Articles
To read the articles in this section, simply click on the article title or read button on the far right (if visible).
Use the below filters to customise the number of articles displayed or search for specific title topics/keywords.
| Articles | |
|---|---|
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
| Read | |
Suggested Articles:

ManageEngine Firewall Analyzer
Dealing with Security Audit Challenges: Discove...
The utilization of log analyzers, such as Firewall Analyzer, in network infrastructure plays a pivotal role in enhancing cybersecurity and fortifyi...
Network Protocol Analyzers
How to Use Multi-Segment Analysis to Troublesho...
Troubleshooting network problems can be a very intensive and challenging process. Intermittent network problems are even more difficult to troubles...

ManageEngine Firewall Analyzer
Ensuring Compliance and Business Continuity in ...
In the wake of digital transformation, the work landscape as we know it has undergone a dynamic shift. People can now work from home, from the offi...
Network Protocol Analyzers
Detect Brute-Force Attacks with nChronos Networ...
Brute-force attacks are commonly known attack methods by which hackers try to get access to restricted accounts and data using an exhaustive list/d...
Featured Subcategories:
WireShark Articles:
How To Detect ARP Attacks & ARP Flooding With C...
ARP attacks and ARP flooding are common problems small and large networks are faced with. ARP attacks target specific hosts by using their MAC addr...
Advanced Network Protocol Analyzer Review: Cola...
Firewall.cx has covered Colasoft Capsa several times in the past, but its constant improvements make it well worth revisiting. Since the last revie...
How to Detect Routing Loops and Physical Loops ...
When working with medium to large scale networks, IT departments are often faced dealing with network loops and broadcast storms that are caused by...
How to Use Multi-Segment Analysis to Troublesho...
Troubleshooting network problems can be a very intensive and challenging process. Intermittent network problems are even more difficult to troubles...
Your IP address:
3.144.116.159
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Palo Alto Networks
How to Fix Palo Alto Firewall “Error: Image File Aut...
Keeping your Palo Alto Firewall up to date with the latest PAN-OS software updates is an important step to ensure your organization is protected against...
Palo Alto Networks
Palo Alto Firewalls Security Zones – Tap Zone, Virtu...
Palo Alto Networks Next-Generation Firewalls rely on the concept of security zones in order to apply security policies. This means that access lists (fi...
Palo Alto Networks
Palo Alto Firewall Application-based Policy Enforcem...
Our previous article examined the benefits of Palo Alto Networks Firewall Single Pass Parallel Processing (SP3) architecture and how its combine with th...
Palo Alto Networks
Palo Alto Networks Firewall - Web & CLI Initial Conf...
This article is the second-part of our Palo Alto Networks Firewall technical articles. Our previous article was introduction to Palo Alto Networks Firew...
Windows Servers
Installing Windows Server 2012 Active Directory via ...
This article serves as an Active Directory tutorial covering installation and setup of a Windows 2012 Domain Controller using Windows Server Manager (GU...
Windows Servers
Hyper-V Best Practices - Replica, Cluster, Backup Ad...
Hyper-V has proven to be a very cost effective solution for server consolidation. Evidence of this is also the fact that companies are beginning to move...
Windows Servers
The Importance of a Hyper-V & VMware Server Backup T...
Using Hyper-V Server virtualization technology, you can virtualize your physical environment to reduce the cost of physical hardware. As part of IT best...
Windows Servers
How to Install Windows Server 2012 from USB Flash – ...
Most would remember the days we had to have a CDROM or DVDROM in order to proceed with the installation of an operating system. Today, it is very common...
Popular Topics
Virtualization & VM Backup
The Backup Bible. A Free Complete Guide to Disaster ...
The Free Backup Bible Complete Edition written by backup expert and Microsoft MVP Eric Siron, is comprised of 200+ pages of actionable content divided i...
Routing
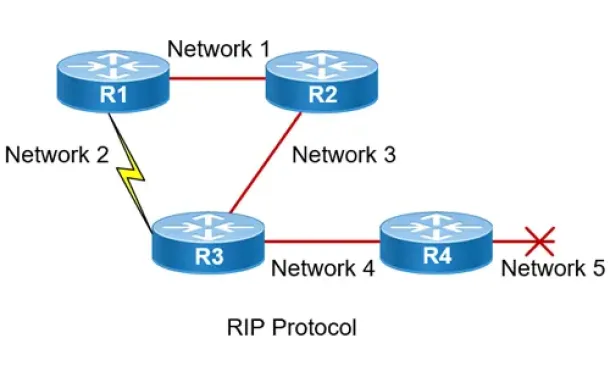
Routing Information Protocol - RIP
Routing Information Protocol (RIP) is a distance-vector routing protocol that is commonly used in small to medium-sized networks. It is one of the...
Windows Servers
How to Install and Configure SNMP for Windows Server...
Simple Network Management Protocol (SNMP) is a UDP protocol that uses port 161 to monitor and collect detailed information on any network device support...
Routing
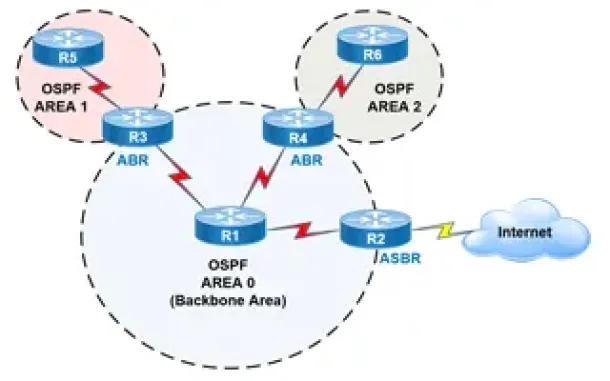
OSPF - Part 2: How OSPF Protocol Works & Basic Conce...
This article covers basic OSPF concepts and operation. We explain how OSPF works, how OSPF tables are built on an OSPF-enabled router and their purpose ...
Cisco CallManager-CCME
How to Register Cisco IP Phones & Connect CallManage...
This article shows how to connect Cisco's Unified CallManager with a CallManager Express system (including UC520, UC540 and UC560) via H323 gateway, all...
Cisco Data Center (Nexus/UCS)
NEXUS NX-OS: Useful Commands, CLI Scripting, Hints &...
Whether you’re new to Cisco Nexus switches or have been working with them for years this article will show how to get around the Nexus NX-OS using ...
Cisco Switches
How to Disable or Enable the Password Recovery Proce...
Our previous article shows how to perform a password recovery on the Cisco Catalyst switches. This article will now explain how to disable or enable the...
Cisco Routers
Configuring Dynamic NAT (NAT Overload) On A Cisco Ro...
NAT (Network Address Translation) is a method that allows the translation (modification) of IP addresses while packets/datagrams are traversing the netw...



















