Suggested Articles:
Network Protocol Analyzers
How to Use Multi-Segment Analysis to Troublesho...
Troubleshooting network problems can be a very intensive and challenging process. Intermittent network problems are even more difficult to troubles...
Network Protocol Analyzers
Introducing Colasoft Unified Performance Manage...
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, qua...

ManageEngine Firewall Analyzer
Dealing with Security Audit Challenges: Discove...
The utilization of log analyzers, such as Firewall Analyzer, in network infrastructure plays a pivotal role in enhancing cybersecurity and fortifyi...
OpManager - Network Monitoring & Management
Ensuring Enterprise Network Readiness for Mobil...
Demands for Enterprise networks to properly support mobile users is on a continuous rise making it more than ever necessary for IT departments to p...
Featured Subcategories:
WireShark Articles:
How To Detect ARP Attacks & ARP Flooding With C...
ARP attacks and ARP flooding are common problems small and large networks are faced with. ARP attacks target specific hosts by using their MAC addr...
How to Detect P2P (peer-to-peer) File Sharing, ...
Peer-to-Peer file sharing traffic has become a very large problem for many organizations as users engage in illegal (most times) file sharing proce...
Introducing Colasoft Unified Performance Manage...
Colasoft Unified Performance Management (UPM) is a business-oriented network performance management system, which analyzes network performance, qua...
Advanced Network Protocol Analyzer Review: Cola...
Firewall.cx has covered Colasoft Capsa several times in the past, but its constant improvements make it well worth revisiting. Since the last revie...
Your IP address:
3.141.30.162
Wi-Fi Key Generator
Follow Firewall.cx
Cisco Password Crack
Decrypt Cisco Type-7 Passwords on the fly!
Palo Alto Networks
Palo Alto Firewall Configuration Options. Tap Mode, ...
Our previous article explained how Palo Alto Firewalls make use of Security Zones to process and enforce security policies. This article will explain th...
Palo Alto Networks
How to Register a Palo Alto Firewall and Activate Su...
This article explains how to register and activate your Palo Alto Firewall Appliance to obtain technical support, RMA hardware replacement, product upda...
Palo Alto Networks
Introduction to Palo Alto Next-Generation Network Fi...
During the past decade, we’ve seen the global IT security market flooded with new network security and firewall security appliances. New vendors emergin...
Palo Alto Networks
Complete Guide: Configuring IPSec VPN between Palo A...
This article will show you how to configure an IPSec VPN tunnel between a Palo Alto firewall (all PANOS versions) and Meraki MX security appliance. Our ...
Windows Servers
Easy, Fast & Reliable Hyper-V & VMware Backup with A...
As more companies around the world adopt the virtualization technology to increase efficiency and productivity, Microsoft’s Hyper-V virtualization platf...
Windows Servers
Installing Active Directory Services & Domain Contro...
This article serves as an Active Directory tutorial covering installation and setup of Windows 2012 Active Directory Services Role & Domain Controll...
Windows Servers
The Importance of a Hyper-V & VMware Server Backup T...
Using Hyper-V Server virtualization technology, you can virtualize your physical environment to reduce the cost of physical hardware. As part of IT best...
Windows Servers
Introduction to Windows DNS – The Importance of DNS ...
The Domain Name System (DNS) is perhaps one of the most important services for Active Directory. DNS provides name resolution services for Active Direct...
Popular Topics

Routing
Enhanced Interior Gateway Routing Protocol - EIGRP
Enhanced Interior Gateway Routing Protocol (EIGRP), similar to IGRP, is a Cisco proprietary routing protocol that is used to exchange routing informatio...
Windows Servers
Installing Windows Server 2012 Active Directory via ...
This article serves as an Active Directory tutorial covering installation and setup of a Windows 2012 Domain Controller using Windows Server Manager (GU...
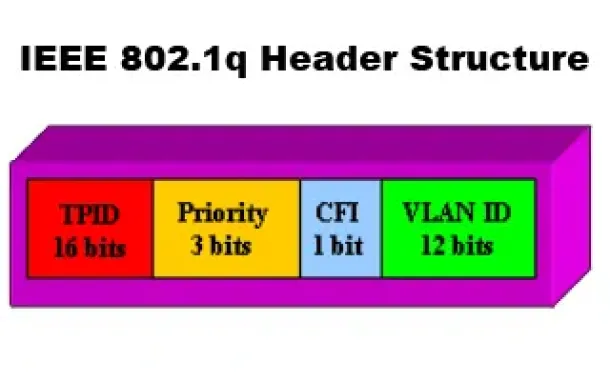
VLAN Networks
VLANs - IEEE 802.1q Trunk Link Protocol Analysis
While the VLAN Tagging article briefly covered the IEEE 802.1q protocol this article will continue building upon it by further analyzing the IEEE 802.1q...
Windows Servers
Renaming Windows 2000 Domain Name
Sometimes renaming a domain is an essential business requirement. There are many situations, such as mergers, change of company name or migration from a...
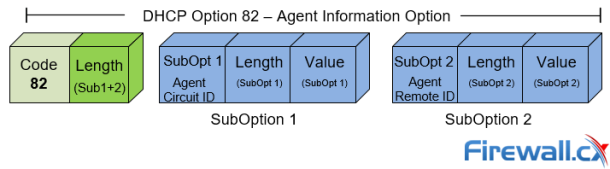
Cisco Switches
DHCP Option 82 Message Format, Analysis. DHCP Snoopi...
This article provides in-depth analysis of DHCP Option 82 (DHCP Relay Agent) which is one of the +180 DHCP Options available to the DHCP protocol and us...
Cisco Data Center (Nexus/UCS)
Complete Guide to Nexus Checkpoint & Rollback Featur...
The Cisco NX-OS checkpoint feature provides the capability to capture at any time a snapshot (backup) of the Cisco Nexus configuration be...

Cisco Data Center (Nexus/UCS)
Nexus 7000/7700 Software Upgrade via ISSU. Complete ...
This article shows how to perform an ISSU (In-Service Software Upgrade) on a Nexus Data Center switch (7000 and 7700 models) and avoid service and netwo...
Cisco Routers
Configuring Policy-Based Routing (PBR) with IP SLA T...
What is Policy-Based Routing?
Policy-Based Routing (PBR) is a very popular feature in Cisco routers, it allows the creation of policies that can select...




















