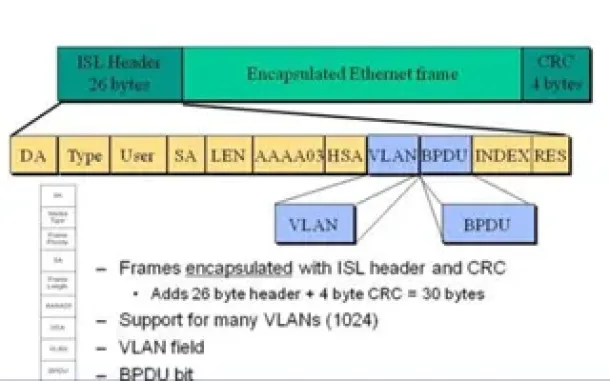
VLAN InterSwitch Link (ISL) Protocol Analysis

VLAN Tagging - Understanding VLANs Ethernet Frames

InterVLAN Routing - Routing between VLAN Networks

Enhanced Interior Gateway Routing Protocol - EIGRP
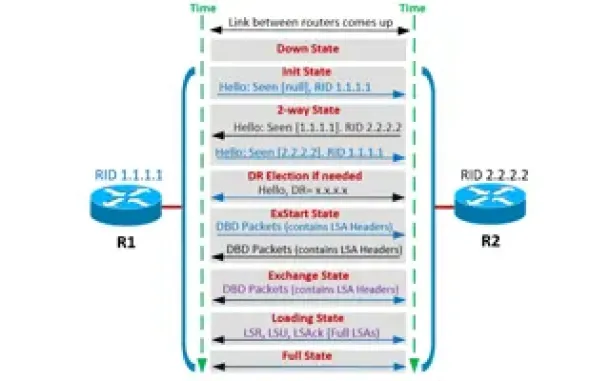
OSPF - Part 4: OSPF Neighbor States – OSPF Neighbor Forming Process
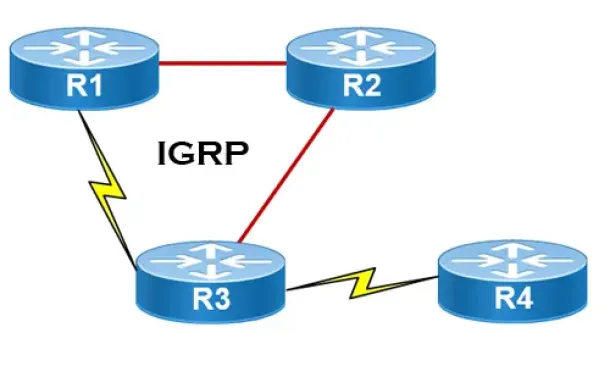
Interior Gateway Protocol - IGRP